Next up, 'Encryption in the microarchitectural world', presented by Ping-Lun Wang
#realworldcrypto
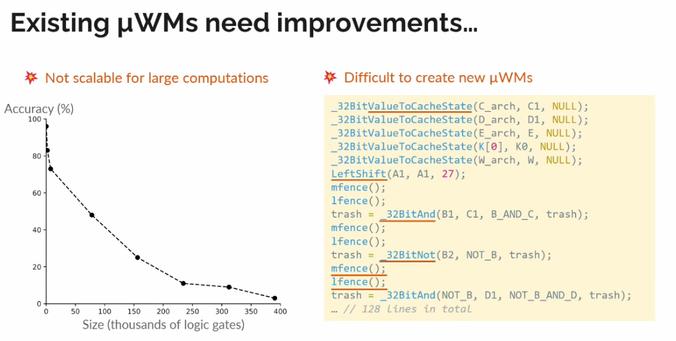
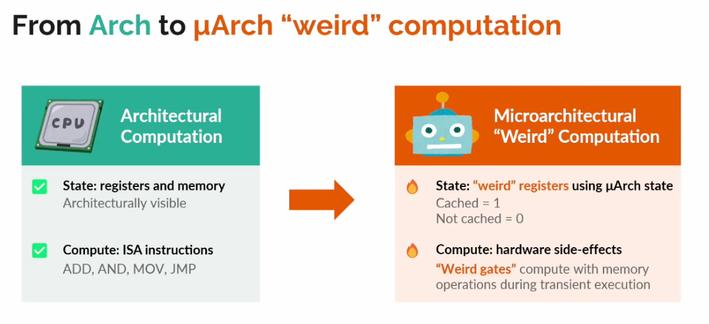
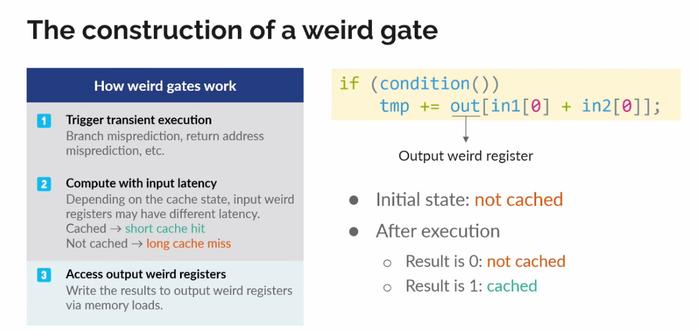
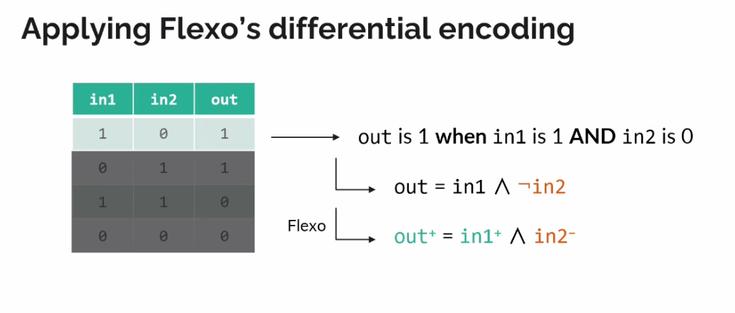
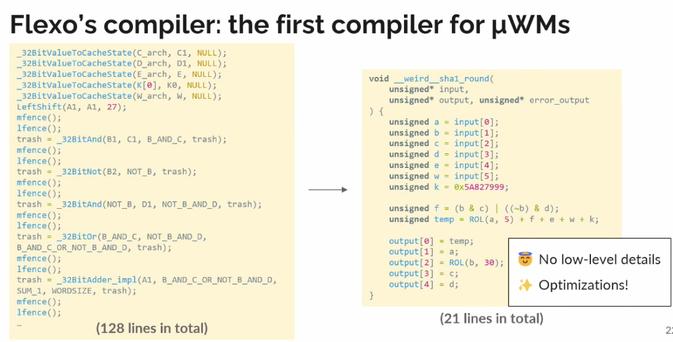
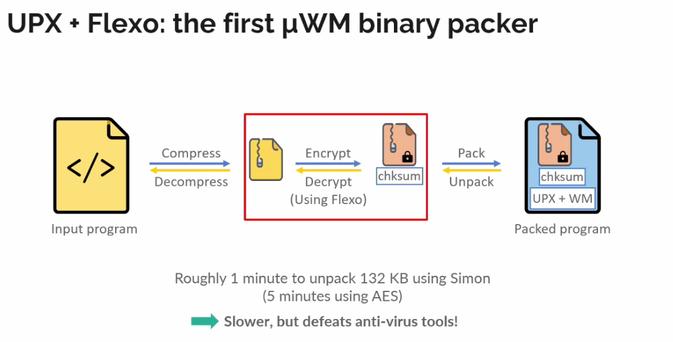
microarchitectural 'weird machines'
#realworldcrypto
We can construct weird machines that work across processor classes, despite small changes in microarchitectures
#realworldcrypto
END OF DAY 1
#realworldcrypto
DAY 2
