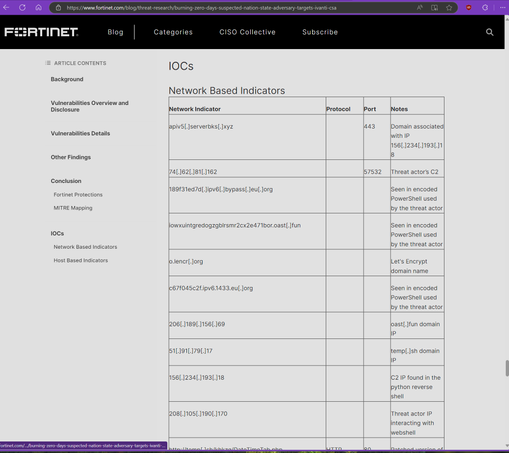
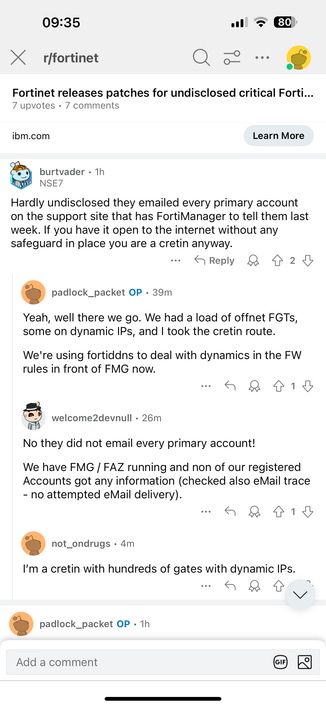
Hello everybody. If you use FortiManager from FortiNet you should be prepared to grab the latest available release from the support portal and upgrade.
Patches aren’t out yet. Mitigation is available. If you have FortiManager facing the internet, I’d say remove it from the internet now. #threatintel https://mastodon.green/@fthy/113299522822025433
fthy (@[email protected])
Patch your FortiManager now. Limit access to it to only from dedicated jump-servers. #fortinet #fortimanager #infosec