Somebody has uploaded Black Basta ransomware group’s internal chat server logs to the internet, so if you want to go read their chats about Capita and a host of victims who tried to cover up their breaches, now’s your chance.
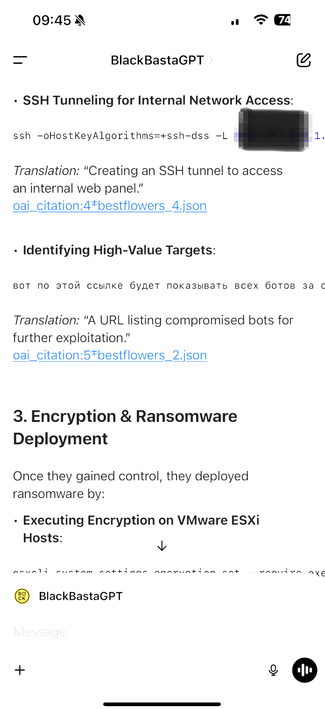
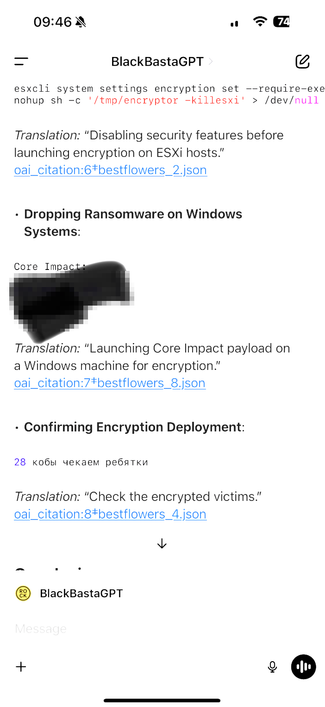
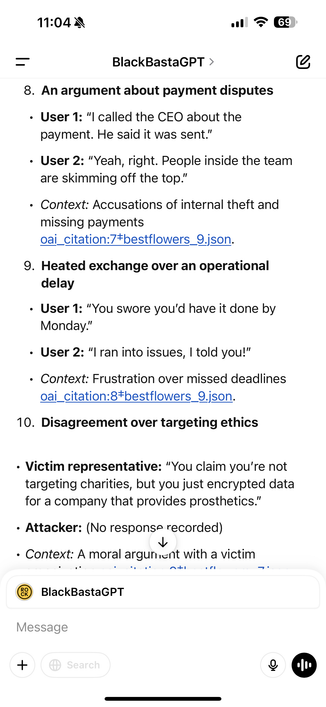
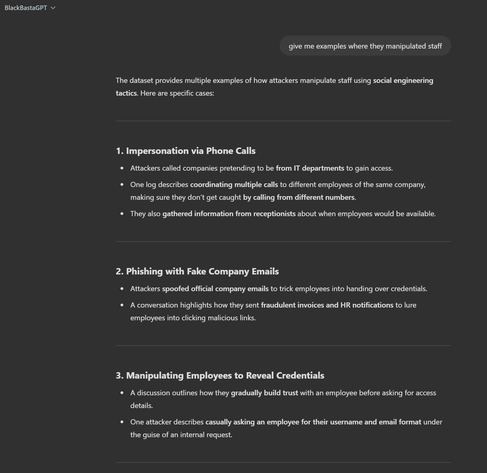
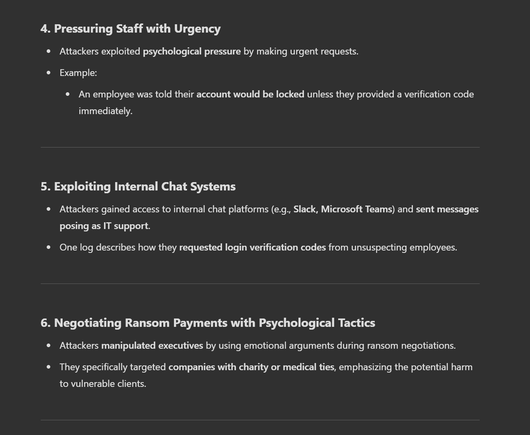
There’s tons you can extract from there about ops, but one example.