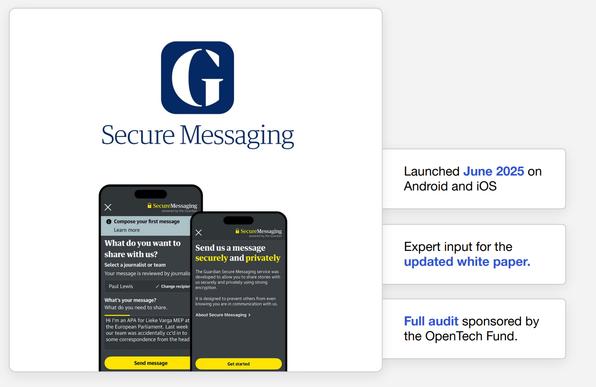
Next up is 'Deploying Research:
On Building and Shipping an
Anonymous Whistleblowing System', presented by Daniel
Hugenroth
#realworldcrypto
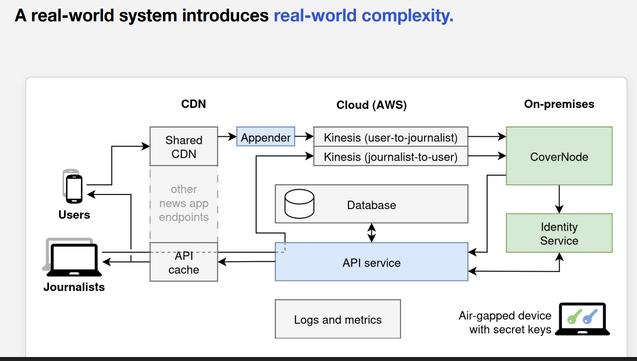
Implemented and deployed in the Guardian app on iOS and Android
#realworldcrypto
Really want boring simple cryptography with few assumptions; used Rust bc strong typing enabled misuse-resistant API design, and performance came for free
#realworldcrypto
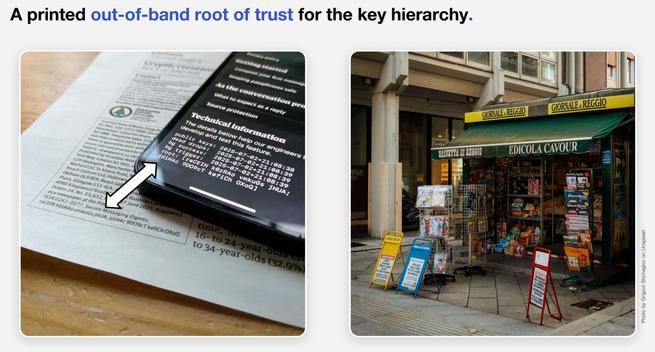
How do we bootstrap trust in the org key? It helps to be part of a long-trusted publication
