| Blog | https://edermi.github.io |
| Github | https://github.com/edermi |
| Twitter (inactive) | https://twitter.com/michael_eder_ |
| City | Munich 🥨 |
edermi
- 383 Followers
- 215 Following
- 411 Posts
I just PAID again for #PIDToolbox Pro. And it is such a shit software. I mean what it does is genius, but the user interface and every interaction with it is terrible. You have to install Java and the Matlab Runtime (>2.5GB!). It does not integrate well into the Mac ecosystem at all, and I guess Windows is a similar experience...
I'd actually PAY a monthly fee for a nice #PID #tuning web service. #FPV
This is super nice if you fly #FPV with different video systems and need to align on channels
Internet Protocol Version 8 (IPv8)
Internet Protocol Version 8 (IPv8) is a managed network protocol suite that transforms how networks of every scale -- from home networks to the global internet -- are operated, secured, and monitored. Every manageable element in an IPv8 network is authorised via OAuth2 JWT tokens served from a local cache. Every service a device requires is delivered in a single DHCP8 lease response. Every packet transiting to the internet is validated at egress against a DNS8 lookup and a WHOIS8 registered active route. Network telemetry, authentication, name resolution, time synchronisation, access control, and translation are unified into a single coherent Zone Server platform. IPv4 is a proper subset of IPv8. An IPv8 address with the routing prefix field set to zero is an IPv4 address. No existing device, application, or network requires modification. The suite is 100% backward compatible. There is no flag day and no forced migration at any layer. IPv8 also resolves IPv4 address exhaustion. Each Autonomous System Number (ASN) holder receives 4,294,967,296 host addresses. The global routing table is structurally bounded at one entry per ASN. This document is one of the companion specifications: draft-thain-ipv8-00 Core protocol (this document) draft-thain-routing-protocols-00 BGP8, IBGP8, OSPF8, IS-IS8, CF draft-thain-rine-00 Regional Inter-Network Exchange draft-thain-zoneserver-00 Zone Server Architecture draft-thain-whois8-00 WHOIS8 Protocol draft-thain-netlog8-00 NetLog8 Protocol draft-thain-support8-00 ARP8, ICMPv8, Route8 draft-thain-ipv8-mib-00 IPv8 MIB and SNMPv8 draft-thain-wifi8-00 WiFi8 Protocol draft-thain-update8-00 Update8 and NIC Certification
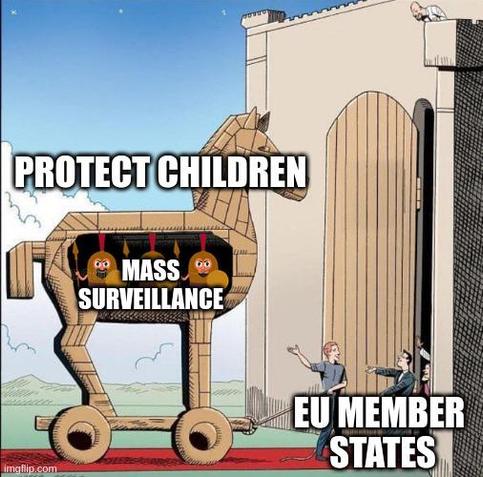
Last month, the EU Council wanted to push through voluntary scanning. But they failed! 🎉
However, the trilogue discussions on Chat Control 2.0 start this Thursday. But #ChatControl is a Trojan Horse for citizens and businesses in Europe. Interestingly, not everyone should be monitored:
❌ Government
❌ Military
✅ YOU
Make sure your country opposes Chat Control! Learn why: 👉 https://tuta.com/blog/chat-control-criticism
https://www.cyclingweekly.com/news/his-dynamic-riding-meant-that-he-was-among-the-leaders-and-within-podium-reach-man-on-stolen-bike-being-pursued-by-police-almost-wins-race
After more than a year in the making it is finally out and available here: https://xintra.org/courses/11-windows-kernel-offensive-defensive-reverse-engineering :)
I will always do open source and publish papers but I've been working for a long time to create a course for people that want structured and in-depth content
I wanted to create this course to give a guided deep dive to the three main pillars anyone that practice security: reverse, offense and defense. This is why, this course putting emphasis not only on the "what" but also the "why" and "how" with everything backed by explanations and snippets from the kernel itself.
Another thing that was important to me is that on top of theoretical and practical knowledge you will receive practical tools that you can use for your research or daily work - which is why by the end of the course you will have your very own EPP (prevention & EDR) and rootkit with a bunch of cool features ready to use.
I'd like to also thank for Xintra and specifically Lina and Ty for everything and to the many people that heard my ideas along the way. My DMs are open for any question :)