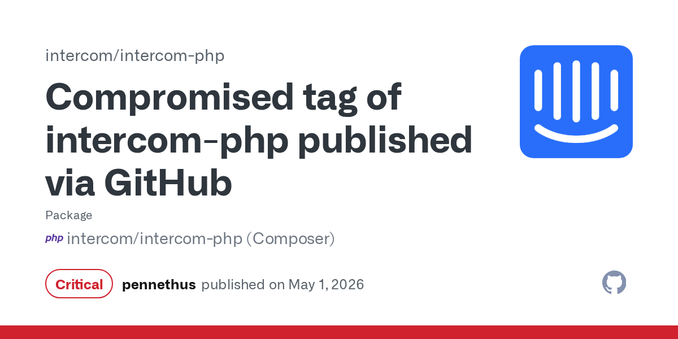
Kaspersky Uncovers Trojanized DAEMON Tools in Targeted Supply-Chain Attack
If you installed DAEMON Tools between April 8 and now, your system may be compromised - Kaspersky researchers warn that a highly sophisticated supply-chain attack has been delivering a backdoor to thousands of systems via trojanized installers. Check your machines for unusual activity and take action ASAP to…
#SupplyChainAttack #TrojanizedSoftware #DaemonTools #EmergingThreats #BackdoorMalware