Speaking of SecureDrop, next up is 'SecureDrop Next Generation: Lessons from a Decade of Deployment', presented by Rowen Shane, Shannon Veitch
#realworldcrypto
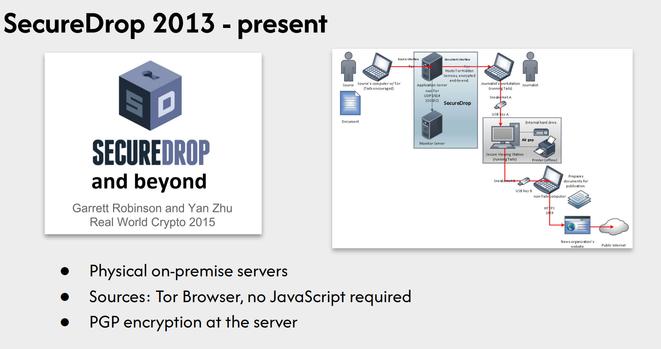
Uses Tor, PGP encryption,
#realworldcrypt
Deployment/maintenance burden, physical security requirement, better encryption is available
#realworldcrypto
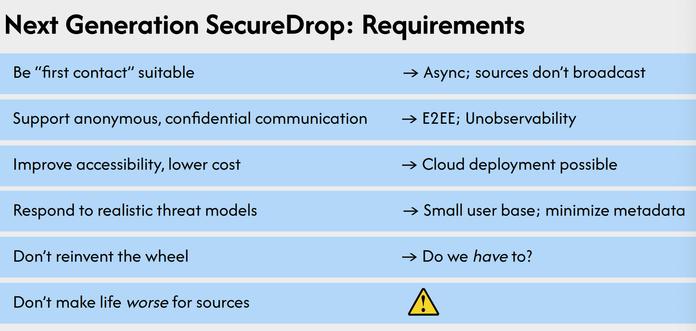
What do we want from a next-gen SecureDrop?
#realworldcrypto
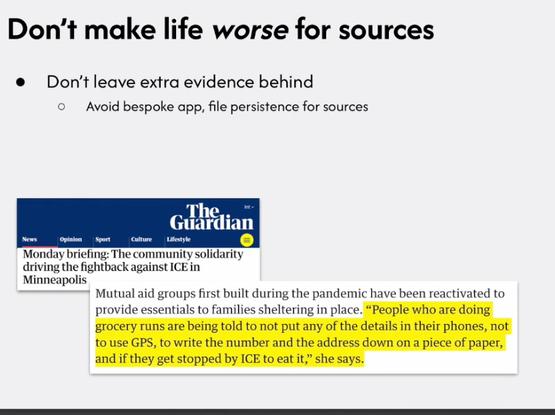
Don't want to leave extra evidence behind
#realworldcrypto
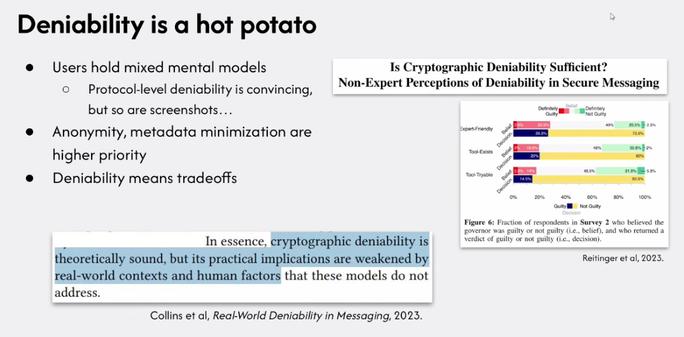
