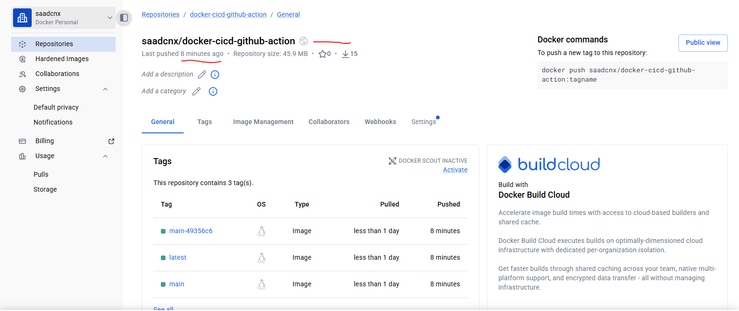
Automated Docker CI/CD with GitHub Actions
Just deployed a production-grade pipeline for a Node.js microservice.
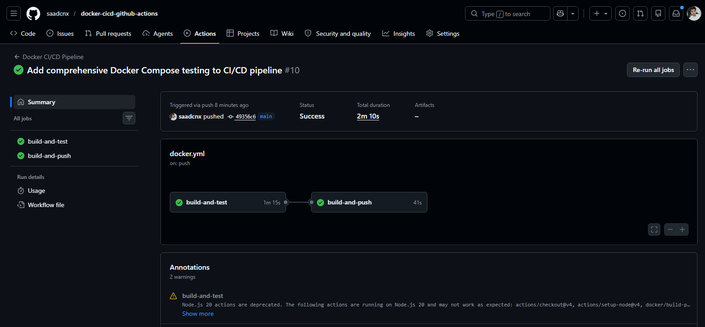
CI Engine: GitHub Actions with custom YAML workflows.
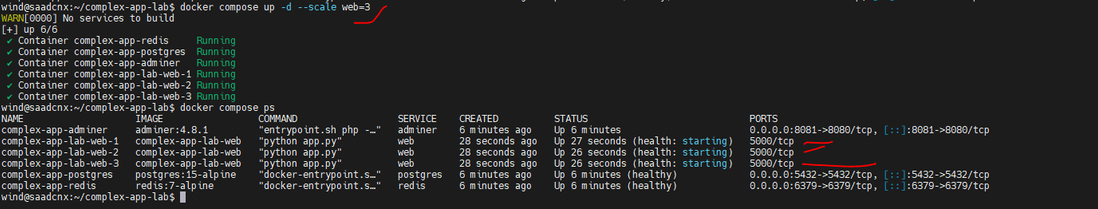
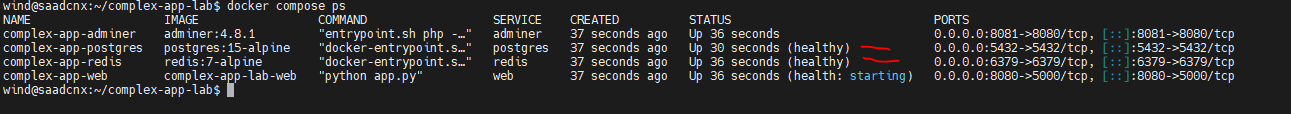
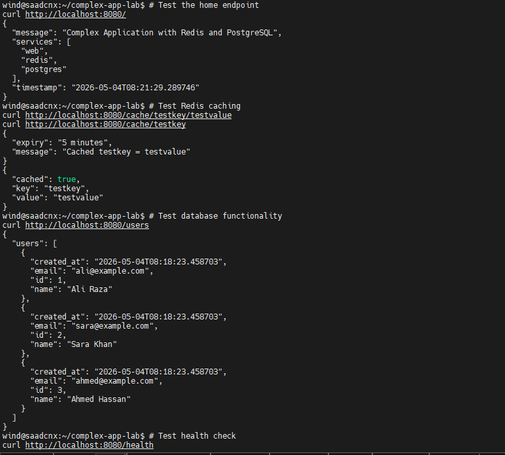
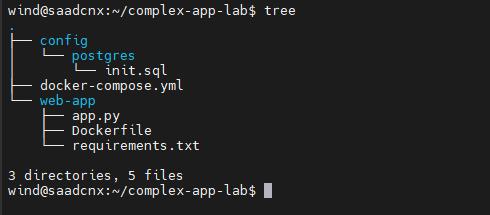
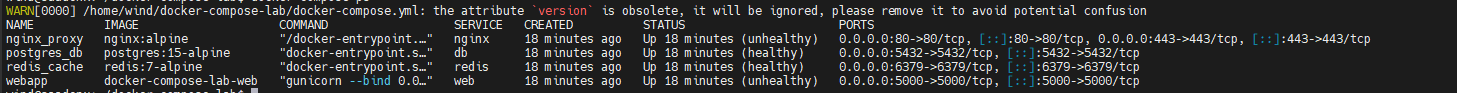
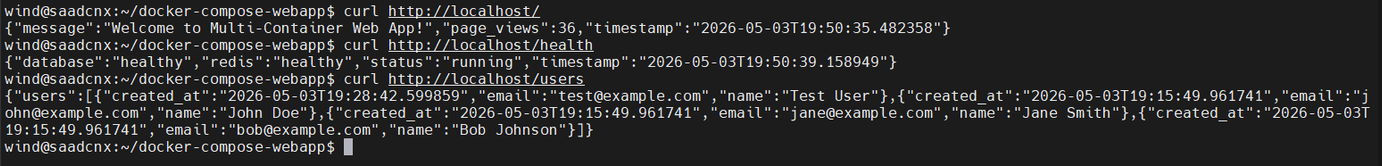
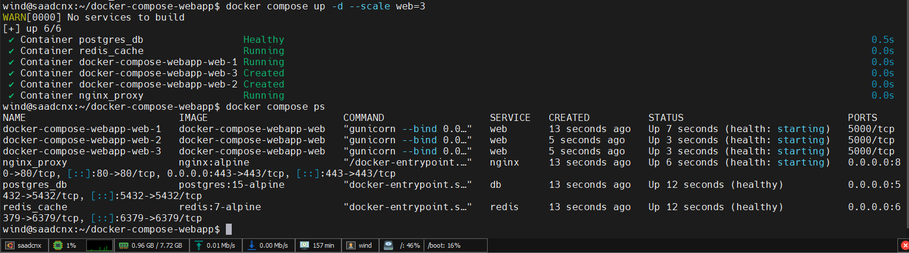
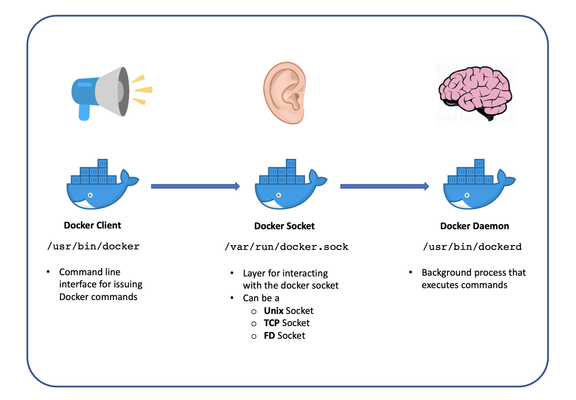
Testing: Integrated Docker Compose to simulate multi-container environments (App + Nginx) during the CI phase.
The pipeline ensures only verified, healthy images reach Docker Hub.
Github :- https://github.com/saadcnx/docker-cicd-github-actions