We have a winner already - CVE-2023-35078, zero day in #MobileIron aka Ivanti Endpoint Manager Mobile
Exploitation in the wild. #threatintel
https://forums.ivanti.com/s/article/KB-Remote-unauthenticated-API-access-vulnerability-CVE-2023-35078
⚠️ Regarding the #MobileIron vulnerability ⚠️
Patches are out for 11.8.1.1, 11.9.1.1 and 11.10.0.2. It also applies to unsupported and EOL versions.
It's a serious zero day vulnerability which is very easy to exploit, where Ivanti are trying to hide it for some reason - this will get mass internet swept. I'd strongly recommend upgrading, and if you can’t get off EOL, switch off the appliance.
Heise have picked up on the #MobileIron zero day. It's under active exploitation, Ivanti have put security information behind a paywall portal and hidden exploitation information behind a non-disclosure agreement.
Ivanti are also a security vendor.
cc @wdormann https://www.heise.de/news/Ivanti-schliesst-Zero-Day-Luecke-in-MobileIron-9225583.html
The #MobileIron advisory is now public. Cyberbullying vendors into doing the right thing is my community service.
CVSS 10. “Remote unauthenticated API access”. #threatintel
This one is completely nuts btw, I set up a honeypot and it’s already being probed via the API - which allows admin access and is completely unauthenticated, apparently nobody ever pentested one of the most widely used MDM solutions.
Norway says Ivanti zero-day was used to hack govt IT systems
The Norwegian National Security Authority (NSM) has confirmed that attackers used a zero-day vulnerability in Ivanti's Endpoint Manager Mobile (EPMM) solution to breach a software platform used by 12 ministries in the country.
The #MobileIron zero day saga continues.
The vendor note to customers says the flaw allows the attacker to "make limited changes to the server".
CISA have released a statement saying "An attacker can also make other configuration changes, including creating an EPMM administrative account that can make further changes to a vulnerable system"
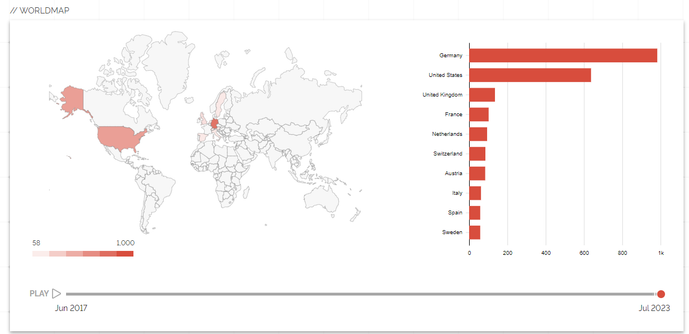
Here's a track of MobileIron/EPMM deployment worldwide.
It's hotter than The Hoff in Germany.
A vast majority of orgs haven't patched. Orgs include 10 Downing Street, large swathes of the US government etc.
https://doublepulsar.com/mobileirony-backdoor-allows-complete-takeover-of-mobile-security-product-and-endpoints-559733d612e1?sk=4915c0011cfce52e58d3ab81d9bb2373
The #MobileIrony API endpoint is now public knowledge - it’s /mifs/aad/
Yes, you just added to add ‘aad’ to access the admin API without auth and it’s been like that for years.
https://github.com/projectdiscovery/nuclei-templates/blob/main/http/cves/2023/CVE-2023-35078.yaml