The new team in charge of the FTX bankruptcy have released their first interim report on the failures of control at FTX and related businesses.
It's 43 pages long, let's go through it 🧵
https://www.courtlistener.com/docket/65748821/1242/1/ftx-trading-ltd/
#FTX #FTXcollapse

Exhibit A – #1242, Att. #1 in FTX Trading Ltd. (Bankr. D. Del., 22-11068) – CourtListener.com
Exhibit(s) (Notice of Filing First Interim Report of John J. Ray III to the Independent Directors on Control Failures at the FTX Exchanges) Filed by FTX Trading Ltd.. (Attachments: # 1 Exhibit A) (Pierce, Matthew) (Entered: 04/09/2023)
The debtors reiterate the stunning lack of recordkeeping and controls at FTX: "Normally, in a bankruptcy involving a business of the size and complexity of the FTX Group, particularly a business that handles customer and investor funds, there are readily identifiable records, data sources, and processes that can be used to identify and safeguard assets of the estate. Not so with the FTX Group."
"Upon assuming control, the Debtors found a pervasive lack of records and other evidence at the FTX Group of where or how fiat currency and digital assets could be found or accessed, and extensive commingling of assets."
FTX executives "stifled dissent, commingled and misused corporate and customer funds, lied to third parties about their business, [and] joked internally about their tendency to lose track of millions of dollars in assets"
Debtors are having to cobble together financial records from what they're able to find in QuickBooks and Slack records 💀
It sounds like the debtors are limited somewhat by the fact that laptops belonging to SBF and other high-level insiders are currently in the hands of the Bahamian Joint Provisional Liquidators, who've been less than cooperative (according to the US team, at least).
Nishad Singh, Gary Wang, and Caroline Ellison have all pled guilty and are cooperating with the DOJ, making it infeasible for the debtors to interview them for bankruptcy purposes until after the criminal trial is over. They have interviewed others, though.
"The FTX Group lacked independent or experienced finance, accounting, human resources, information security, or cybersecurity personnel or leadership, and lacked any internal audit function whatsoever. Board oversight, moreover, was also effectively non-existent."
“if Nishad [Singh] got hit by a bus, the whole company would be done. Same issue with Gary [Wang]."
Some new context on the sudden resignation of Brett Harrison in September 2022: he "resigned following a protracted disagreement", after which his bonus was drastically reduced.
In a separate instance, a lawyer who was hired only three months prior, who learned about the North Dimension bank accounts, was "summarily terminated after expressing concerns about Alameda’s lack of corporate controls, capable leadership, and risk management."
"At the time of the bankruptcy filing, the FTX Group did not even have current and complete lists of who its employees were."
"As a general matter, policies and procedures relating to accounting, financial reporting, treasury management, and risk management did not exist, were incomplete, or were highly generic and not appropriate for a firm handling substantial financial assets."
More QuickBooks shade.
"Fifty-six entities within the FTX Group did not produce financial statements of any kind. Thirty-five FTX Group entities used QuickBooks as their accounting system and relied on a hodgepodge of Google documents, Slack communications, shared drives, and Excel spreadsheets and other non-enterprise solutions to manage their assets and liabilities"
"Approximately 80,000 transactions were simply left as unprocessed accounting entries in catch-all QuickBooks accounts titled 'Ask My Accountant.'"
Sam Bankman-Fried: "Alameda is unauditable... we are only able to ballpark what its balances are, let alone something like a comprehensive transaction history. We sometimes find $50m of assets lying around that we lost track of; such is life"
"Thousands of deposit checks were collected from the FTX Group’s offices, some stale-dated for months, due to the failure of personnel to deposit checks in the ordinary course; instead, deposit checks collected like junk mail."
Transfers in the tens of millions of dollars were approved via Slack emoji, or discussed in disappearing Signal or Telegram chats.
"Only four months after the real estate purchase had closed did the employee enter into a promissory note with Alameda in which he undertook to repay the funds used to purchase the property. Other insiders received purported loans from Alameda for which no promissory notes exist."
Accounts were opened using names and email addresses that were not obviously linked to FTX, using pseudonymous email addresses, in the names of shell companies created for these purposes, or in the names of individuals (including individuals with no direct connection FTX)
"Alameda also transferred funds to insiders to fund personal investments, political contributions, and other expenditures—some of which were nominally 'papered' as personal loans with below-market interest rates and a balloon payment due years in the future."
The document reiterates known allegations about Alameda's "unique ability to trade and withdraw virtually unlimited assets [on FTX], regardless of the size of its account balance and without risk of its positions being liquidated."
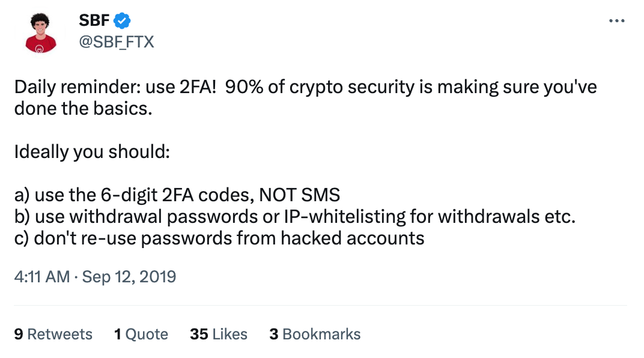
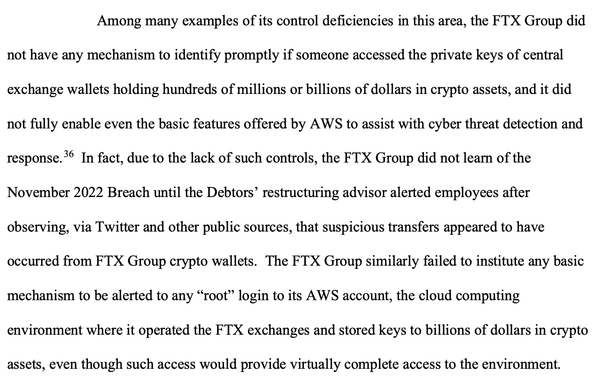
The FTX group had no cybersecurity staff whatsoever.
FTX stored private keys to its crypto wallets in AWS 🫠
"[FTX] kept virtually all crypto assets in hot wallets... [FTX] undoubtedly recognized how a prudent crypto exchange should operate, because when asked by third parties to describe the extent to which it used cold storage, it lied."