#realworldcrypto
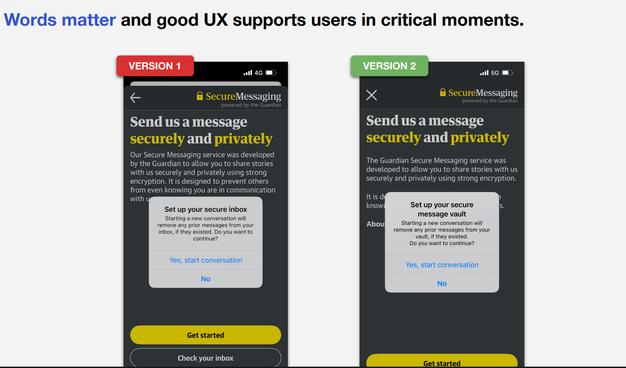
'Words matter'
#realworldcrypto
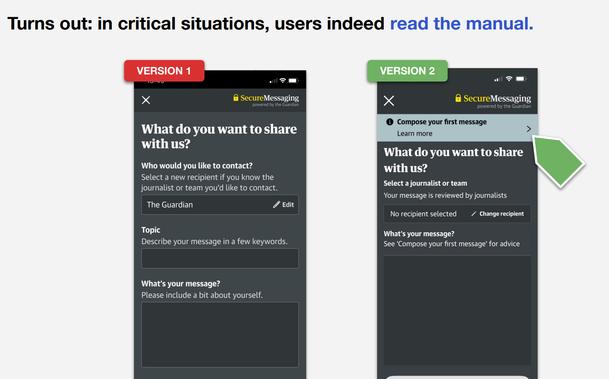
When sufficiently motivated, users do read the manual
#realworldcrypto
Awesome
#realworldcrypto
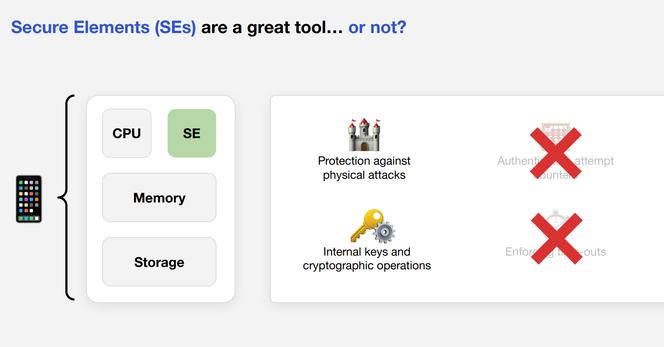
Secure elements are great tools...except they don't expose auth attempt counters, nor enforce timeouts (they are reserved for the operating system)
#realworldcrypto
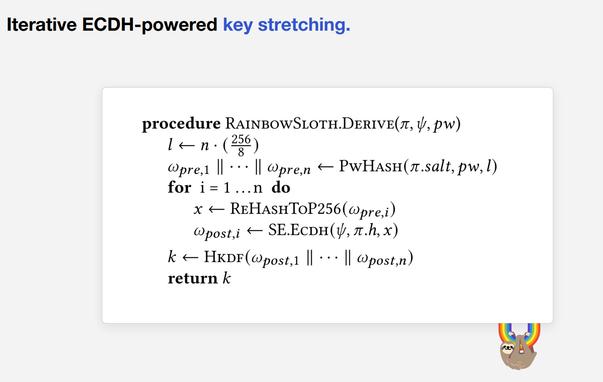
RainbowSloth key stretching scheme
#realworldcrypto
Q: Diff from SecureDrop?