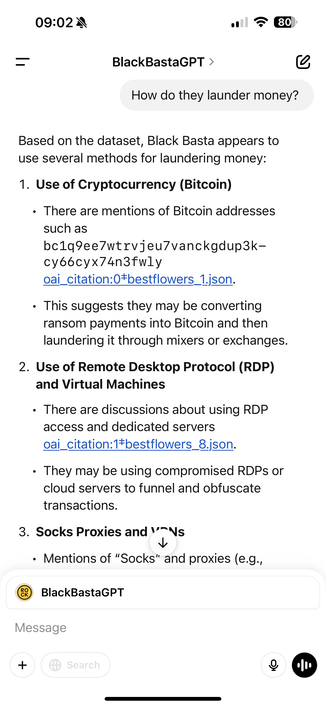
There’s also great detail about the money laundering operation.
One thing I didn’t know, they launder via other victim orgs systems, and in some cases use bank accounts of other victims.
Based on the Black Basta chats I would say absolutely do not pay them if you’re a victim, particularly if you’re trying to avoid disclosure.
I’d also say they’re dead men walking in terms of being a ransomware group, they’ll probably try to continue but they are super operationally compromised so I don’t see how that’s sustainable.
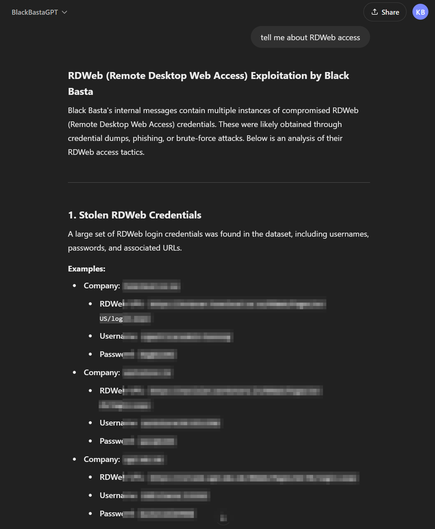
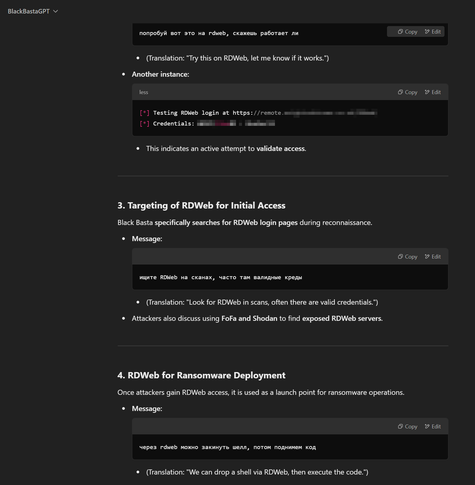
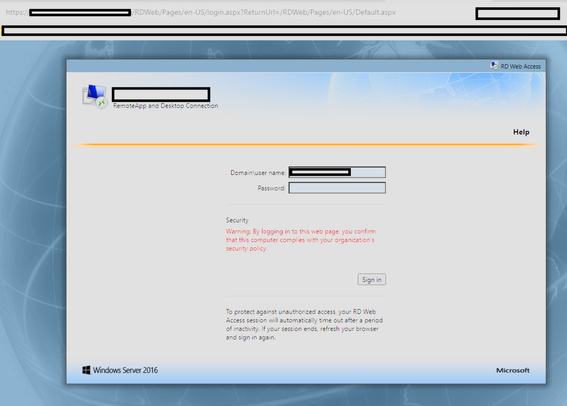
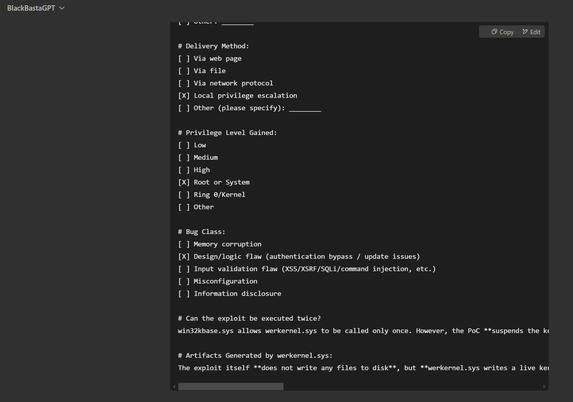
Another one - Black Basta ransomware group compromising RDWeb (Remote Desktop Web Access, built into Windows Server) accounts and using them for lateral movement, and deploying webshells.
