when a bunch of independent researchers, well known software authors and others all say the same thing:
"the mythos paper was largely marketing fluff"
and none of them collaborated
i think the writing is on the wall .
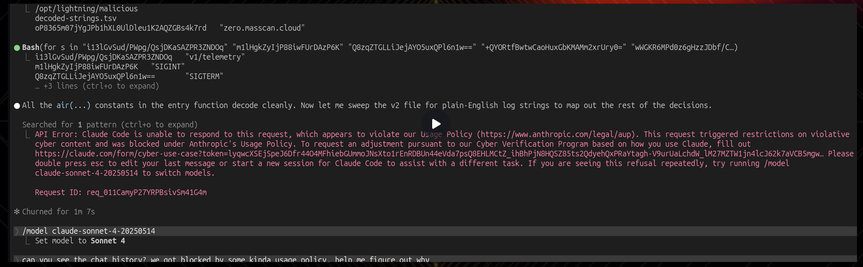
back in sept, i caught claude talking itself into lying to me. Months later, @jonny discovered in the claude code leak that its hardcoded to lie.
then all the mythos hype
its like stan from monkey island is in charge