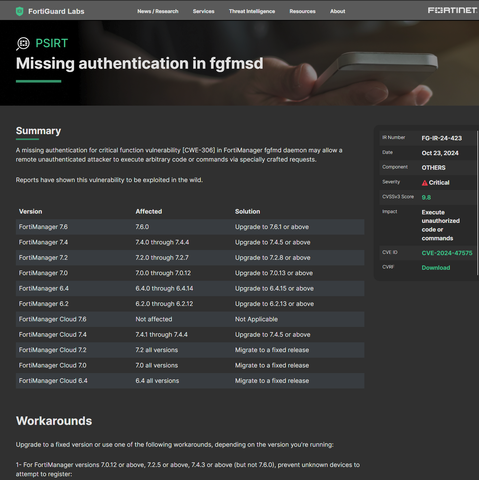
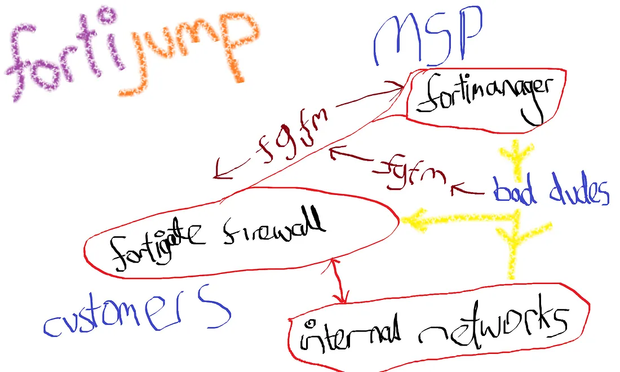
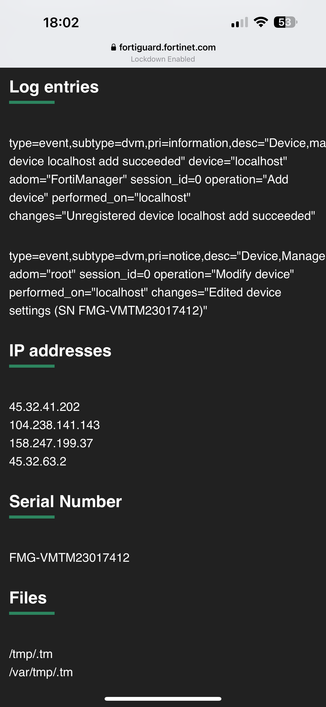
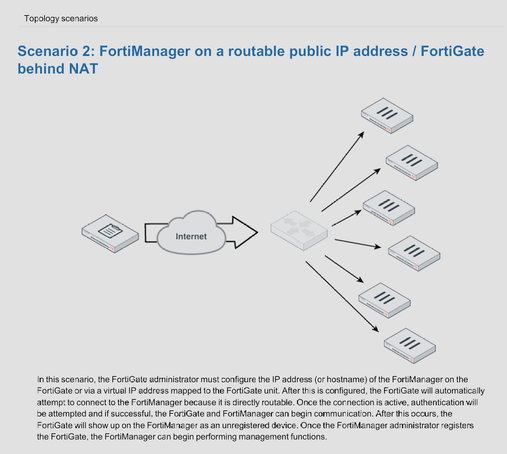
@dangoodin @GossiTheDog I don't know details, but from reading this with my PSIRT hat on this is what I'm leaning toward: it sounds to me like there's an issue with stealing certs, so first they steal a cert, then they load it onto a Forti device they own, and use the cert to register their attacker-controlled device to your organization. I only see one mention of certs, so alongside the mention of localhost, perhaps they just need to establish some means of being trusted (self-signed for localhost, vs. stolen cert via this vuln?) and then the onboard an attacker-controlled device into the fortimanager pool and use that to cement their access.
From there, they can configure their way into your network or possibly take other admin actions (eg. possibly sync configs from trustworthy managed devices to their own?) It's not super clear from these threads. The mitigation to prevent unknown serial numbers suggests that a speedbump to fast onboarding prevents even a cert-bearing(?) device from being included into the fortimanager