Still relying on VPN for remote access? It’s time to move to Zero Trust.
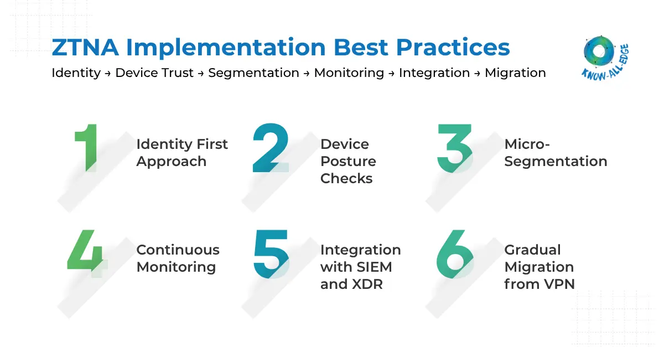
This infographic highlights key ZTNA best practices—identity-first access, device posture checks, micro-segmentation, continuous monitoring, and SIEM/XDR integration.
A practical approach to reduce attack surface and enable secure, scalable access for modern enterprises.
#ZTNA #ZeroTrust #CyberSecurity #NetworkSecurity #SecureAccess #VPNReplacement