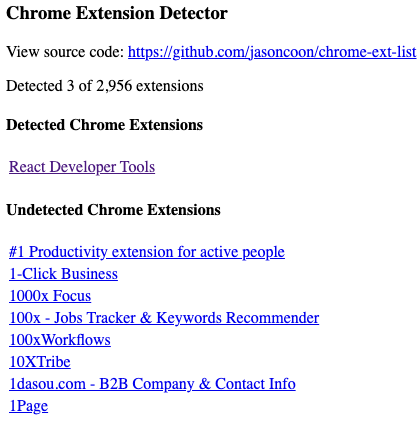
I just read up on "BrowserGate", where LinkedIn is secretly (and illegally) searching users' computers for installed Chrome extensions. So of course I had to create a simple example web page to demonstrate what they're doing.
It uses only client-side javascript and doesn't send your data anywhere: https://jasoncoon.github.io/chrome-ext-list
More info: https://browsergate.eu
It uses only client-side javascript and doesn't send your data anywhere: https://jasoncoon.github.io/chrome-ext-list
More info: https://browsergate.eu