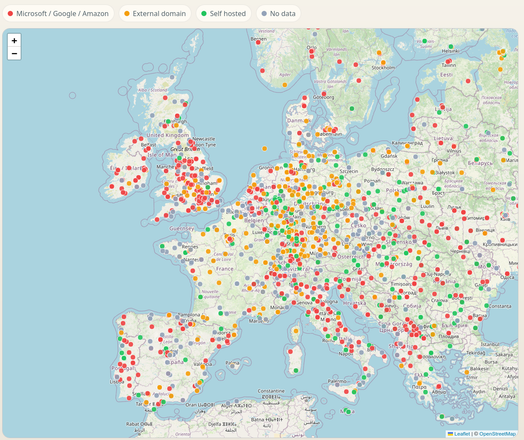
What's the state of digital sovereignty for our academic landscape?
Inspired by a similar post looking at digital sovereignty of municipalities, I explored what messaging infrastructure universities rely on. Sadly, many have switched to hyper scalars but few large universities keep running their own email infrastructure. Germany, Austria, France does not look too bad and lead by example.
[Note that the assessment is based on a simple MX records comparison against a list of known scalars, I don't yet check SPF records or guesstimate the SMTP software/version, this may be done in a future version.]
Check out the interactive map: https://nebelwelt.net/gannimo/unimx/