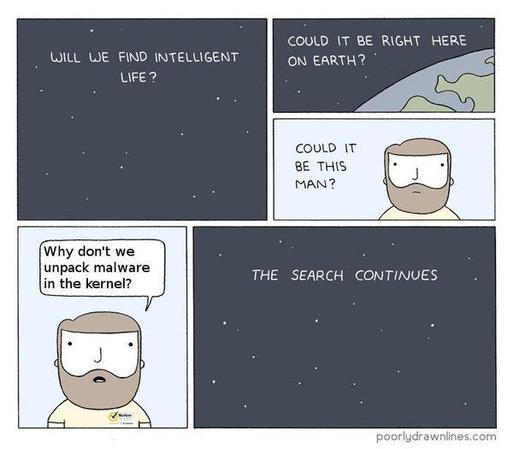
In the ‘90s, I used to run antivirus software on Windows and it found a bunch of things, including one virus that was on a magazine cover disk (ooops!). When I was at Microsoft, for the entire five years, every single thing that Windows Defender flagged was a false positive. Worse, it also turned out that they had the same design flaw everyone mocked Norton for 20 years earlier: they ran parsers, written in CL in the kernel. This let a malicious file get kernel-privilege execution simply by being scanned by Windows Defender, so a drive-by download or an email attachment that you don’t open (but which is written to disk) could trigger a compromise.
25 years ago, there was a tradeoff between an increased attack surface but also real detections but, as far as I could see, modern antivirus has no upsides. My work machine at Microsoft might have been entirely riddled with malware, but if so Defender didn’t find any of it. And may even have been the cause of some of the infection.
Has anyone actually had any kind of attack prevented by one of these things in the last five to ten years?

 ✅🎯🙄
✅🎯🙄