'The real way to use deniability is in combination with other security properties of the system; there are tradeoffs against authentication'
#realworldcrypto
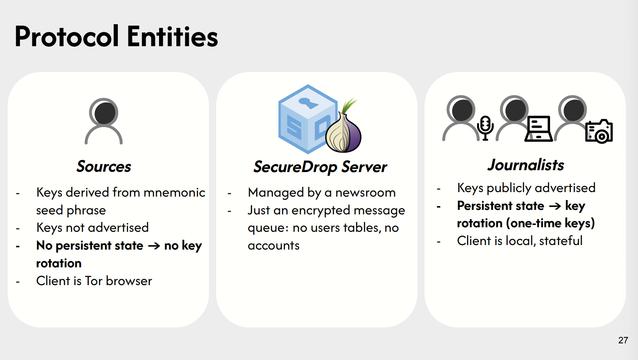
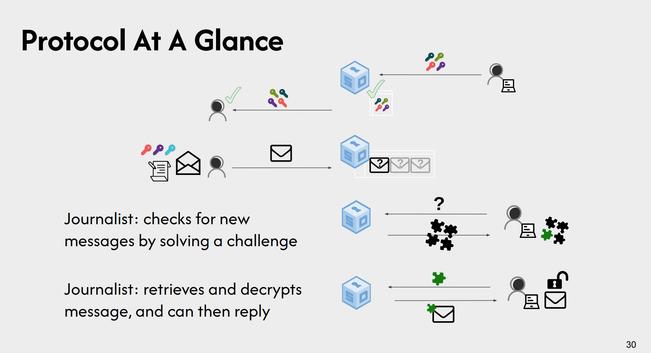
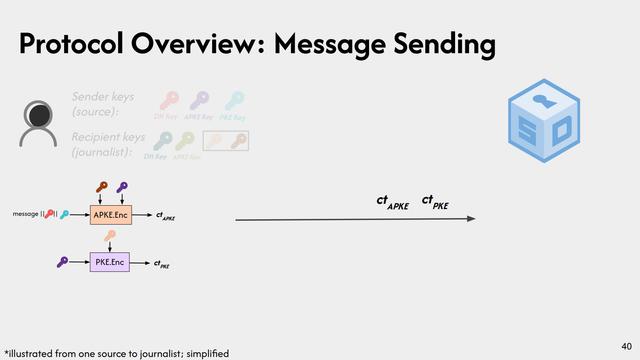
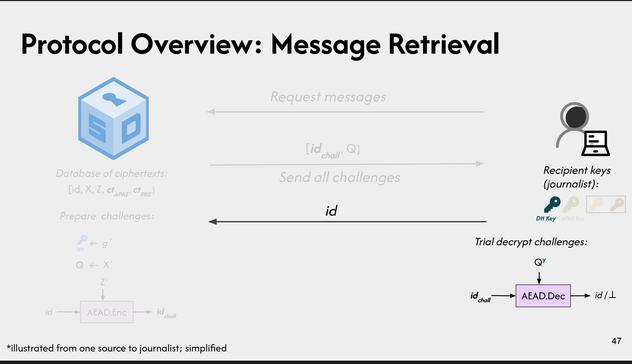
Client is the Tor browser; no persistent state; server is 'just' an encrypted message queue; one time keys
#realworldcrypto
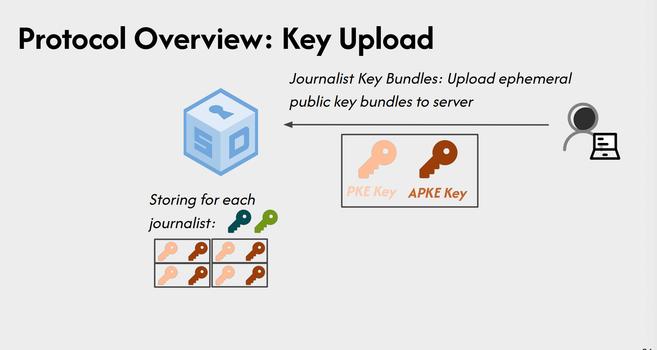
Key bundles per-journalist
#realworldcrypto
Hints
#realworldcrypto
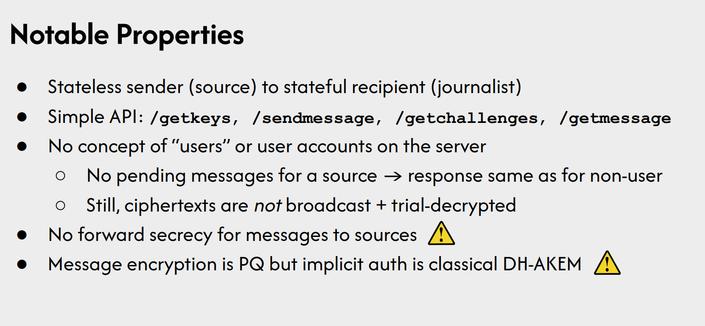
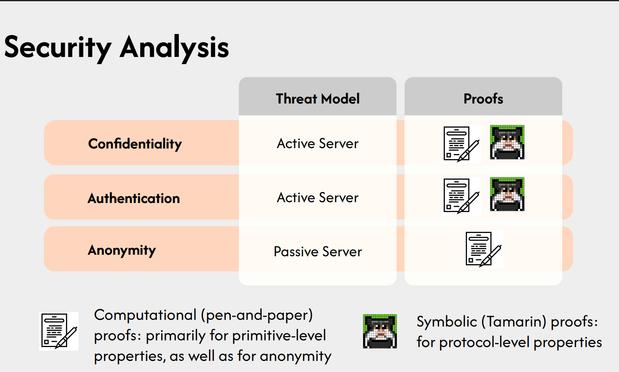
Specifics about the new SecureDrop protocol
github.com/freedomofpre...
