| Pixelfed | https://pixelfed.social/schlamar |
@schlamar
- 7 Followers
- 64 Following
- 756 Posts
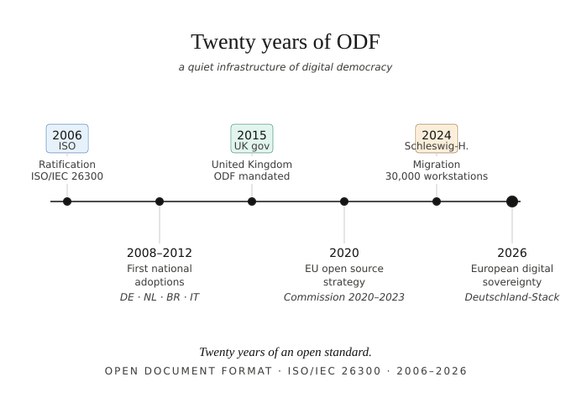
An open letter to office suite users, just before the Euro-Office announcement
https://blog.documentfoundation.org/blog/2026/06/08/an-open-letter/
RE: https://nileane.fr/@nileane/116704285750838861
If you’re still using Proton mail:
The company is sponsoring the videos of French far-right / fascist YouTuber Vincent Lapierre.
If encryption is part of your vision for a better society, find a better service provider.
UPDATE 2026-06-08: Response from Proton. This comes after mods apparently deleted lots of critical posts in r/ProtonMail.
https://www.reddit.com/r/ProtonMail/comments/1u05xs2/comment/oqgihvq/
John Finnemore on the French horn/cor anglais:
"I was idly wondering why the cor anglais has a French name meaning ‘English horn’, and the French horn has an English name meaning… well, ‘French horn’. I looked it up, even though I knew there would just be some reasonable but rather dull explanation.
"There isn’t. There is a completely bonkers explanation, in both cases. Here’s the first.
"So. The cor anglais isn’t English, or French. But that’s nothing, because another thing it isn’t is… a horn. It’s basically an overgrown oboe, and it’s from Silesia. But being thin with a bulb on the end, it looks a little like the trumpets angels are shown playing in medieval art.
"Or at least it did to the Germans, who started calling it the Engellisches Horn, or angel’s horn. Can you see the hilarious misunderstanding that’s about to happen? Well, that happened. The Italians thought the Germans called it the English Horn, so they translated it to corno inglese. The French got it from the Italians, and called it the cor anglais. The British got it from the French, and presumably stared at it, thought ‘We can’t call that an English horn! It’s nothing to do with us, we’ve only just this minute seen one!’ …and I suppose decided just to keep the French name to save embarrassment.
"But that is rationality itself compared to what happened with the “French” horn.
"Right. The French horn. It isn’t French, or English… but it is a horn. So that’s something. (In fact, horn players just call it ‘the horn’, and they wish you would too, but they can’t make you.) This story is simpler than the cor anglais one, but even more gloriously stupid.
"The French were famous for making beautiful hunting-horn type horns: curly tubes that made a nice noise when you blew through them. Then the Germans came up with a more complicated horn with slides and crooks and valves and what-have-you. So British horn players started calling the horns they played in orchestras French Horns, to make it clear they were having nothing to do with those funny looking new German horns with all the bits hanging off them. But the thing is… slides and crooks and valves and what-have-you are a really good idea. You can play tunes with them and everything. So, before long, in a brilliantly British combination of ruthless pragmatism and equally ruthless face-saving, British horn players were playing German horns… but still calling them French horns.
"In summary then: the cor anglais, or English horn, is a Silesian oboe that the Italians thought the Germans thought was English, but the Germans actually thought looked angelic. Whereas the French horn is a German horn that the British called the French horn to distinguish it from the German horn… which is what it is.
"All clear? Good. Carry on."
A voice from the back of the room piped up, "Yeah, right."
Almost 25 years ago, I wrote a blog post with the title ‘jumping ship slowly’ about leaving Windows (XP was awful, it was mind boggling to me that Vista managed to make people nostalgic for XP). My advice remains the same:
Don’t try switching OS first. The OS is the most easily replaceable bit in the stack. Switch applications first. Most ‘Linux’ apps are cross platform. They’ll run on Windows, and the few that don’t will run in WSL2. You can switch out apps one at a time, and take the time to get comfortable with the alternatives.
Once you’re comfortable not using any Windows-only apps, changing the OS but using all of the same applications is very easy to do. Changing OS and application stack at the same time is an enormous obstacle.
I believe this is also why a lot of corporate and government Linux migrations fail: they try to change everything at the same time and that’s too steep a learning curve.
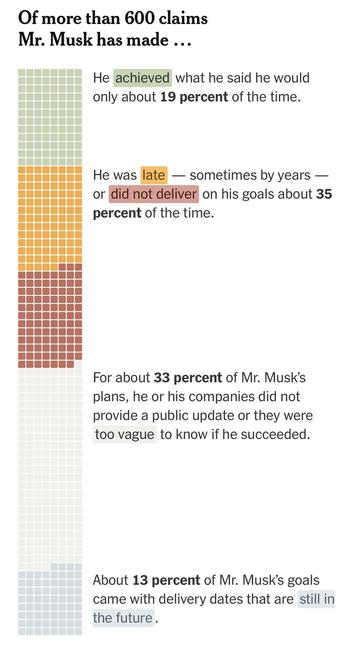
Student: “So Elon Musk is a trillionaire?”
Me: “Yup.”
Student: “How did he get that much money?”
Me: “Well, he doesn’t really have a trillion dollars cash. He just owns a lot of stock in companies that are valued at a trillion dollars.”
Student: “So those companies make huge profits?”
Me: “Oh gosh no. They all lose billions of dollars a year. All of them. Huge losses.”
The Economist headline: “Gen Z Mysteriously Hates Capitalism and No One Can Figure Out Why.”
RE: https://infosec.exchange/@cR0w/116692776221622923
Last year I said this, and it's still true.
"If there's one thing I've learned about covering cybersecurity over the past decade or so, is that the cybersecurity community (the fixers and breakers) and the cybersecurity industry (profits above all else) are two very, very different things."
https://queue.acm.org/detail.cfm?id=3807963 is some meta research trying to put AI for software development in proper perspective.
(Disclaimer: I went to school w/ one of the authors but I found the paper on my own.)