A: Focused on the first contact experience; using Tor is a red flag/signal; we don't support sending files, pivot elsewhere for that
#realworldcrypto
Work with actual UX researchers; in-person user testing;
#realworldcrypto
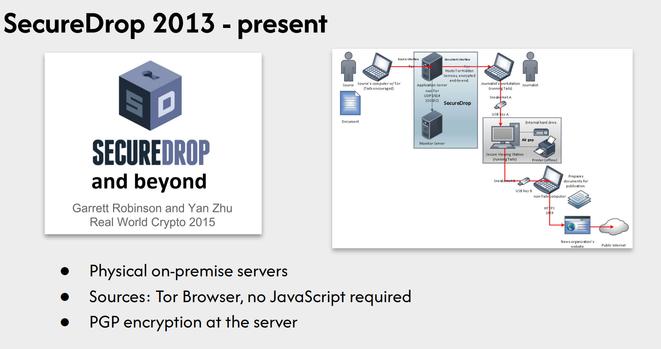
Speaking of SecureDrop, next up is 'SecureDrop Next Generation: Lessons from a Decade of Deployment', presented by Rowen Shane, Shannon Veitch
#realworldcrypto
Uses Tor, PGP encryption,
#realworldcrypt
Deployment/maintenance burden, physical security requirement, better encryption is available
#realworldcrypto
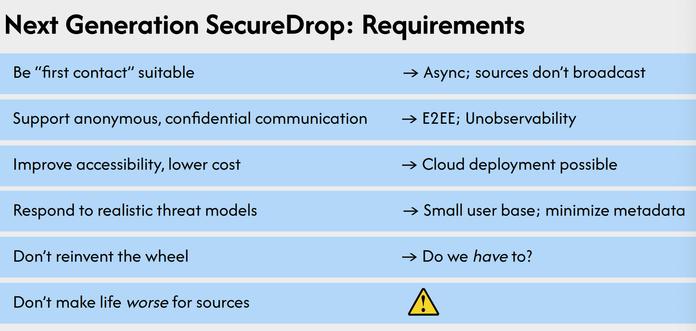
What do we want from a next-gen SecureDrop?
#realworldcrypto
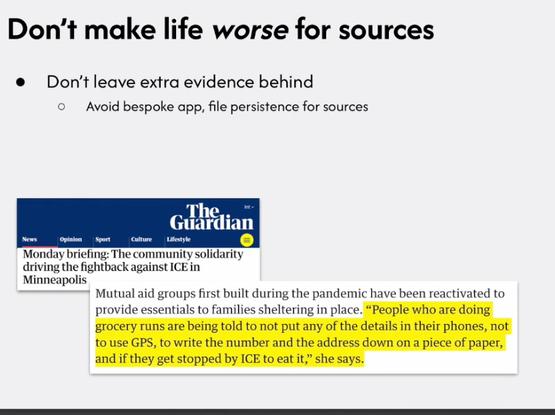
Don't want to leave extra evidence behind
#realworldcrypto