#realworldcrypto
github.com/freedomofpress...
github.com/freedomofpress...
Pros, and cons
#realworldcrypto
Different organizational profiles motivate different deployment types
#realworldcrypto
Next steps, attachments, formal verification!
github.com/freedomofpre...
github.com/freedomofpre...
#realworldcrypto
GitHub - freedomofpress/secure...
GitHub - freedomofpress/secure...
Q: Target a particular journalist, key exhaustion?
A: Known, not seen in existing SecureDrop instances, so deferring doing anything for now, but there are approaches
#realworldcrypto
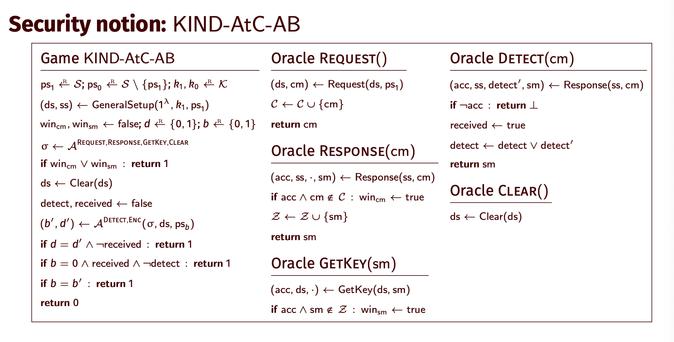
Next up, 'At-Compromise Security: The Case for Alert Blindness', presented by Simone Colombo
#realworldcrypto
How much are our assumptions and models actually based on the real world?
