| Blog | https://www.freddieleeman.nl |
| @freddieleeman | |
| Project | https://learnDMARC.com |
| Project | https://URIports.com |
| Project | https://SmartHomeGeeks.io |
Freddie Leeman
- 63 Followers
- 14 Following
- 249 Posts
https://www.uriports.com/blog/google-simplifies-its-spf-record/

Google simplifies its SPF record and that is good news for everyone
At the start of December 2025, Google quietly made a meaningful change to the SPF record published at _spf.google.com. While the change may look subtle at first glance, it has clear benefits for anyone relying on Google in their own SPF configuration. A short history of Google’s
The new BIMI lps= tag, also known as the local-part selector, has been added to the BIMI specification. It allows domain owners to define different brand indicators based on the sender address (for example noreply@, support@, marketing@), without relying solely on the selector header.
With lps=, brands can assign unique BIMI logos to different sender types, exclude certain local-parts from showing any logo at all, and gain far more control over how their brand appears in recipients’ inboxes.
https://www.uriports.com/blog/bimi-lps-tag/
#BIMI #EmailAuthentication #DMARC #BrandProtection #URIports #EmailSecurity
Understanding the new lps= tag in BIMI
The BIMI specification continues to evolve, and one of the most notable changes in draft version 11 is the introduction of the new lps= tag, also known as the local-part selector. What is the lps= tag? In prior versions of BIMI, published brand indicators and their DNS assertion records relied
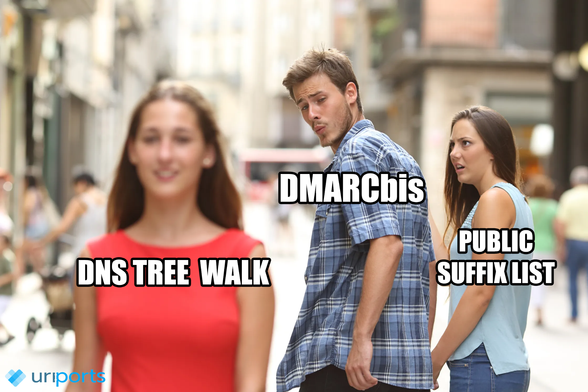
DMARCbis replaces the PSL with DNS Tree Walk: What's the Difference? https://www.uriports.com/blog/dmarcbis-dns-tree-walk/
DMARCbis Replaces the PSL with DNS Tree Walk: What's the Difference?
A central concept in DMARC is the Organizational Domain. It plays two key roles: 1. It defines the fallback domain used to look up a DMARC policy when no DMARC record is found at the exact domain from the "From" header. 2. It provides the domain against which relaxed alignment
Ever wonder what email servers are doing behind the scenes? At https://LearnDMARC.com, we turned the confusing world of email authentication into a visual story.
📡 Watch servers talk it out.
🎯 Take the DMARC quiz.
📬 Paste email headers.
Perfect for learners, IT pros, and anyone who’s ever yelled “WHY is SPF failing?!” Best of all? It’s free, and your data isn’t stored or used for anything beyond creating the visualization.
#EmailSecurity #DMARC #LearnDMARC #EmailAuthentication #SPF #DKIM #URIports
Google DMARC reports are back! After going quiet since April 13, Google has resumed sending DMARC aggregate reports as of 19:15 UTC today. So far, the reports only include data from yesterday (April 16), but it is a good sign that things are starting to flow again.
Being deeply involved into Email Authentication in Germany we did some research on the state of DMARC in .de. I’ve written a summary in our blog: https://sys4.de/en/blog/dmarc-in-de-202503/
Judge for yourself…
The State of DMARC in .DE in March 2025 | sys4 Enterprise Experts
It’s been more than a year Yahoo and Google have begun to require senders to fulfill requirements for email authentication - namely SPF, DKIM and DMARC - if they want these mailbox providers to accept and deliver messages and place them into the INBOX. Anyone else, not following the email authentication standards, risks to have their messages delivered to the SPAM-folder or having them outright rejected during an delivery attempt. This did not come unexpected.
Chrome now supports potential-permissions-policy-violation Reports – And so does URIports!
With the latest 134 update, Chrome can now generate potential-permissions-policy-violation reports, helping developers catch Permissions Policy conflicts before they happen. At URIports, we’re excited to announce that we fully support these new reports, giving you deeper visibility into how embedded content interacts with your site’s security policies.
Learn more about these reports and how they help secure your web applications in our latest blog: https://www.uriports.com/blog/potential-permissions-policy-violation-reports/
Potential Permissions Policy violation Reports
URIports now supports potential-permissions-policy-violation reports, helping detect iframe permission conflicts before features are used. This improves security monitoring, prevents misconfigurations, and strengthens policy enforcement. Stay ahead of potential risks with better visibility.
Out of the top million domains, 303 have implemented a Web Key Directory (WKD) for publishing OpenPGP keys. Among them, 140 use the advanced method, 185 use the direct method, and 22 have configured both. Notably, 13 domains have inadvertently allowed their key folder to be indexed, exposing all public keys and associated email addresses. I will reach out to the administrators of these domains in the coming days.
If you publish PGP keys via WKD and want to verify your setup, or want to start using WKD, you can use our new, free service at https://WebKeyDirectory.com. We’ve also included examples of common misconfigurations for reference.