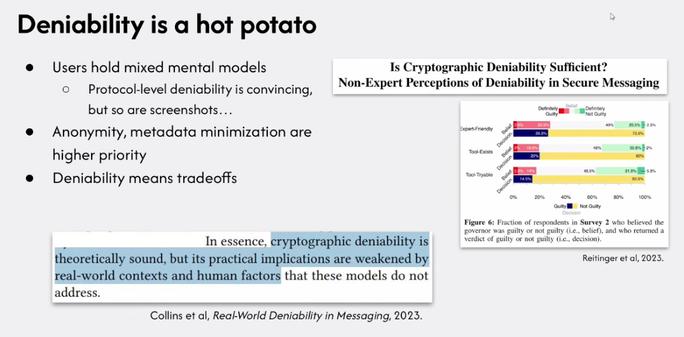
'The real way to use deniability is in combination with other security properties of the system; there are tradeoffs against authentication'
#realworldcrypto
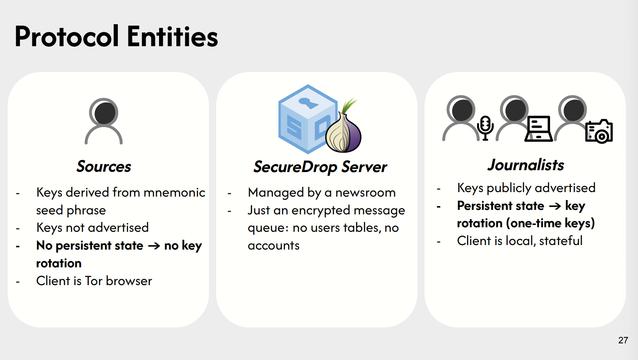
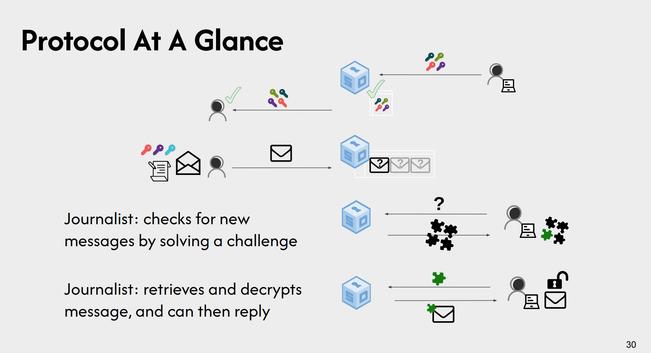
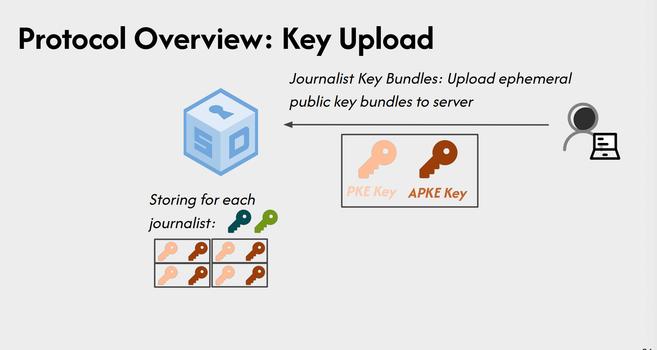
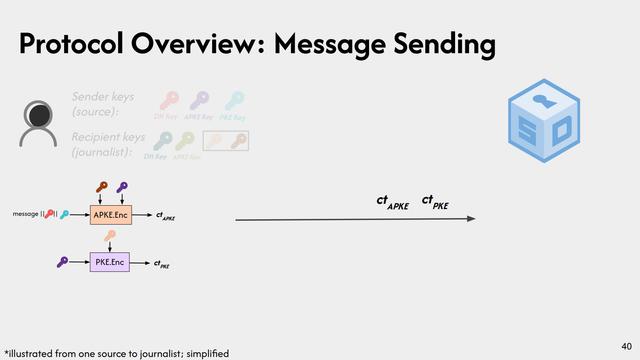
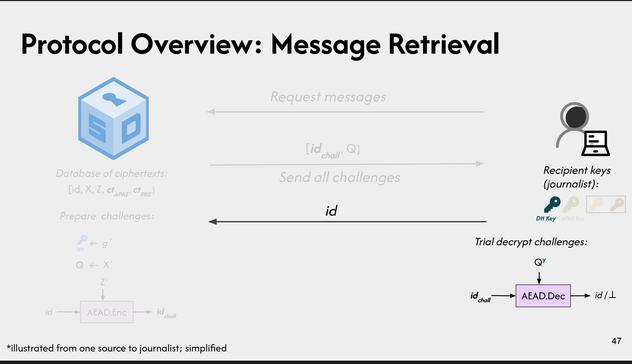
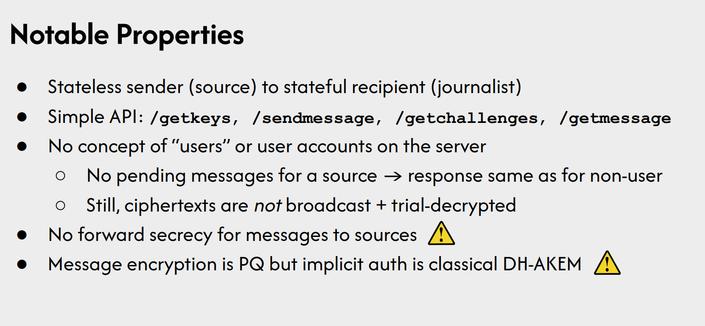
Client is the Tor browser; no persistent state; server is 'just' an encrypted message queue; one time keys
#realworldcrypto
Key bundles per-journalist
#realworldcrypto
Hints
#realworldcrypto
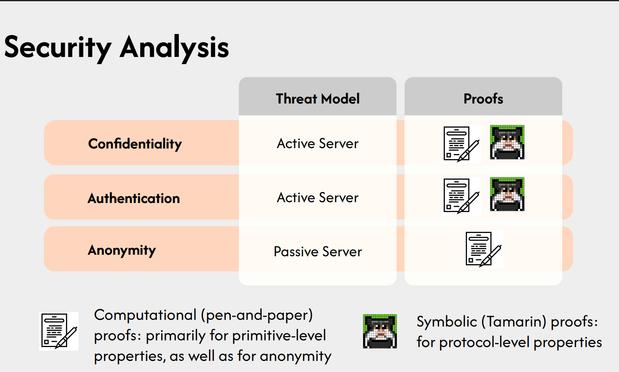
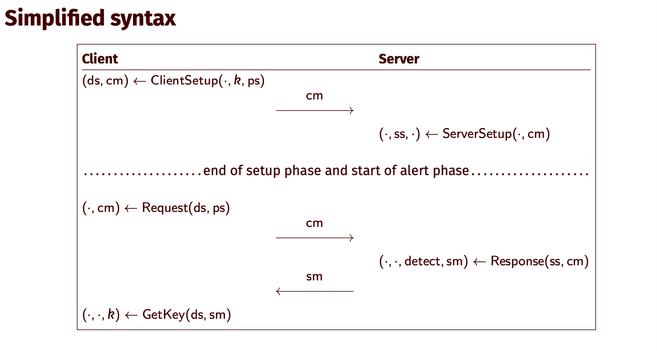
Specifics about the new SecureDrop protocol
github.com/freedomofpre...
#realworldcrypto
