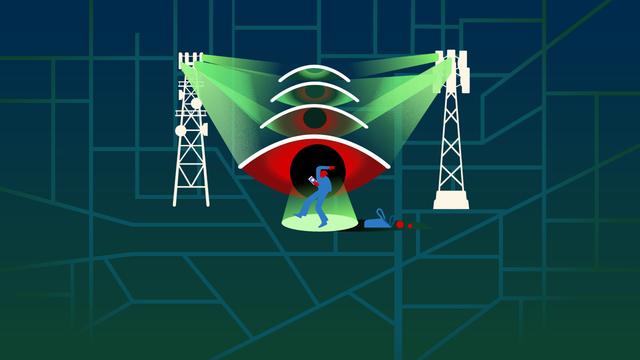
Bad Connection
Uncovering Global Telecom Exploitation by Covert Surveillance Actors https://citizenlab.ca/research/uncovering-global-telecom-exploitation-by-covert-surveillance-actors/
An investigation by the Citizen Lab Team, which uncovers two sophisticated telecom surveillance campaigns and, for the first time, directly links real-world attack traffic to mobile operator signalling infrastructure.
#CyberSecurity #ThreatIntelligence #Surveillance #TelecomSecurity #MobileSecurity #SS7 #NetworkSecurity #CyberEspionage #CitizenLab #Infosec #Privacy #DigitalRights #CyberResearch #SignalInfrastructure #Telecom
 🐦🔥nemo™🐦⬛ 🇺🇦🍉
🐦🔥nemo™🐦⬛ 🇺🇦🍉