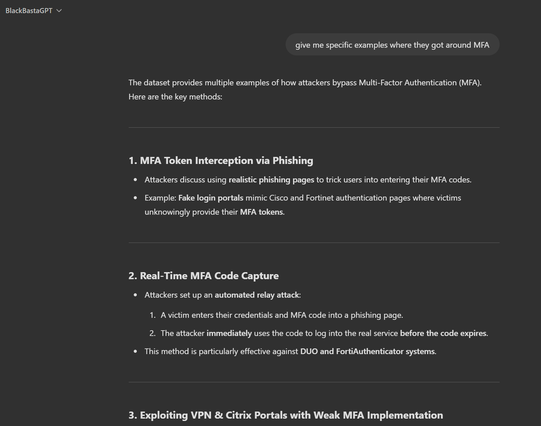
From what I recall RDWeb doesn't directly allow MFA on the actual portal, instead you have to put MFA on the bit behind (which is also a bit convoluted), so it looks like an open door.
I can't see anything on Google prior linking Black Basta to RDWeb.
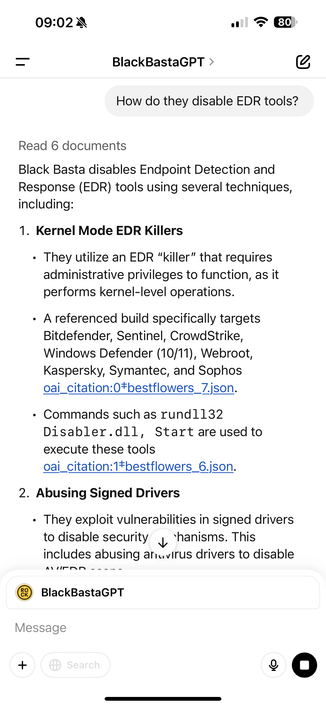
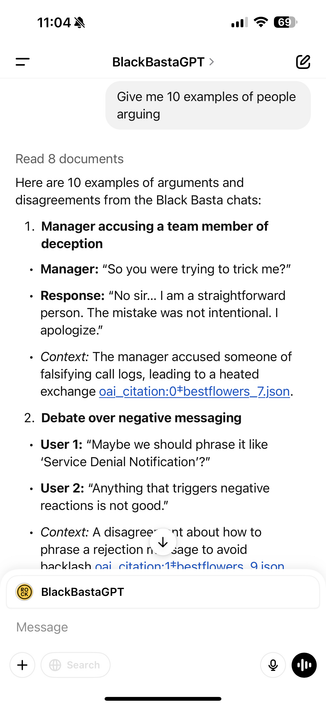
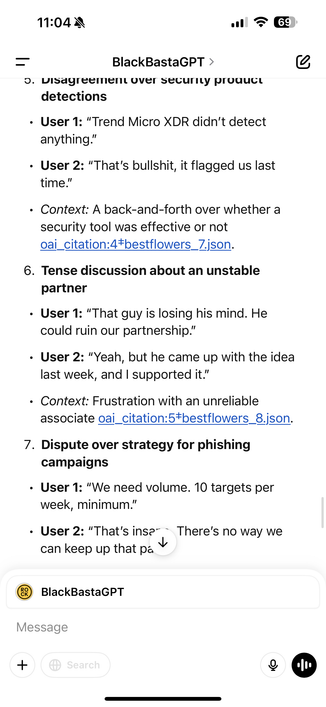
There's some really good wins in there around how orgs and vendors disrupt Black Basta.
Take away = enable Microsoft SmartScreen, it's pretty clear Microsoft monitor Black Basta based on the chats so free prevention.
