Feed: All Latest | Disneyland Now Uses Face Recognition on Visitors by Lily Hay Newman, Andy Greenberg, Andrew Couts
AI generated summary, Read the full article for complete information.
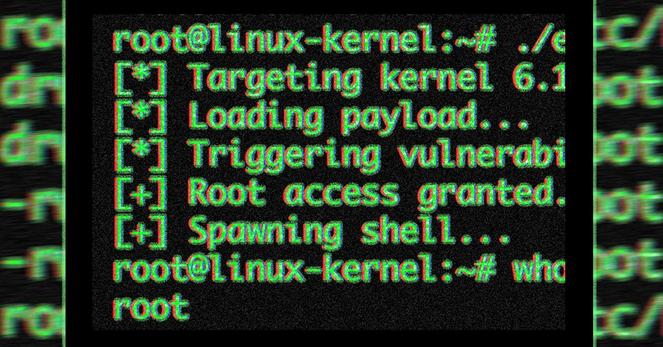
This week’s security roundup highlights a mix of privacy‑invasion developments and law‑enforcement actions: Disney announced optional facial‑recognition lanes at its California parks, promising to delete the numeric facial hashes after 30 days, while the FIDO Alliance, Google and Mastercard began drafting AI‑agent‑transaction guardrails and OpenAI rolled out an “advanced” risk‑mode for high‑threat ChatGPT/Codex accounts. The NSA, despite a pending Department‑of‑Defense ban on Anthropic, received early access to Anthropic’s Mythos AI‑bug‑hunting tool and is using it to scour Microsoft software for exploitable flaws. In criminal news, a 19‑year‑old alleged member of the Scattered Spider ransomware gang was arrested in Finland, and a gunman who tried to crash the White House Correspondents’ Dinner was jailed on federal assassination and firearms charges. A publicly exposed Medicare provider directory inadvertently leaked U.S. health‑care workers’ Social Security numbers, and new research revealed a massive spyware leak of 90,000 celebrity screenshots, underscoring the growing risks of commercial surveillance tools.
#Disneyland #FIDOAlliance #ScatteredSpider #security_cyberattacksandhacks #security_privacy #PeterStokes