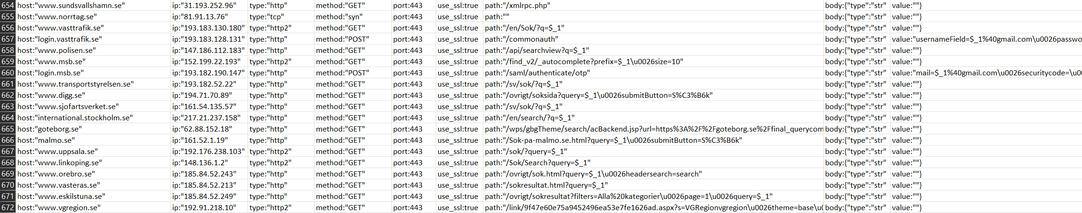
NoName057(16) are targeting the UK today, so I shall start monitoring them and naming their targets and attack types.
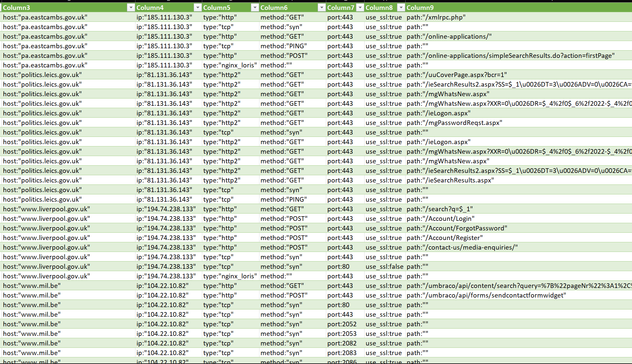
Their targeting: https://raw.githubusercontent.com/GossiTheDog/Monitoring/main/NoName/targets_2023_12_07_11am.txt
Currently:
pa.eastcambs.gov.uk
politics.leics.gov.uk
www.liverpool.gov.uk
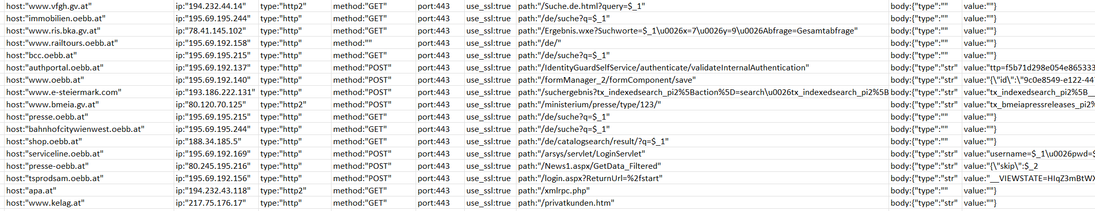
www.mil.be
www.bollington-tc.gov.uk
www.cranbrooktowncouncil.gov.uk
cert.be
my.swiftcard.org.uk
www.monarchie.be
www.premier.be
www.david-clarinval.be
www.dekamer.be
www.senaat.be
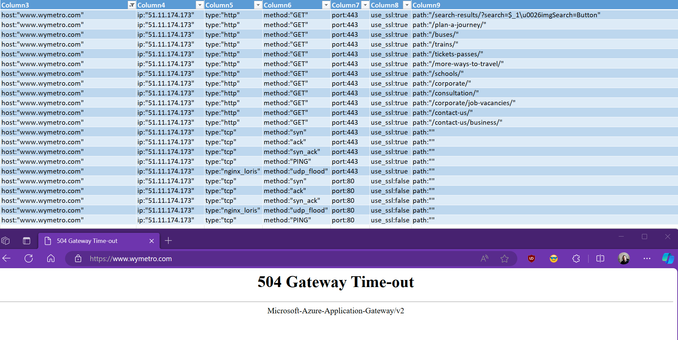



 glad I’m not traveling
glad I’m not traveling
 Why Not Zoidberg? 🦑
Why Not Zoidberg? 🦑
