the +64 ascii string thing doesn't work for all files. some of them end up negative
34 B6?
THAT DOESN'T MAKE ANY SENSE
interesting: logo.pac goes "40 3F 00 00 A7 AC AF A7 AF 9F 70 71 6E B4 A9 AD 60 D4"
so my code was stopping after 40 3F.
but A7 AC AF A7 ... looks more like a filename
the 40 3f 00 00 before the filename in LOGO.PAC isn't part of the filename, it's part of the header.
I can't figure out how it's determining when filenames end, though.
Maybe it's assuming they all have extensions and all extensions are 3 letters long?
found the code where it parses the PAC headers.
It's terrible as expected.
The pre-pac header stuff gives you a pointer into each header, but then the fun part is that the pointer is not to the beginning, it's to the middle. So it looks things up by indexing forward AND backward
and here's how it determines the ending: it's until it hits a 0, OR the filename ends up being 12 characters long.
FUCK
someday I'm gonna reverse engineer a game and not want to timetravel back to its creation and ask them WHAT THE FUCK at gunpoint
sometimes I won't even ask, I'll just start shooting
so I'm just gonna take all my current PAC parsing code and throw it out and replace it with the nonsense of the actual code.
that was my fatal mistake: I was writing parsing code assuming this shit made any fucking sense
it seems to be trying to ensure all filenames are uppercase, but because it's wrong, it is corrupting all non-lowercase characters.
now to try to figure out what the fuck it does
this decompression routine is big-endian.
on a little-endian system.
it seems it's loading 16bit lengths, then using the top 15 bits? with the lowest bit as a flag?
I don't recognize this. I don't think it's DEFLATE
so looking at this code, it doesn't seem to involve huffman encoding. there's no tables, just some look-back with a sliding (I think?) window.
So this is just a slightly fancy RLE, I think?
Bingo. it works!
Mostly. my output file is always 64mb but that's because I don't have a good way to tell how big it should be
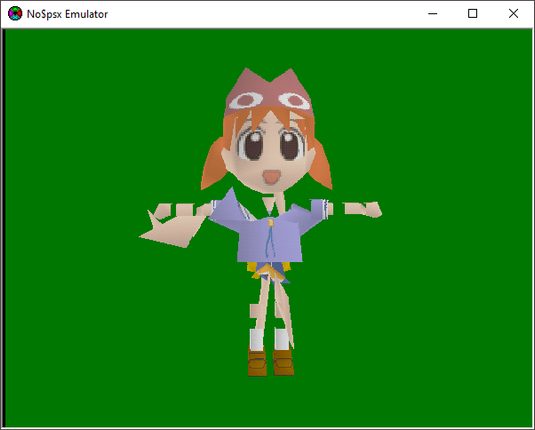
I have textures now.
As far as I can tell, there's no code that handles chunk-36.
So the only way that makes sense is if part of the game dynamically loads code which then registers a chunk-36 parser
So like, the first Chiyo-chan is chi_v.pac
That PAC file contains 91 texture images and a 95 kilobyte GMD file, which seems to contain all the geometry AND animations.
Fortunately I know where the function that parses it starts
the code also seems to handle decoding two versions of the GMD format, but I can only find one in use in the datafiles.
Maybe they used the other in the One Piece games, and just never dropped support?
I bet versions 1 and 0 appear inside version 2
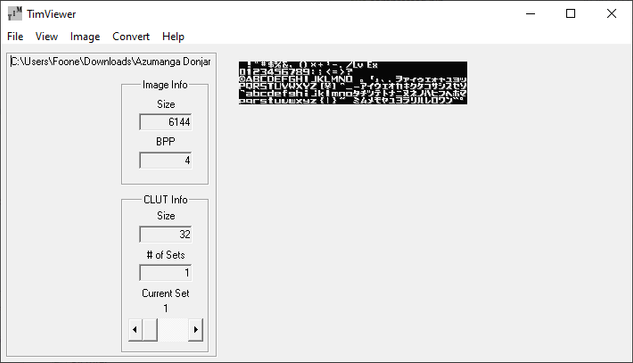
interesting string:
"This is Technosoft\'s communication shell password"
Technosoft is the company that game before Ganbarion. Apparently they built some kind of communication shell utility for their PS1 games
ugh I'm not being paid enough for this.
