Berlin was faced with a 2nd arson attack on their power grid within a few months, leaving again thousands of households without power, for days. During this incident, several systems were damaged simultaneously deeming any backup systems, ineffective.
An attack like this requires planning, and it starts from reconnaissance.
How did the attackers know to set fire on one specific bridge that contained five high-voltage and ten medium-voltage cables, causing a major power outage in the area?
Can someone find sufficient information on a city's power grid infrastructure available on the internet?
Yes, they can. With more detail than there should be.
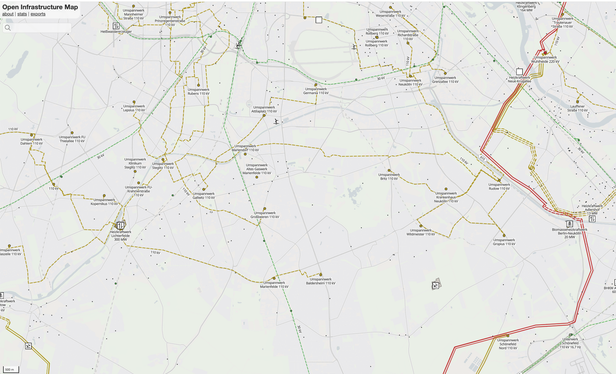
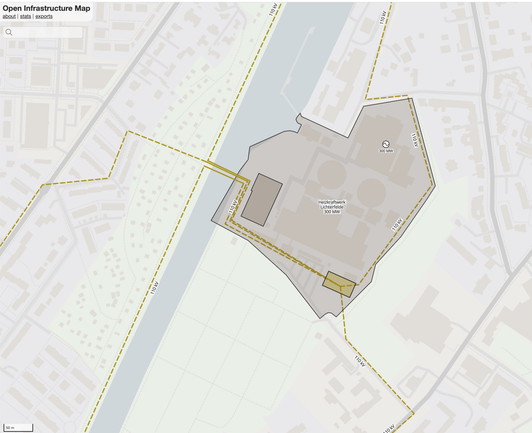
This is where platforms like the Open Infrastructure Map ("OpenInfraMap") enter the game.
𝐎𝐩𝐞𝐧𝐈𝐧𝐟𝐫𝐚𝐌𝐚𝐩 (𝐡𝐭𝐭𝐩𝐬://𝐨𝐩𝐞𝐧𝐢𝐧𝐟𝐫𝐚𝐦𝐚𝐩.𝐨𝐫𝐠/) is an open-source web platform that provides a layered, detailed visualization on global infrastructure data like 𝘱𝘰𝘸𝘦𝘳, 𝘵𝘦𝘭𝘦𝘤𝘰𝘮, 𝘰𝘪𝘭 𝘢𝘯𝘥 𝘨𝘢𝘴 𝘯𝘦𝘵𝘸𝘰𝘳𝘬𝘴, 𝘸𝘢𝘵𝘦𝘳 𝘪𝘯𝘧𝘳𝘢𝘴𝘵𝘳𝘶𝘤𝘵𝘶𝘳𝘦 𝘢𝘯𝘥 𝘮𝘢𝘫𝘰𝘳 𝘳𝘢𝘪𝘭 𝘱𝘰𝘸𝘦𝘳 𝘴𝘺𝘴𝘵𝘦𝘮𝘴 𝘪𝘯𝘧𝘳𝘢𝘴𝘵𝘳𝘶𝘤𝘵𝘶𝘳𝘦 (the data is crowdsourced from OpenStreetMap).
Don't think that searching this map needs to take time, by using Overpass Turbo (also with the help of with any LLM that it is compatible with) one can significantly trim the search time and concentrate their research through queries.
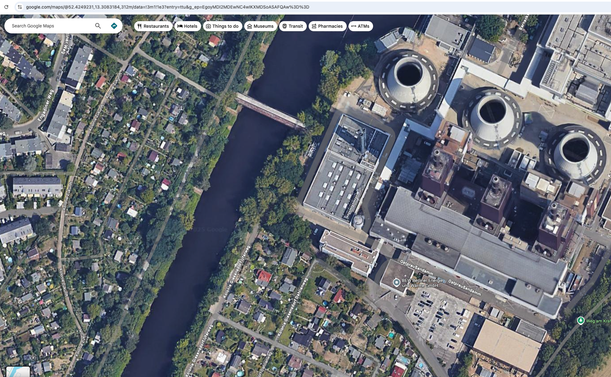
Looking at the OpenInfraMap data in combination with satellite imagery, it is easy to see why this point of attack was chosen: all the 110 Κilovolt high-voltage lines that supply southwest Berlin converge into a single cable bridge that is overground, accessible, near a sparsely populated area, with plenty of hiding spaces (trees, etc).
The Google street view imagery provides some extra help in reviewing some of the physical security and the surrounding area in preparation of a better plan.
The OpenInfraMap in combination with Google maps is just one simple example of potential adversarial OSINT. There is more publicly available information and databases that can be researched, found, and used in similar acts of sabotage (or worse, given the geopolitical state we are currently in).
It is scary easy for saboteurs or other attackers to find vulnerabilities on critical infrastructure free & available online, and to focus on the locations/points where an attack could have the maximum impact.
This incident has not been an isolated event.
What can be done? If you work on securing a critical infrastructure entity:
🔹 Run your own OSINT analysis to identify vulnerabilities in advance. Know your level of exposure.
Control what you can:
🔹 Where possible, ask platforms to add blur or remove certain imagery. Aim for less detail in what can be visible, even through crowdsourced images.
🔹 Prioritize based on risk and take practical steps to implement better security measures on those vulnerable, identified spots before an adversary exploits them.
#OSINT #BerlinBlackout