#realworldcrypto
"Cryptography is also a social science unaware of itself."
#realworldcrypto
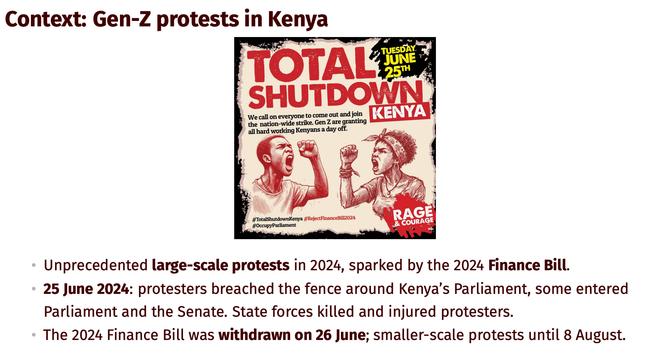
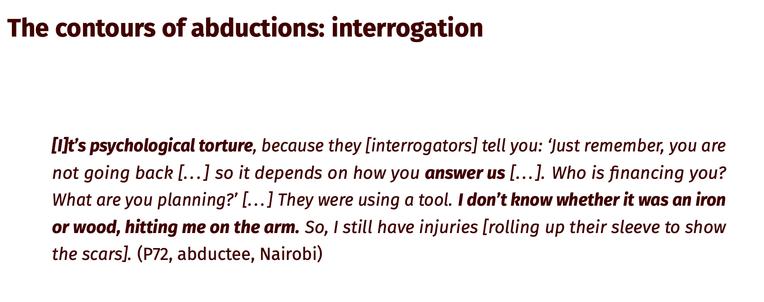
82 abductions related to these protests
#realworldcrypto
Vigorous application of ethnography to cryptography
#realworldcrypto
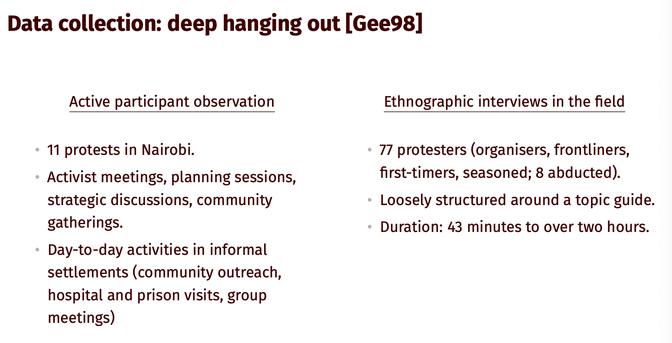
'deep hanging out' (technical term)
#realworldccrypto
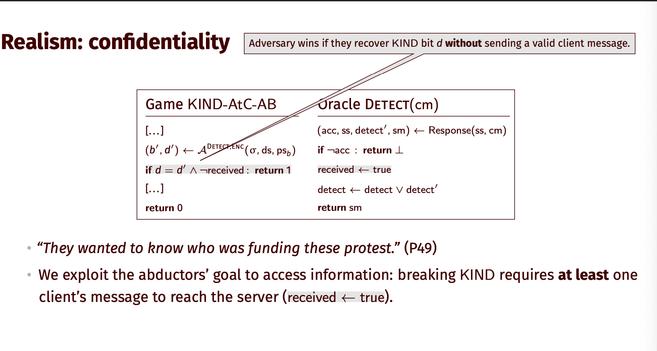
Adverary goal: intelligence, via torture
#realworldcrypto
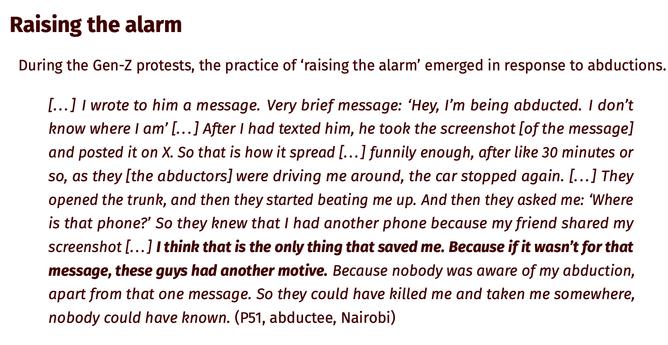
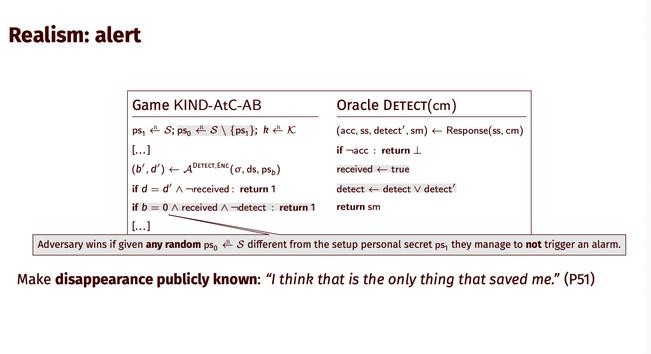
'raising the alarm' saved victims
#realworldcrypto
"The abductors eventually heard the message, which put pressure on them to release the abducted person."
