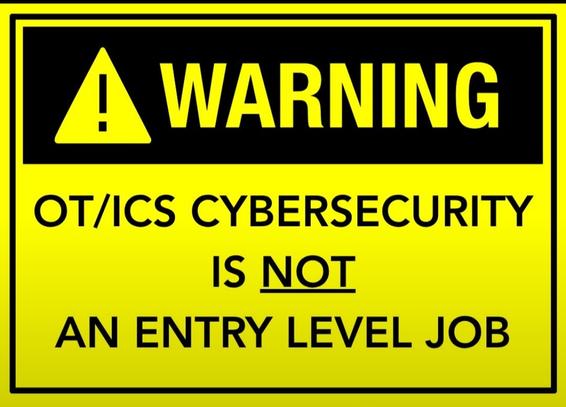
I just realized that so many people in the company simply don’t understand, or don’t want to understand, the Purdue Model!
The Purdue Model is a functional model. Its origins have nothing to do with cybersecurity. It was adopted for cybersecurity, but not as a “zone” model. Its purpose is to define the functional layers at which different methods and tools are used. You don’t simply use typical IT tools at the lower levels!
The DMZ was added much later, as the model evolved into a cybersecurity model. “Additional segmentation can be performed using the concept of zones and conduits described in ISA 62443.” The layers are not intended to define a zone per se. Anyone who does not divide the layers into discrete security zones based on an analysis should not even attempt to work in this (OT) area!
Furthermore, individuals have the flexibility to design their own separation, segmentation, and zone configuration within each architecture, taking into account specific functional and application-related requirements. This approach enables the creation of a robust defense in depth, with the Purdue model serving as a guide while allowing for customization as needed, without rigid requirements.
I will not show these guys how the ISA62443 and the Purde model match. Because I expect that experts can do it and those who can't do it have to learn.
#OTSecurity #Cybersecurity #ICS #Purdue