github.com/freedomofpress...
github.com/freedomofpress...
Pros, and cons
#realworldcrypto
Different organizational profiles motivate different deployment types
#realworldcrypto
Next steps, attachments, formal verification!
github.com/freedomofpre...
github.com/freedomofpre...
#realworldcrypto
GitHub - freedomofpress/secure...
GitHub - freedomofpress/secure...
Q: Target a particular journalist, key exhaustion?
A: Known, not seen in existing SecureDrop instances, so deferring doing anything for now, but there are approaches
#realworldcrypto
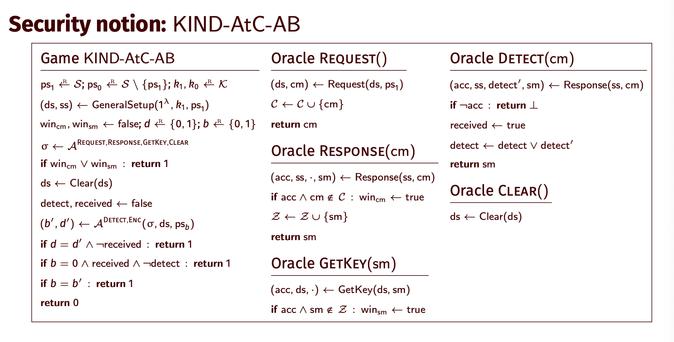
Next up, 'At-Compromise Security: The Case for Alert Blindness', presented by Simone Colombo
#realworldcrypto
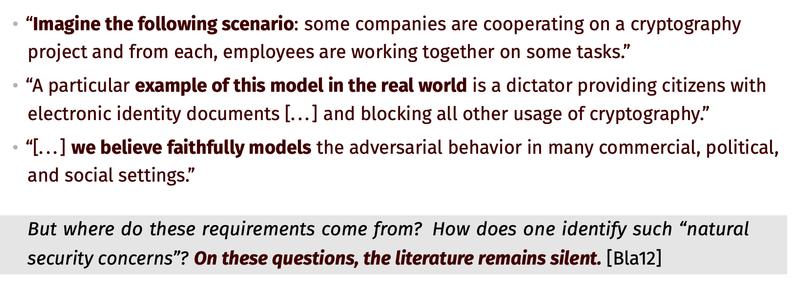
How much are our assumptions and models actually based on the real world?