#realworldcrypto
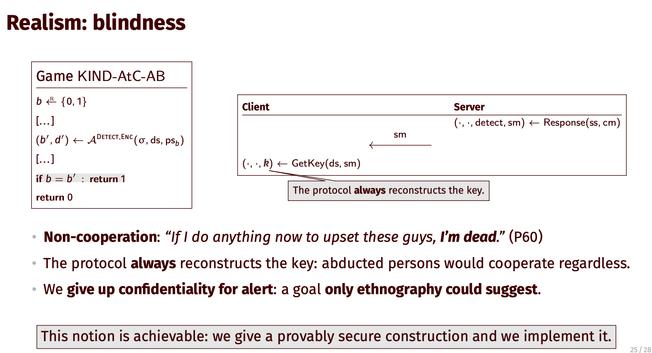
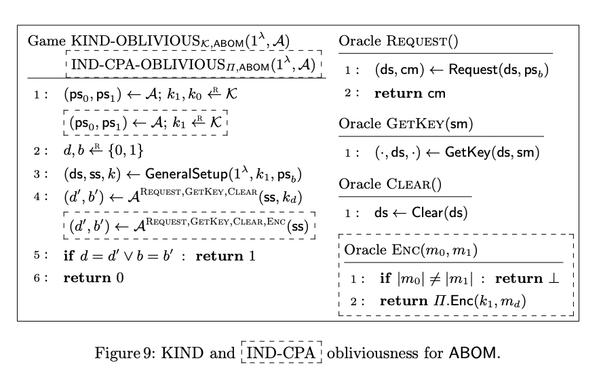
At-compromise alert blindness: when they are taken, abducted people can alert their network without the adversary noticing
#realworldcrypto
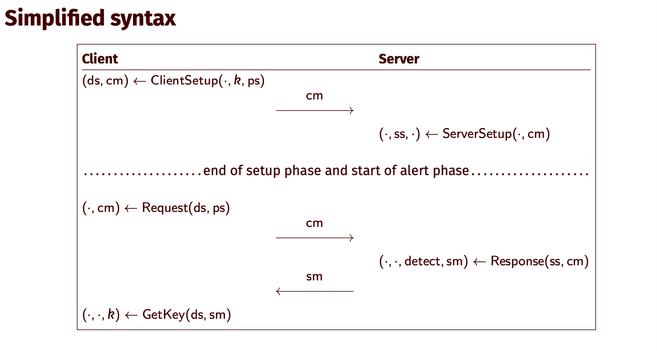
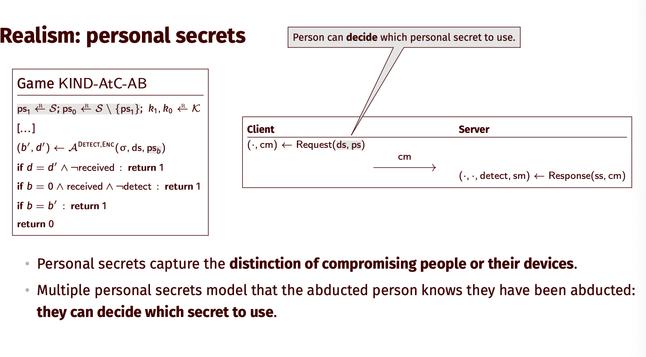
Personal secrets capture the distinction of compromising people or their devices. Multiple personal secrets model that the abducted person knows they have been abducted:
they can decide which secret to use.
#realworldcrypto
Alert
#realworldcrypto
Blindness: 'If I do anything now to upset these guys, I’m dead.'
#realworldcrypto
We give up confidentiality for alert: a goal only ethnography could suggest. We give a provably secure construction and we implement it.