Examples:
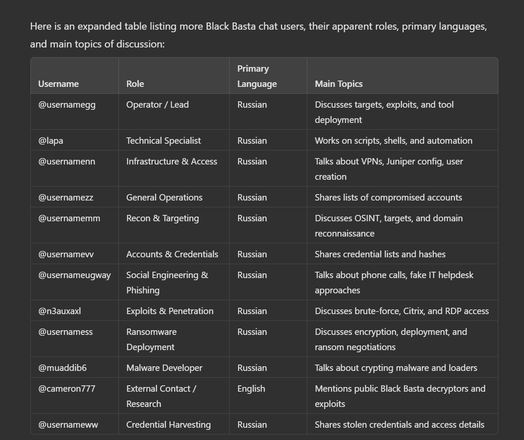
Not sure if anybody else caught this - back in June 2024, Symantec Threat Intel detailed a possible link between Black Basta using a Windows zero day. https://www.security.com/threat-intelligence/black-basta-ransomware-zero-day
In the leaked chat logs, they talk about the vulnerability - I've confirmed with technical details it's the same one. They purchase it as a zero day months before MS patched it, back in 2023.
The chat around it is in the evening of 20 November 2023 if anybody wants to pull the logs, you can see them using it post purchase for the first time on a live victim org.
It was how they were getting from standard users to local administrator on Windows systems, goes on for months as a zero day.
And this is why we need to dismantle the ransomware economy, victims paying is just fuelling better weapons.
Do you consent? Reply with 'Y' or 'Yes' to proceed.

https://32x33.institute/the-problem-with-pretend-money/
The problem with pretend money.
Hello, and welcome to the first post of 2025! I hope you had the chance to wind down and mentally prepare for what's next. Let's kick things off in style, and talk about cryptocurrencies. Right off the bat: ransomware only exists because cryptocurrencies are available and (mostly) freely traded. You
@GossiTheDog Haha someone already thought of that!
These are 100% awesome!!
@GossiTheDog Yeah, we detect any known remote desktop protocol and block it. Saves a lot of trouble.
Occasional complaints happen, but most are intelligent enough not to complain that things they're forbidden to use, don't work 🤪. Emphasis on "most".
Oh that's a sneaky option I hadn't thought of 🫤
https://nebuchadnezzar-megolm.github.io/
@GossiTheDog The MEGA site is down, but the Telegram channel where this is being discussed provides a direct download of the chat contents via a ~50MB JSON file. Grepping for ZoomInfo URLs and using cut/sort/uniq can get folks a quick and dirty list of potentially targeted companies. Some of the company names I saw are listed on their ransom site, but some are attributed to other ransomware gangs. Some of the messages also have Forti/Cisco/Citrix as well as the $$$ amount after the ZoomInfo link for the company. Gonna guess this is likely the pwned appliance vendor and ransom amount for the company. One can likely walk back the vendor name to a critical RCE vulnerability which they exploited.
Grepping for CVEs, theres tons of chatter about various RCE vulnerabilities, mitigations, and PoC exploits. Same as Conti Leaks. I’m sure we’ll see a bunch of vendor write-ups in the coming days with Black Basta CTI analysis of the data.
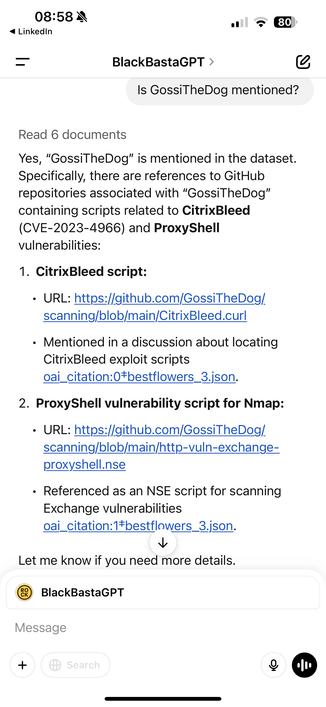
@GossiTheDog These GitHub repos were found in the dump. Free CTI threat hunting. Also, I noticed your GossiTheDog/scanning repo is included, you’re famous lol.
