https://trustedsec.com/blog/full-disclosure-a-third-and-fourth-azure-sign-in-log-bypass-found #MicrosoftAzure #SecurityBypass #WhackAMole #InfoSec #HackerNews #ngated
https://trustedsec.com/blog/full-disclosure-a-third-and-fourth-azure-sign-in-log-bypass-found #MicrosoftAzure #SecurityBypass #WhackAMole #InfoSec #HackerNews #ngated
Understanding Security Bypasses in Ubuntu's Unprivileged User Namespaces
#ubuntu
#securitybypass
#unprivilegedusernamespaces
#linuxsecurity
#apparmor
TunnelVision: The DHCP Decloaking Technique
Date: May 6, 2024
CVE: CVE-2024-3661
Vulnerability Type: Bypass a security feature
CWE: [[CWE-284]], [[CWE-400]]
Sources: Leviathan Security Blog
Issue Summary
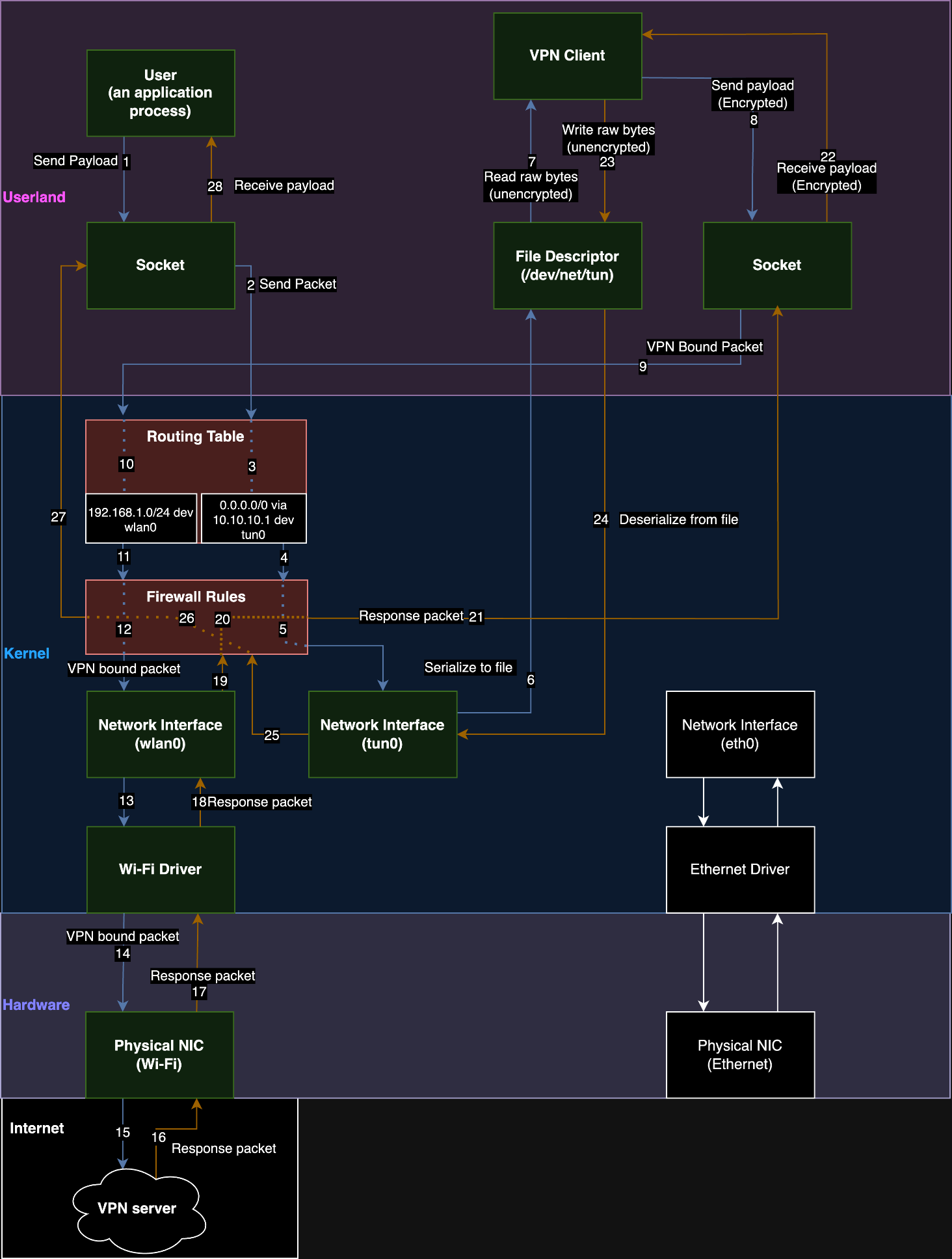
TunnelVision, a technique disclosed by Leviathan Security, involves bypassing VPN encryption using DHCP to decloak user traffic without disrupting the VPN control channel, which leaves VPN kill switches ineffective. This vulnerability utilizes DHCP option 121 to manipulate routing tables, allowing attackers to redirect selected traffic away from the secured VPN tunnel directly to themselves, making sensitive user data vulnerable to interception.
Technical Key Findings
Attackers use DHCP option 121 to insert malicious /1 routes into a victim's routing table, diverting specific traffic away from the encrypted VPN tunnel directly to the attacker because they are more specific than the /0 routes. This style of attack seems to be a slight variation on the "Poison Tap" attack from Samy Kamkar in 2016, where the same thing is done, but with a USB/Thunderbolt network adapter. Where they are plugged it into the victim device, advertise two more specific routes of 0.0.0.0/1 and 128.0.0.0/1 and then you get all the traffic in preference to other system interfaces despite interface ordering: https://github.com/samyk/poisontap
In 2002, RFC 3442 introduced option 121 classless static routes. It allows administrators to add classless static route ranges to a client’s routing table.
Requirements for decloaking VPN traffic
- The targeted host must accept a DHCP lease from the attacker-controlled server
- The targeted host’s DHCP client must implement DHCP option 121
- The client setup should lack firewall rules that block traffic to/from physical interface
Vulnerable Products
All operating systems supporting DHCP option 121, including Windows, Linux, iOS, and macOS. It does not affect Android as it does not support DHCP option 121.
Impact Assessment
Successful exploitation leads to potential traffic interception, jeopardizing sensitive data and enabling targeted denial-of-service and de-anonymization attacks.
Patches or Workaround
Mitigations include using network namespaces on Linux, enforcing strict firewall rules, or completely ignoring DHCP option 121 during active VPN connections.
Tags
#Networking #VPN #DHCP #CVE-2024-3661 #SecurityBypass #TrafficDecloaking
CVE-2024-3661: TunnelVision - How Attackers Can Decloak Routing-Based VPNs For a Total VPN Leak — Leviathan Security Group - Penetration Testing, Security Assessment, Risk Advisory
We discovered a fundamental design problem in VPNs and we're calling it TunnelVision. This problem lets someone see what you're doing online, even if you think you're safely using a VPN.
Near-miss today on negative-interaction with badland C&C -- Defender alerted on the web access.
Me: Did you have any interaction with odd emails around 7:05am CDT?
User: Yea, checking my personal email, accidentally clicked one as I was trying to delete it...
Me: You were checking your personal email on your work laptop - who's your provider? We block personal mail access at the web filter…
User: live.com -- I know that bypasses the filtering because of Microsoft - LOL!
The "LOL!" was their actual response.
They know can't filter MS URLs for shit or we'll break M365.
At least Defender caught (but not blocked) the destination…

