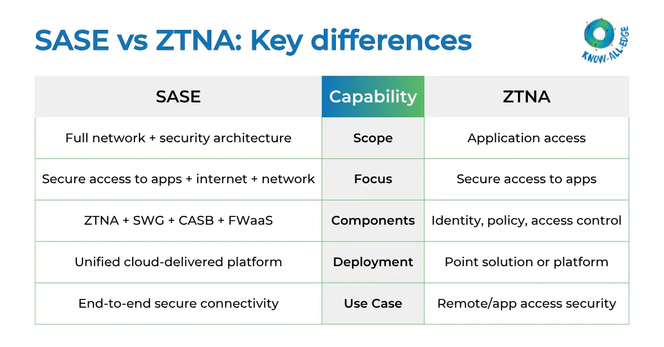
SASE vs ZTNA, what’s the difference?
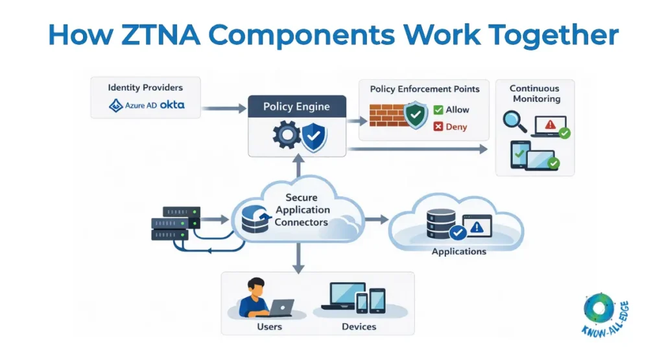
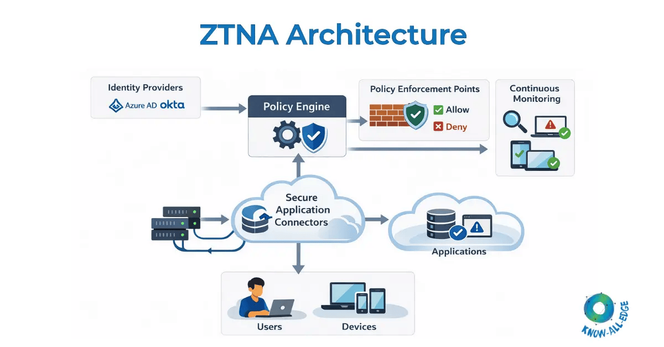
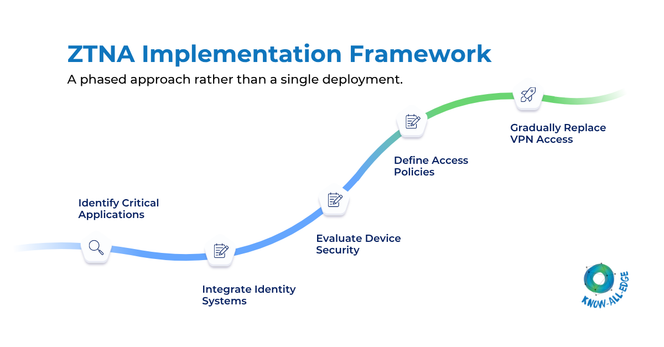
This visual simplifies how SASE delivers a unified, cloud-native security stack, while ZTNA enables secure, identity-based access to applications. A quick guide for IT leaders evaluating Zero Trust, secure remote access, and modern cybersecurity architecture.
#SASE #ZTNA #ZeroTrust #CyberSecurity #NetworkSecurity #CloudSecurity #SecureAccess