#realworldcrypto
"Cryptography is also a social science unaware of itself."
#realworldcrypto
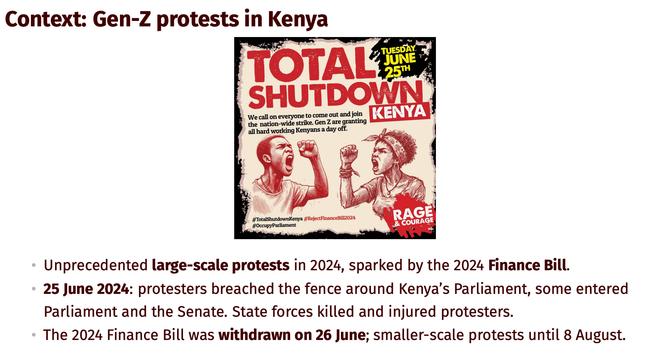
82 abductions related to these protests
#realworldcrypto
Vigorous application of ethnography to cryptography
#realworldcrypto
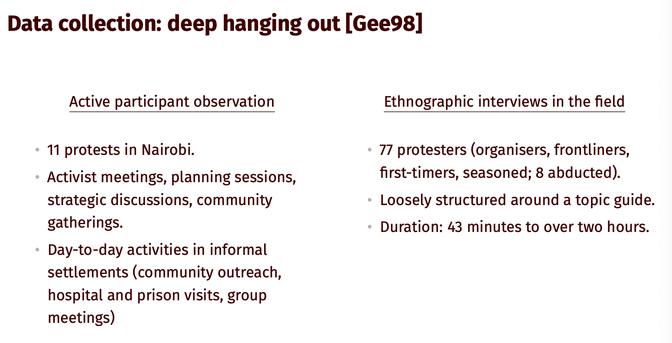
'deep hanging out' (technical term)
#realworldccrypto
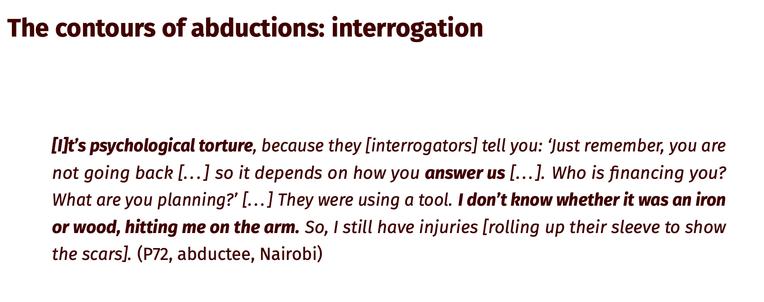
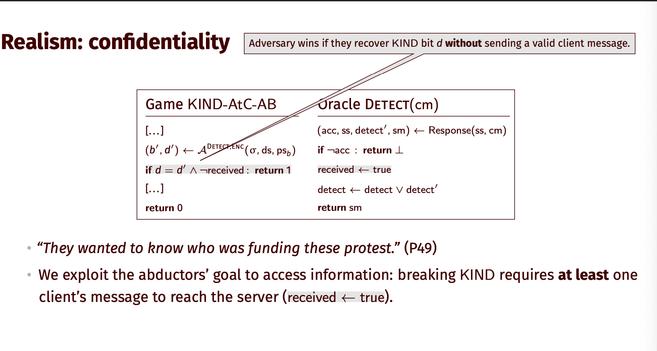
Adverary goal: intelligence, via torture
#realworldcrypto
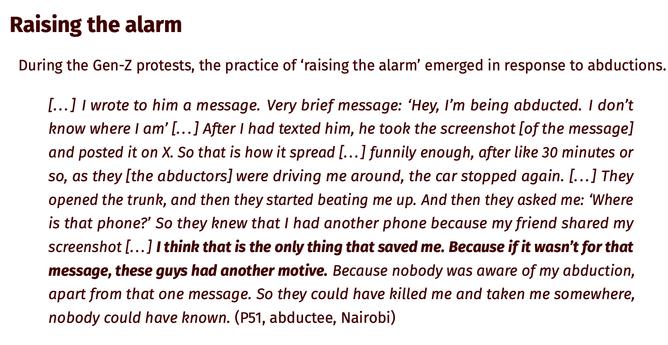
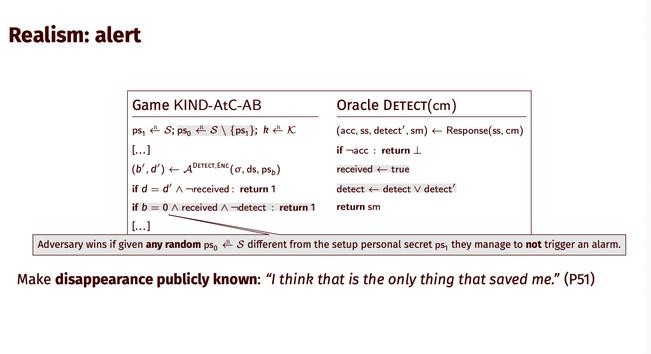
'raising the alarm' saved victims
#realworldcrypto
"The abductors eventually heard the message, which put pressure on them to release the abducted person."
#realworldcrypto