so it seems there's a complex function-pointer system used so that the main loop can stay the same, and it can be overwritten by overlays loaded from the APF files
return (int)*(short *)(**(int **)(*(int *)(param_1 + 0xc) + 0x14) + 0x10);
C is such a simple and expressive language
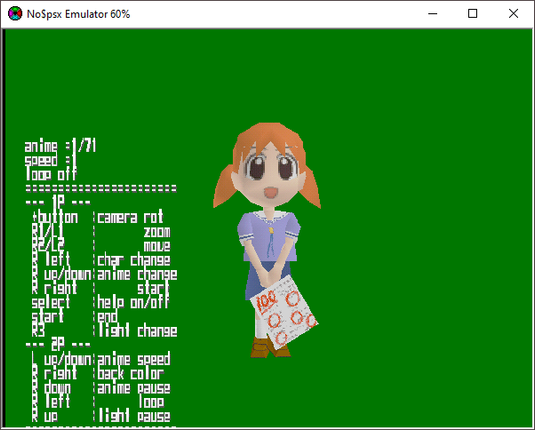
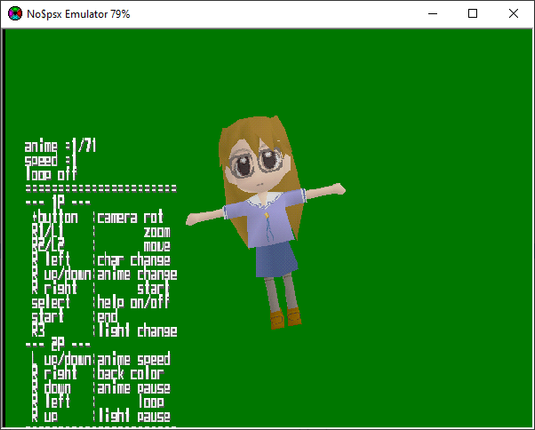
okay I have figured out where most of the controller logic for the char viewer is, and thus I know which function is called when it needs to load a new character
but reversing that will have to wait until tomorrow. I am fried
load_new_character
I keep tracing through a complicated tree of functions in the overlay, then discovering an identical set of functions in the non-overlay.
Could be something like that.
But when a PAC file needs to be loaded for a special reason, you can pass a different pac-chunk
-handler-list.
I'm now at the "corrupt data while it's being loaded and see what breaks" stage of reverse engineering.
I haven't learned much, but I do now know a bunch of a bytes you shouldn't change or "the polygons will get all fucked"
the vertex/index stride value
the vertex/index offset
the surface format (i'm surprised they'd let you use anything other than "triangles")
So, basically the stage neurology was at when they were guessing what bits of the brain do by seeing what was fucked up in people with various head injuries.
okay I've got it down to the point of being able to fuck up a single triangle.
that's a lot of progress! now I can try to figure out what format these coordinates are in
So it uses a shared-vertex system, apparently?
go it. the 01 I was messing with was actually the second byte: 00 01.
as in, 256.
offset 256 is where the vertex list starts.
so I dumped the vertex list into MeshLab and it turns out... it looks nothing like Chiyo-Chan.
SO I think that means that the points are relative to each body part?
so I've discovered that by changing the render_flags at 80063a80 so that it's 0x100, you can make the debug screen display "MEM8".
That's all it does. the 8 never changes. it's hardcoded.
I'm not sure what this is for.
I think under some situations the horizontal position might change. like, maybe if it's lower on RAM, the position will be more to the left?
so I guess if you wired up an external way to trigger the debug mode, so you break into the debug mode and see how much RAM the game had available at that point

 Ibly 🏳️⚧️
Ibly 🏳️⚧️