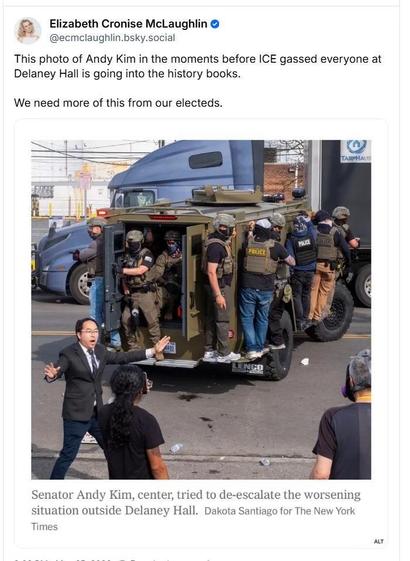
RE: https://mstdn.social/@PamelaBarroway/116639080558038766
Follow-up to my earlier post about #NewJersey Senator #AndyKim, who was pepper-sprayed by #ICE at the #DelaneyHall Detention Center in Newark on Monday.
This jaw-dropping photo shared with me shows the moment before ICE actually pepper-sprayed Kim, when he was trying to bring the temperature down. One for the ages.
I'm going call his office again right now. How lucky are we in NJ to have such representation?
Also, #fuckICE.