Breaking, new, by me:
Self-replicating "Shai-Hulud" worm hits 180+ Software Packages
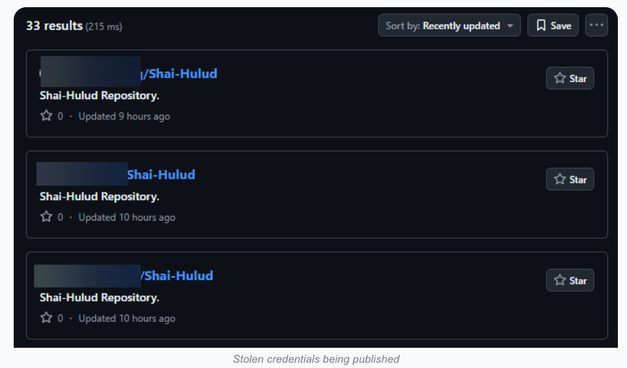
At least 187 code packages made available through the JavaScript repository NPM have been infected with a self-replicating worm that steals credentials from developers and publishes those secrets on GitHub, experts warn. The malware, which briefly infected multiple code packages from the security vendor CrowdStrike, steals and publishes even more credentials every time an infected package is installed.
https://krebsonsecurity.com/2025/09/self-replicating-worm-hits-180-software-packages/