https://virtualize.sh/blog/vmscape-and-why-xen-dodged-it/ #ETHZürich #VMScape #cybersecurity #Xen #HackerNews #ngated
https://virtualize.sh/blog/vmscape-and-why-xen-dodged-it/ #ETHZürich #VMScape #cybersecurity #Xen #HackerNews #ngated
VMScape and why Xen dodged it
https://virtualize.sh/blog/vmscape-and-why-xen-dodged-it/
#HackerNews #VMScape #Xen #Virtualization #Tech #News #Analysis
L'attaque VMScape casse l'isolation des VM sur les puces AMD et Intel
https://www.lemondeinformatique.fr/actualites/lire-l-attaque-vmscape-casse-l-isolation-des-vm-sur-les-puces-amd-et-intel-97864.html
#Infosec #Security #Cybersecurity #CeptBiro #VMScape #VM #PucesAMD #Intel
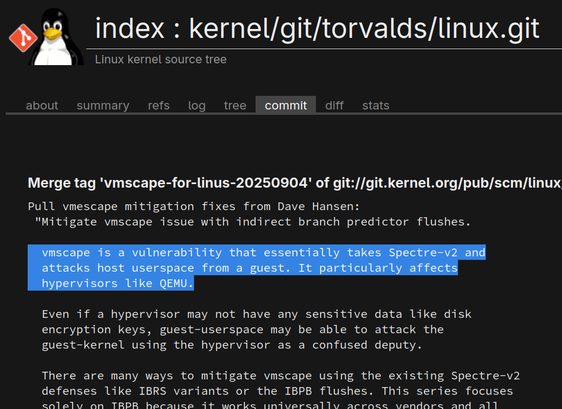
Mitigations for #vmscape have been merged to #Linux mainline and included in new stable and longterm #kernel versions released about an hour ago (like 6.16.7 or 6.12.47).
Vmscape is a vulnerability that essentially takes Spectre-v2 and attacks host userspace from a guest. It particularly affects hypervisors like #QEMU.
For more details see this #LinuxKernel merge commit https://git.kernel.org/torvalds/c/223ba8ee0a3986718c874b66ed24e7f87f6b8124, the doc changes in contains at https://git.kernel.org/torvalds/c/9969779d0803f5dcd4460ae7aca2bc3fd91bff12, or the following page from those that published the vulnerability:
It is tracked as #CVE-2025-40300
Virtualized environments may no longer be as safe as we thought. The new VMScape vulnerability lets guest systems peek into host data by exploiting shared CPU predictions. How vulnerable is your cloud?
https://thedefendopsdiaries.com/vmscape-attack-a-new-threat-to-virtualized-environments/
#vmscape
#virtualizationsecurity
#cloudsecurity
#cyberthreats
#amdintelvulnerability