At-compromise alert blindness: when they are taken, abducted people can alert their network without the adversary noticing
#realworldcrypto
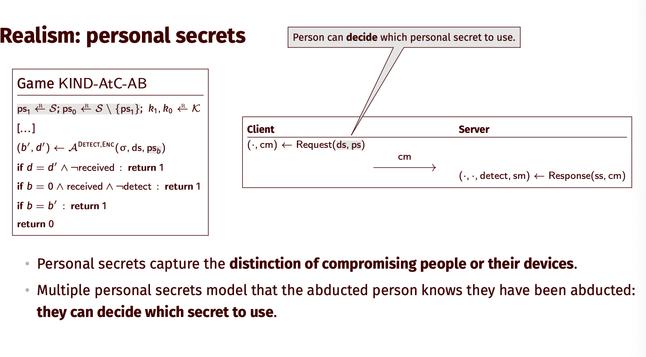
Personal secrets capture the distinction of compromising people or their devices. Multiple personal secrets model that the abducted person knows they have been abducted:
they can decide which secret to use.
#realworldcrypto
Alert
#realworldcrypto
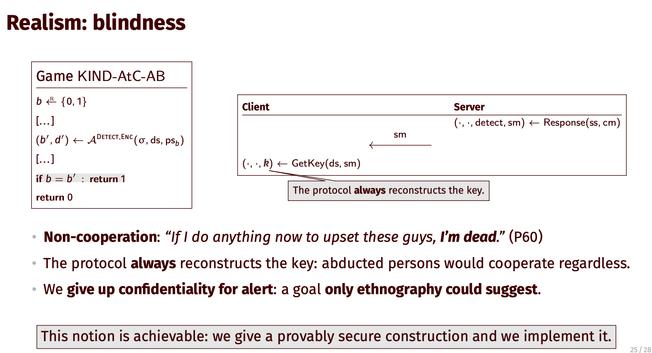
Blindness: 'If I do anything now to upset these guys, I’m dead.'
#realworldcrypto
We give up confidentiality for alert: a goal only ethnography could suggest. We give a provably secure construction and we implement it.
#realworldcrypto
Ethnography proposes 'exists' statements, not 'for all' statements
#realworldcrypto