Did you know theres likely a cryptographic lock on your computer that can prevent you installing whatever OS you choose (likely if it was made in the last 2 decades)
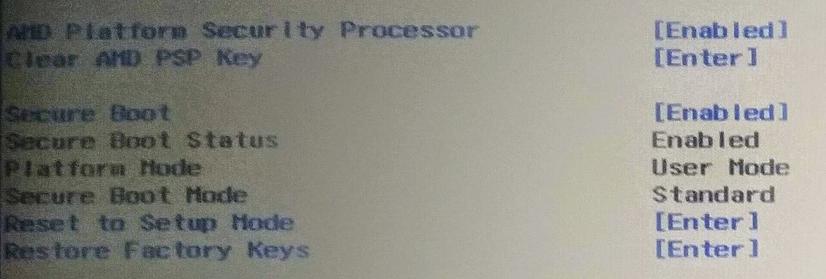
For intel its called Intel Management Engine for AMD its called AMD Platform Security Processor
These are closed environments isolated from the rest of the machine that perform security checks on the OS as it is booting
State and capital know personal computing is a double edged sword and can give proles too much power: so they've been quietly building locks at the core of your computer so you don't understand the freedom that is being taken from you.
When activated it would be trivial to outlaw any OS that isnt government approved like already happens in North Korea.
The only way I can think of to get around this is to support Open Source Hardware projects especially those building open source CPUs and full motherboards there are very few of them but most seem to be building on the RISC-V standard instruction set.
#OpenSourceHardware #RISCV #Anarchism #NorthKorea #Capitalism #IntelMangementEngine #AMDPlatformSecurityProcessor