#realworldcrypto
Ethnography proposes 'exists' statements, not 'for all' statements
#realworldcrypto
Coffee time
#realworldcrypto
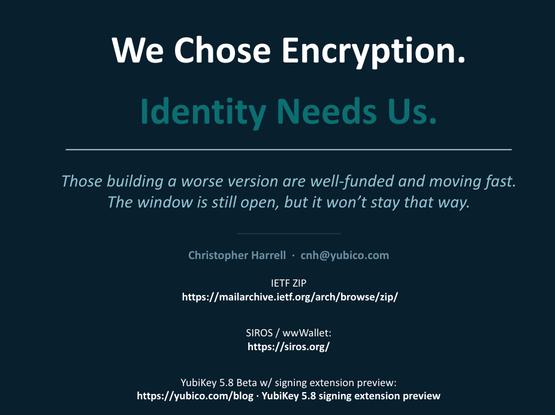
'Defending the Open Internet: TLS, Passkeys, and the Privacy Stakes of Digital Identity', by Christopher Harrell
#realworldcrypto
Q: How do I resolve the dilemma that if i work on this, governments will use it to discriminate [against children, women, etc]
A: Build primitives that work with trust lists, group of issuers we trust [um we trusted the US until we didn't, oops]
#realworldcrypto
Q: Device-bound means i lose my creds
A: Cloud-based HSM [narrator: 🙄]
#realworldcrypto
Not all have PQ privacy
#realworldcrypto
Q: The nice ZKs going to PQ change the computational/privacy properties
A: Depending on the construction (BLS vs ML-DSA, relying on the symmetric guts of certain constructions)
#realworldcrypto
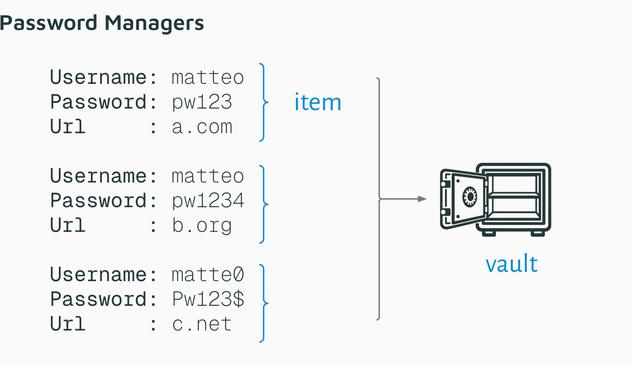
Next up, 'Zero Knowledge (About) Encryption: On the Security of Cloud-based Password Managers', presented by Matteo Scarlata and Giovanni Torrisi
#realworldcrypto
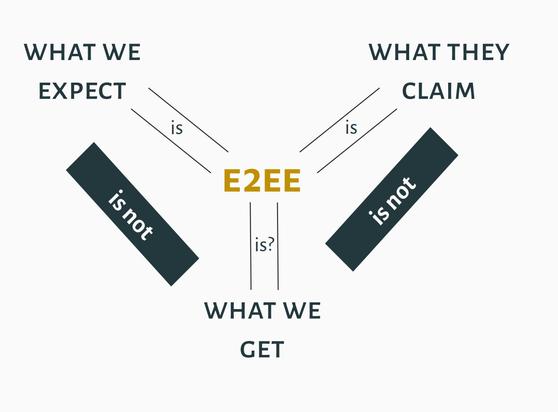
