🚨NEW RESEARCH🚨
Attackers don’t always need zero-days. Sometimes, all it takes is a single character.
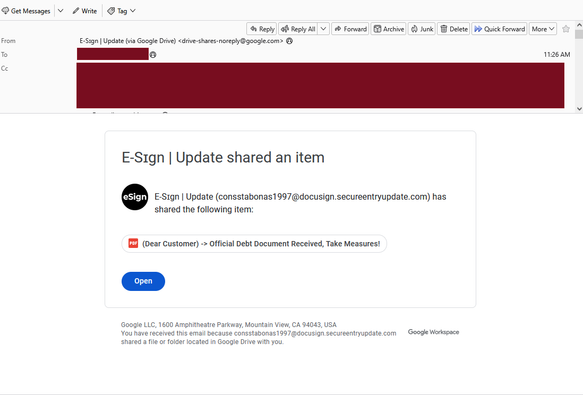
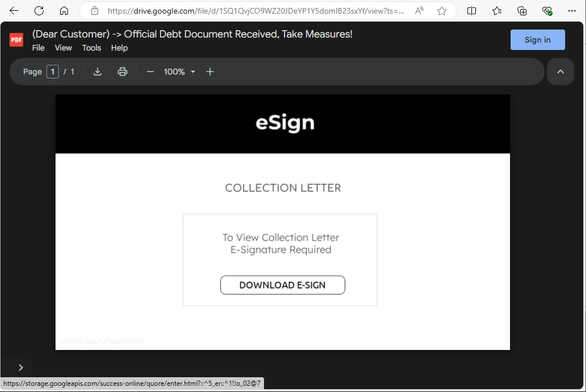
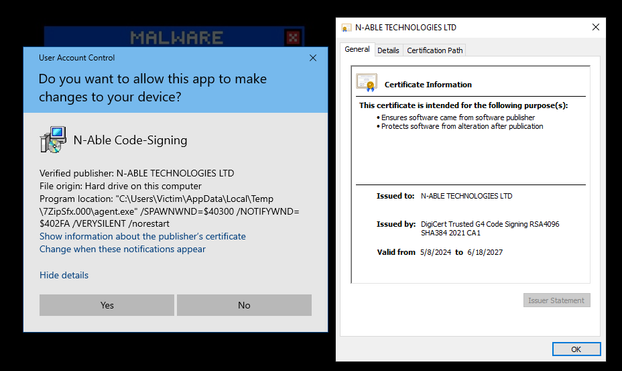
Our researchers recently uncovered a phishing wave abusing the Japanese Hiragana character “ん” – a lookalike that resembles a forward slash or Latin “n.” By inserting it into domain names, attackers are creating URLs that appear legitimate at a glance but redirect victims to credential harvesters, fake crypto wallets, and malware downloads.
Our investigation traced more than 600 malicious domains leveraging this technique.
Why it matters:
Unicode confusion lets these domains slip past regex filters and automated scanners. Punycode encoding makes them DNS-valid and browser-friendly.
The tactic spreads fast, beyond crypto into travel, enterprise, and education. This is a textbook example of attackers weaponizing subtlety.
👉 Read our full analysis here: https://www.netcraft.com/blog/down-the-hiragana-hole-uncovering-a-new-wave-of-lookalike-domains
#BrandProtection #Cybersecurity #ThreatIntelligence