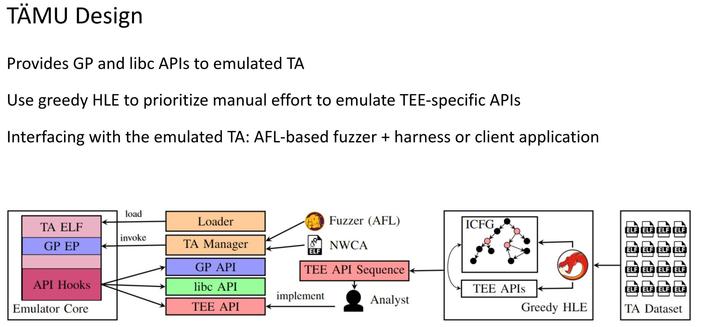
Have you ever wondered what is running on your Android phone? As it turns out, it's not just the apps that you install but there are also so called "trusted applications" that handle your sensitive data like passwords, fingerprints, or keys.
We have developed a high-level rehosting approach that enables security researchers to thoroughly test these applications and found 17 0-days that were responsibly disclosed and are now fixed. This work was presented at this week's IEEE Symposium on Security and Privacy, one of the top-4 security conferences.
https://nebelwelt.net/blog/2026/0521-taemu.html