We have a winner already - CVE-2023-35078, zero day in #MobileIron aka Ivanti Endpoint Manager Mobile
Exploitation in the wild. #threatintel
https://forums.ivanti.com/s/article/KB-Remote-unauthenticated-API-access-vulnerability-CVE-2023-35078
⚠️ Regarding the #MobileIron vulnerability ⚠️
Patches are out for 11.8.1.1, 11.9.1.1 and 11.10.0.2. It also applies to unsupported and EOL versions.
It's a serious zero day vulnerability which is very easy to exploit, where Ivanti are trying to hide it for some reason - this will get mass internet swept. I'd strongly recommend upgrading, and if you can’t get off EOL, switch off the appliance.
Heise have picked up on the #MobileIron zero day. It's under active exploitation, Ivanti have put security information behind a paywall portal and hidden exploitation information behind a non-disclosure agreement.
Ivanti are also a security vendor.
cc @wdormann https://www.heise.de/news/Ivanti-schliesst-Zero-Day-Luecke-in-MobileIron-9225583.html
The #MobileIron advisory is now public. Cyberbullying vendors into doing the right thing is my community service.
CVSS 10. “Remote unauthenticated API access”. #threatintel
This one is completely nuts btw, I set up a honeypot and it’s already being probed via the API - which allows admin access and is completely unauthenticated, apparently nobody ever pentested one of the most widely used MDM solutions.
Norway says Ivanti zero-day was used to hack govt IT systems
The Norwegian National Security Authority (NSM) has confirmed that attackers used a zero-day vulnerability in Ivanti's Endpoint Manager Mobile (EPMM) solution to breach a software platform used by 12 ministries in the country.
The #MobileIron zero day saga continues.
The vendor note to customers says the flaw allows the attacker to "make limited changes to the server".
CISA have released a statement saying "An attacker can also make other configuration changes, including creating an EPMM administrative account that can make further changes to a vulnerable system"
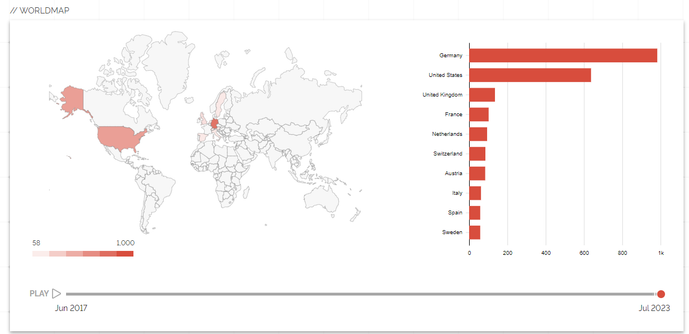
Here's a track of MobileIron/EPMM deployment worldwide.
It's hotter than The Hoff in Germany.
A vast majority of orgs haven't patched. Orgs include 10 Downing Street, large swathes of the US government etc.
https://doublepulsar.com/mobileirony-backdoor-allows-complete-takeover-of-mobile-security-product-and-endpoints-559733d612e1?sk=4915c0011cfce52e58d3ab81d9bb2373
The #MobileIrony API endpoint is now public knowledge - it’s /mifs/aad/
Yes, you just added to add ‘aad’ to access the admin API without auth and it’s been like that for years.
https://github.com/projectdiscovery/nuclei-templates/blob/main/http/cves/2023/CVE-2023-35078.yaml
CISA advisory says the zero day exploitation of #MobileIron was happening from "at least" April 2023 (which backs up from I wrote in my blog - i.e. I can see exploitation in logs going back to early this year).
Threat actors were uploading webshells and such. #threatintel #mobileirony
https://www.cisa.gov/news-events/cybersecurity-advisories/aa23-213a
@GossiTheDog nice! I feel like it was good timing for us to move from #Nessus to #Nuclei for our automated network-wide scans last week.
It’s been great to see just how agile the community behind Nuclei is. Nessus never felt like that, probably due to the poorer onboarding experience for users and developers alike.
@GossiTheDog
NOICE
Excellent write-up, quite an own-goal for a security firm to pull something like this, and certainly not a company that'd I'd recommend to a client.
@GossiTheDog @Newk "As far as I can see, Ivanti have no telemetry on every API endpoint request — so simply may well not know how many customers were impacted."
Oh look, it's "we've seen no evidence of exploitation [because we haven't and can't look for any]"
Impressive.
"Many years ago, MobileIron aka Ivanti Endpoint Manager Mobile (EPMM) gained support for AzureAD integration in a product update, allowing the device is be Azure AD domain joined. It appears this code introduced the vulnerability, as it allowed unrestricted remote access to the entire MobileIron API as an admin user — without suppling any credentials."





 🇺🇦
🇺🇦