'E2EE' password managers
#realworldcrypto
We don't trust the server, should only have access to the vault plaintext if you have access to the master password
#realworldcrypto
uh oh
#realworldcrypto
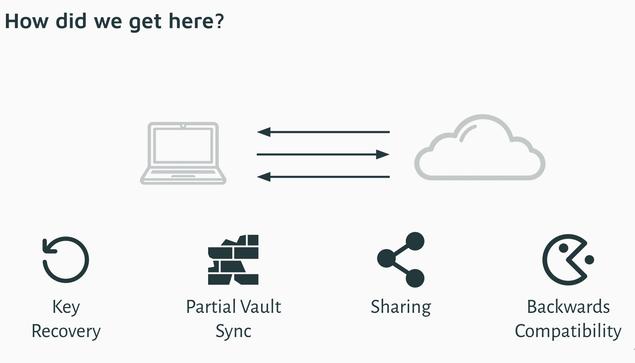
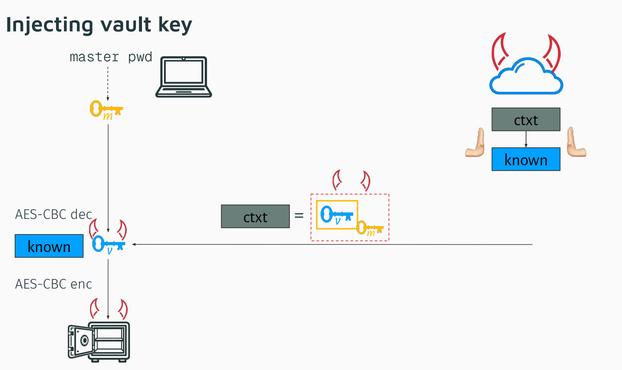
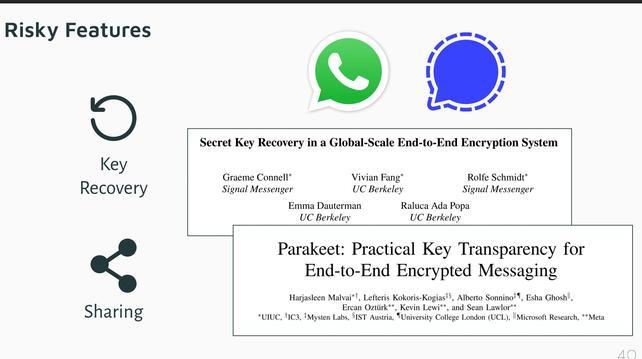
features ('features') that lead to this breakdown:
#realworldcrypto
oh recovery flows
#realworldcrypto
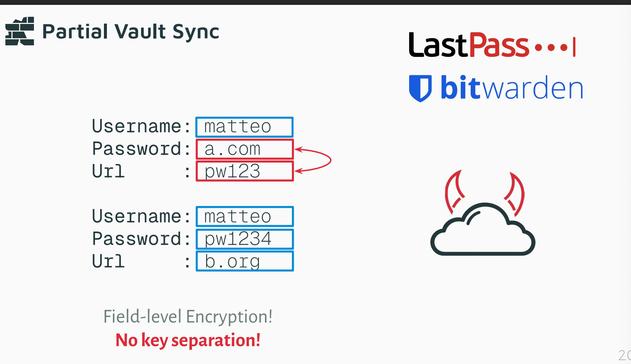
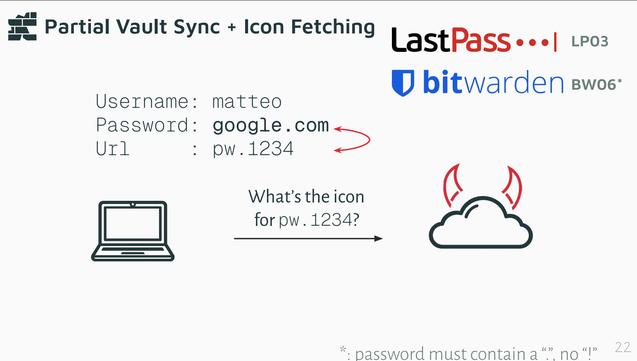
Partial vault sync (😭)
#realworldcrypto
Relatedly, icon fetching ('metadata')
#realworldcrypto
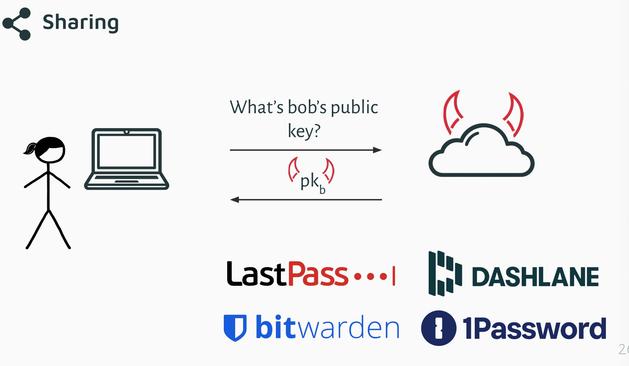
Sharing items
#realworldcrypto
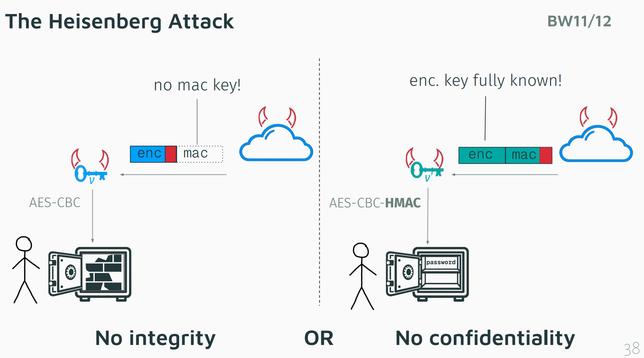
backwards compatibility leads to attacks 😭
#realworldcrypto
Heisenberg Attack: 'nothing to do with Breaking Bad, although we're gonna break it pretty badly 😈'
#realworldcrypto
Ways to mitigate security issues in these risky features: key transparency, better designs for key recovery
#realworldcrypto
SAY IT AGAIN
#realworldcrypto
Better protections against downgrade attacks
#realworldcrypto