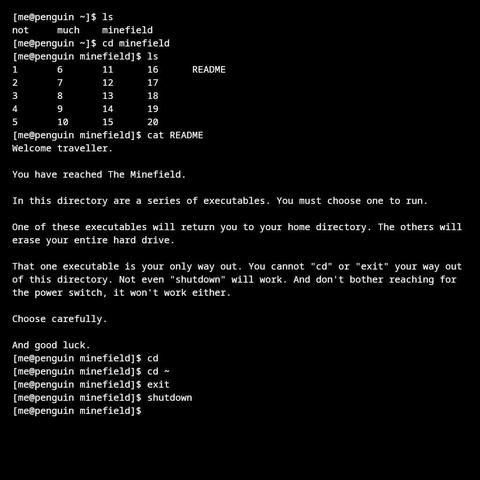
The Minefield
There’s an Emacs command to do that
C-x M-c M-minefield
Encrypt hard drive and keep the key in RAM. Could be recovered with a cold boot attack but that’s very advanced. The DOS virus ONEHALF would run as a daemon encrypring a block on the drive on each boot and intercept reads/writes to the encrypted part as if nothing ever happened. Only after encrypting ½ of the disk, it would reveal itself with an ominous
Dis is one half. Press any key to continue...The decryption was eventually cracked by ESET and they developed a tool to recover the drive.
If you are using KDE
cat with a trojan or something.
I can think of a way out:
Just throw the whole PC away. It’s someone else’s problem now!
There was an old virus that would copy your FAT table to ram, erase it from disk, and preset you with a slot machine UI where you would gamble to get the FAT back, if you won, great, the virus would write the FAT back to the drive, if not, you lost everything.
Rebooting without playing meant loosing everything.
FAT Table
Can I just pay? I can go to the ATM Machine and enter my PIN Number
find ./ -type f | xargs md5sum, then avoid the one directory where the executable has a different checksum. Heck, even find | ls might suffice.
ls -al and compare the sizes.
I wonder if we could bash -n -v the source code? 🤔 Since -n should error check without execution.
Edit: maybe that only works on scripts?
cat 1
cd to locations. At one point you search the “garden”, which is an unmanageable tangle of directories, with find.
Reminder that binaries cannot change a shell’s working directory, so the non-mines will do nothing.
(cd is a shell builtin)
$SHELL in the parent dir
strings 1
while this is not real, something similar in principal very much was! (but not too widespread)
see here or look up “casino dos malware”
uh in short it erases “the disk’s” (unsure which) file allocation table (pretty much the dos/windows version of a superblock). apparently some versions did copy it to memory and give the user a chance though!
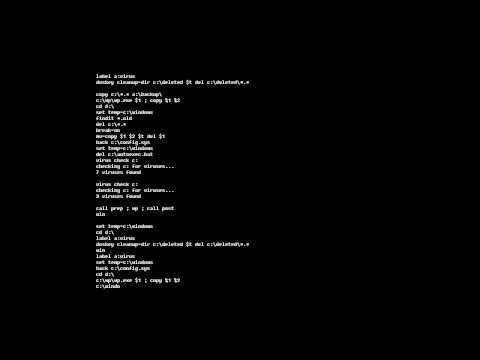
Old Software Review: Fake DOS Screen Saver 1.0
We have squid games at home.
Squid games at home: