@paul everyone is saying Tailscale, but the self-host version is Headscale, and is compatible with the Tailscale clients
Tailscale!
@paul A little nuanced, but I'd recommend either Wireguard (which has the advantage of supporting auto-connection on foreign Wifi) or Tailscale (which is comparatively far easier to set up)
Happy to discuss more if you have interest.
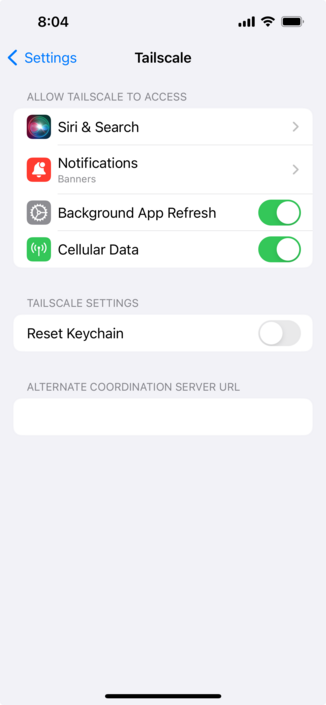
As of 1.48, released 3 days ago, TailScale supports VPN on Demand.
My apologies. I leave my exit node enabled all the time and never toggle it off so my quick test I did just now leaves it enabled.
But if you have it disabled then, no, there is no way to tell it to re-enable a specific node.
@caseyliss @paul I just set Wireguard up at home with the GL.iNet Beryl you recently recommended for travel and their Brume 2 for the home client/server.
It was super simple. I’m shocked to hear Tailscale is simpler?
@paul pfsense supports openvpn, ipsec and wireguard - https://docs.netgate.com/pfsense/en/latest/vpn/index.html
I've used ipsec and openvpn: ipsec has builtin vpn client in macOS, two others require clients. openvpn for macos is https://www.sparklabs.com/viscosity/ (paid) and wireguard is in the app store. not sure if ipsec will work with floating IP; but openvpn and wireguard works fine with these.
@paul I just setup Wireguard and it was super simple and so much faster than an VPN I’ve used before.
Probably should say “snappier” since I have no metrics to back it up 😅
GitHub - hwdsl2/setup-ipsec-vpn: Scripts to build your own IPsec VPN server, with IPsec/L2TP, Cisco IPsec and IKEv2
Scripts to build your own IPsec VPN server, with IPsec/L2TP, Cisco IPsec and IKEv2 - GitHub - hwdsl2/setup-ipsec-vpn: Scripts to build your own IPsec VPN server, with IPsec/L2TP, Cisco IPsec and IKEv2
@paul wiregurd, v2ray, snell
All works fine

 🦆
🦆










 Caleb
Caleb