chunk IDs 0-31 use a 3-parameter callback, and 32-47 use a 4-parameter callback
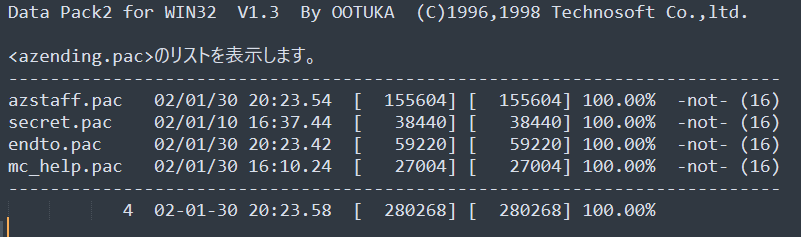
Data Pack2 by OOTUKA, Technosoft Co LTD, eh?
It's possible he's OOTUKA.
because while it's not 100% correct (they changed shit after this file was made), it's still partially correct: azending.pac DOES include endto.pac, in it's entirety
so PAC is a lazy TAR clone
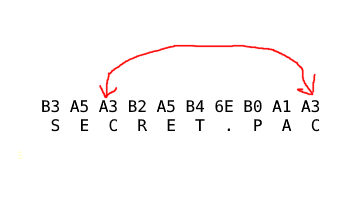
B3 A5 A3 B2 A5 B4 6E B0 A1 A3
it does decode as shift-jis (which the text file was encoded as) but turns into:
ウ・」イ・エー。」
which I don't think makes any sense
and if you decode it as utf-16, the most reasonable encoding for windows computers at the time, you end up with ꖳ늣뒥끮ꎡ, which makes even less sense.
I'm pretty sure they didn't name the files in their Azumanga Daioh game in a mix of Mande, Korean, and Sino-Tibetan scripts
the "C" in "SECRET" is encoded the same as the "C" in "PAC"
And note that the A in PAC is encoded as A1, which is only 2 less than the A3 which C is encoded as.
answer: nothing python 3.11 can encode to.
Maybe this isn't an encoding. Maybe this is encryption.
B3 A5 A3 B2 A5 B4 6E B0 A1 A3
subtract 64 from each letter
>>> ''.join(chr(x-64) for x in [0xB3,0xA5,0xA3,0xB2,0xA5,0xB4,0x6E,0xB0,0xA1,0xA3])
'secret.pac'
the header for the file itself is 16 bytes.
Then each chunk starts with a null-terminated string, encoded with that silly +64 ASCII mode.
Then there's another NUL byte, then 32 bytes of per-chunk header, then the raw chunk data.
the +64 ascii string thing doesn't work for all files. some of them end up negative
34 B6?
THAT DOESN'T MAKE ANY SENSE
interesting: logo.pac goes "40 3F 00 00 A7 AC AF A7 AF 9F 70 71 6E B4 A9 AD 60 D4"
so my code was stopping after 40 3F.
but A7 AC AF A7 ... looks more like a filename
the 40 3f 00 00 before the filename in LOGO.PAC isn't part of the filename, it's part of the header.
I can't figure out how it's determining when filenames end, though.
Maybe it's assuming they all have extensions and all extensions are 3 letters long?
found the code where it parses the PAC headers.
It's terrible as expected.
The pre-pac header stuff gives you a pointer into each header, but then the fun part is that the pointer is not to the beginning, it's to the middle. So it looks things up by indexing forward AND backward
and here's how it determines the ending: it's until it hits a 0, OR the filename ends up being 12 characters long.
FUCK
someday I'm gonna reverse engineer a game and not want to timetravel back to its creation and ask them WHAT THE FUCK at gunpoint
sometimes I won't even ask, I'll just start shooting
so I'm just gonna take all my current PAC parsing code and throw it out and replace it with the nonsense of the actual code.
that was my fatal mistake: I was writing parsing code assuming this shit made any fucking sense
it seems to be trying to ensure all filenames are uppercase, but because it's wrong, it is corrupting all non-lowercase characters.
now to try to figure out what the fuck it does
this decompression routine is big-endian.
on a little-endian system.
it seems it's loading 16bit lengths, then using the top 15 bits? with the lowest bit as a flag?
I don't recognize this. I don't think it's DEFLATE
so looking at this code, it doesn't seem to involve huffman encoding. there's no tables, just some look-back with a sliding (I think?) window.
So this is just a slightly fancy RLE, I think?
Bingo. it works!
Mostly. my output file is always 64mb but that's because I don't have a good way to tell how big it should be
I have textures now.
As far as I can tell, there's no code that handles chunk-36.
So the only way that makes sense is if part of the game dynamically loads code which then registers a chunk-36 parser
So like, the first Chiyo-chan is chi_v.pac
That PAC file contains 91 texture images and a 95 kilobyte GMD file, which seems to contain all the geometry AND animations.
Fortunately I know where the function that parses it starts
the code also seems to handle decoding two versions of the GMD format, but I can only find one in use in the datafiles.
Maybe they used the other in the One Piece games, and just never dropped support?
I bet versions 1 and 0 appear inside version 2
Is this encryption dot gif