icrawler
- 16 Followers
- 162 Following
- 13 Posts
@soatok
I feel you and admire your resolve for all these pro bono works you're doing.. Also your adventures ;) keep me moving forward and endure as well, so thank you.
i.e. I recently discovered that some SDK includes a home grown crypto protocol that basically allows a related-key attack... (at that the 'crypto' part was missing in docs thus not easily findable via threat modeling process) It took weeks to persuade a responsible party to seek an independent consultation to confirm my finding , while an initial response was that they don't want to waste precious resources to beautify the code. And I didn't seek neither money nor fame, just wanted to make the world a better place ;)
Also in Russia there's a similar database, https://bdu.fstec.ru/vul (root cert is issued by Russian domestic CA, thus won't be trusted by most of the browsers)
Yes, you're right, sorry for my loose wording: strict QKD (like in BB84) is a two-party thing (I remember seeing some papers about quantum key agreement on groups, but never heard them being implemented).
I asked about systems with decryption of a minted key by the mentioned middleware ;) (thus huge attack surface) with compensating controls in form of some other -- PQC or classic symmetric -- crypto (thus complexity due to such "hybrid" -- as on Soatok's blog -- crypto construction)
Curious, do you have an ELI5 explanation against a QKD setup for more than a pair of nodes?
NIST's arguments against QKD are concise and fine (overall complexity, huuuuge attack surface, ..) but they usually require some time to explain..
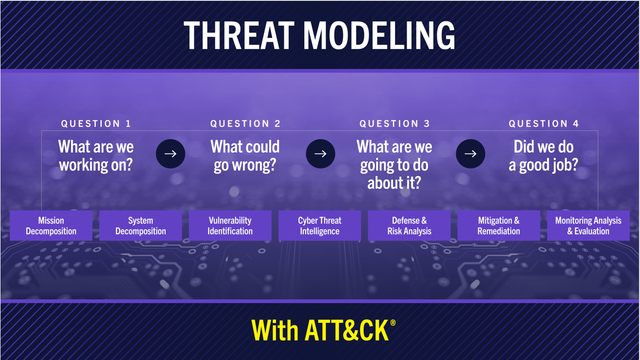
For Threat Model Thursday, let’s look at Threat Modeling with ATT&CK from MITRE. As always with Threat Model Thursday, my goal is to respectfully engage with interesting work and ask what we can learn from it. This one is particularly interesting because I’ve been teaching threat modeling with kill chains, including ATT&CK, for many years.
First, it’s incredibly nice to see an overview graphic, and nice to see another system that adpots the Four Question Framework, and has a condensed view up front of what you need to know.
(1/6 or read the blog https://shostack.org/blog/mitre-attack-threat-modeling-threat-model-thursday/)
(required computations cannot be performed and cannot be parallelized -- except running a few instances)
and the Grover's search algorithm is the best one -- there was a proof for that..
Security (Evaluation Criteria) - Post-Quantum Cryptography | CSRC | CSRC
Call for Proposals 4.A Security The security provided by a cryptographic scheme is the most important factor in the evaluation. Schemes will be judged on the following factors: 4.A.1 Applications of Public-Key Cryptography NIST intends to standardize post-quantum alternatives to its existing standards for digital signatures (FIPS 186) and key establishment (SP 800-56A, SP 800-56B). These standards are used in a wide variety of Internet protocols, such as TLS, SSH, IKE, IPsec, and DNSSEC. Schemes will be evaluated by the security they provide in these applications, and in additional applications that may be brought up by NIST or the public during the evaluation process. Claimed applications will be evaluated for their practical importance if this evaluation is necessary for deciding which algorithms to standardize. 4.A.2 Security Definition for Encryption/Key-Establishment NIST intends to standardize one or more schemes that enable “semantically secure” encryption or key encapsulation with respect to...