The focus is on USB, PCI, and other buses where devices can retain a persistent state and become attack vectors-even across reboots. The solution proposes that when an unauthorized device is detected, it should be excluded from the host system but made available to an isolated VM. The presentation goes into concrete design assumptions, and the technical details of how such port-level quarantine could be implemented in firmware and OS layers.
If your Qubes OS only shows a black screen after the suspend/resume, then follow these instructions: https://www.qubes-os.org/doc/suspend-resume-troubleshooting/#suspend-turns-off-the-screen-and-gets-stuck and expand the line like this: GRUB_CMDLINE_LINUX=“$GRUB_CMDLINE_LINUX rd.qubes.hide_all_usb mem_sleep_default=deep”.
This makes it much easier and is easy on the nerves.
#qubesos #instructions #Qubes_OS
Suspend/resume troubleshooting
First check if there are any remarks for similar devices in the Hardware Compatibility List (HCL). Network-Manager says “Device not ready” on suspend/resume These instructions may help with suspend/resume issues for more devices than just wireless cards, that is just the (unfortunately ...
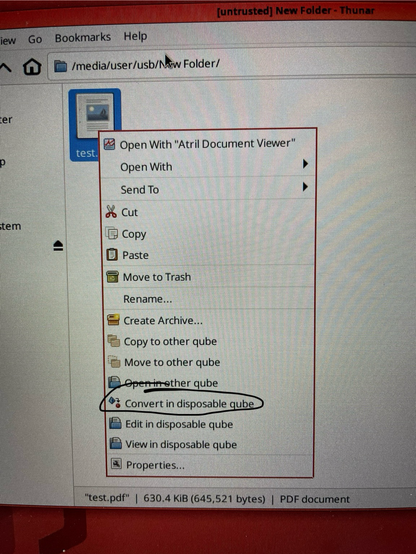
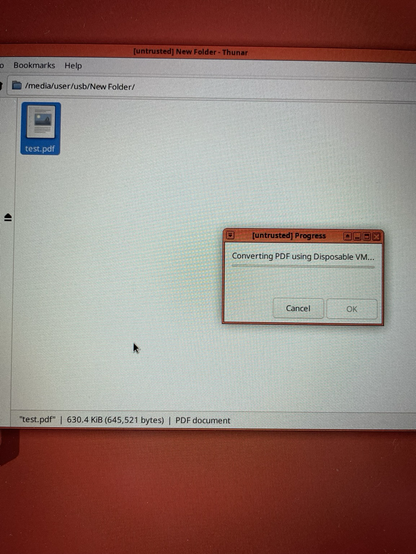
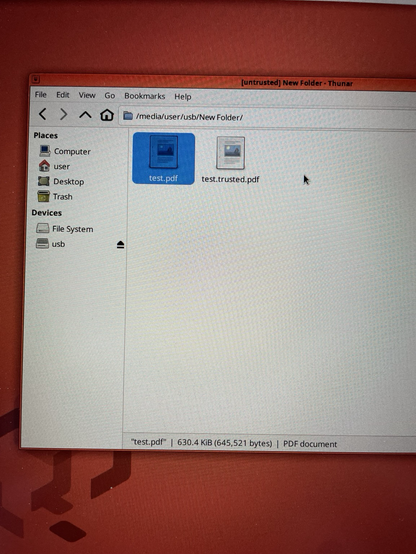
In Qubes OS i file pdf che si scaricano da internet (potenzialmente dannosi) possono essere convertiti tramite una vm monouso in pdf trusted, in pratica subiscono una conversione in Immagine in modo che eventuali codici malevoli di varia natura non vengano importati nella macchina .
@QubesOS
@[email protected] @linux
#privacy #untrustedinternet #pdf #Qubes_OS #linux #sicurezza
It's like qrexec-client-vm, but systemd-socket-activated.
It does TCP and Unix sockets. Includes a Split-SSH example and a new qubes.ConnectNFS RPC.
This is for my use cases (work in progress). Some might be your use cases. Feedback welcome.
Узнал про https://en.wikipedia.org/wiki/Qubes_OS , вроде интересное.
https://forum.qubes-os.org/t/installing-emacs-packages-on-template-qube/13877/3
Installing emacs packages on template qube
@enmus, thank you for considering the question. As far as I understood, none of emacs packages are listed in template available repositories. But it would be fantastic if I am wrong here. The repos I know for emacs are: elpa GNU ELPA Packages melpa Package Listing org Index of /elpa/ In the end, there is a way to tell emacs to use the qubes proxy (like in pip). Following: The code below worked on my emacs when placed on the init.el config file: (setq url-proxy-servi...