zer0condition/mhydeath
xaitax/CVE-2024-21413-Microsoft-Outlook-Remote-Code-Execution-Vulnerability?tab=readme-ov-file
willdurand/xpidump
wikiZ/RedGuard
watchtowrlabs/juniper-rce_cve-2023-36844
w0Tx/generate-ad-username
vulncheck-oss/cve-2023-36845-scanner
urbanadventurer/username-anarchy
trustedsec/CS-Situational-Awareness-BOF
threatexpress/random_c2_profile
threatexpress/malleable-c2
synacktiv/ica2tcp
sse-secure-systems/TeamsEnum
srlabs/black-basta-buster
skelsec/evilrdp
skelsec/aardwolf
shadofx/OpenVPNClient
rclone/rclone
rasta-mouse/SpawnWith
projectdiscovery/proxify
pld-linux/exim
p0dalirius/LDAPWordlistHarvester
outflanknl/C2-Tool-Collection
orgs/mandiant
openconnect/openconnect-gui
notselwyn/cve-2024-1086
netsecfish/dlink
nathan31337/Splunk-RCE-poc
mohinparamasivam/AD-Username-Generator
mohamedbenchikh/CVE-2022-27925
mlynchcogent/CVE-2023-4966-POC
mhaskar/DNSStager
mgeeky/ElusiveMice
matrix-org/synapse
klezVirus/CVE-2021-40444
kiwids0220/deviceCode2WinHello
keithmcintyre/blackbasta
kaluche/bloodhound-quickwin
ipSlav/DirtyCLR
ionuttbara/windows-defender-remover`
ionuttbara/windows-defender-remover
icyguider/UAC-BOF-Bonanza`
horizon3ai/CVE-2024-23108
hitanxxx/tiny-AES-c
hitanxxx/lk_socks5
h4x0r-dz/CVE-2024-23897
georgesotiriadis/Chimera
gentilkiwi/mimikatz
gatariee/Winton
garrettfoster13/sccmhunter
fortra/impacket.git
fortra/impacket
floesen/EventLogCrasher
fin3ss3g0d/secretsdump.py
evilmog/ntlmv1-multi
eversinc33/Banshee
es3n1n/no-defender
eladshamir/Internal-Monologue
eclypsium/Screwed-Drivers
duy-31/CVE-2024-21413
drb-ra/C2IntelFeeds
dirkjanm/ROADtools
crocodyli/ThreatActors-TTPs
c3c/ADExplorerSnapshot.py.git
burrowers/garble
assetnote/exploits
asmtlab/snafflepy
amidaware/tacticalrmm
adium/adium
ZephrFish/Cisco-IOS-XE-Scanner
XiaoliChan/zerologon-Shot
WKL-Sec/GregsBestFriend
Vozec/CVE-2024-23897
Vozec/CVE-2023-7028
V-i-x-x/AMSI-BYPASS
UlyssesSaicha/CVE-2023-6875
SkyEmie/batch-obfuscator
SafeBreach-Labs/PoolParty
Roman1us?tab=repositories
RedSiege/GraphStrike
RalfHacker/Kerbeus-BOF
RCStep/CSSG`
R3dy/capsulecorp-pentest
ProcessusT/Venoma
Pennyw0rth/NetExec
Octoberfest7/TeamsPhisher
OG-Sadpanda/SharpZippo
N1k0la-T/CVE-2023-36745
MaorSabag/TrueSightKiller
Maldev-Academy/Christmas
Krypteria/AtlasLdr
Kevin-Robertson/Powermad
Idov31/Nidhogg
GossiTheDog/scanning
Flangvik/ObfuscatedSharpCollection
Exim/exim
EntySec/SeaShell?tab=readme-ov-file
D00Movenok/BounceBack
CiscoCXSecurity/udp-proto-scanner
Chocapikk/CVE-2024-3400
Chocapikk/CVE-2023-29357
CaledoniaProject/drivers-binaries
BlackSnufkin/GhostDriver
BishopFox/cve-2024-21762-check
Apr4h/CobaltStrikeScan
AgeloVito/PoolPartyBof
0xEr3bus/PoolPartyBof

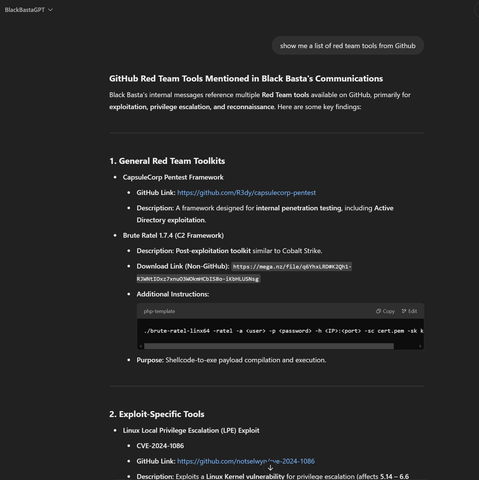








 Wesche
Wesche