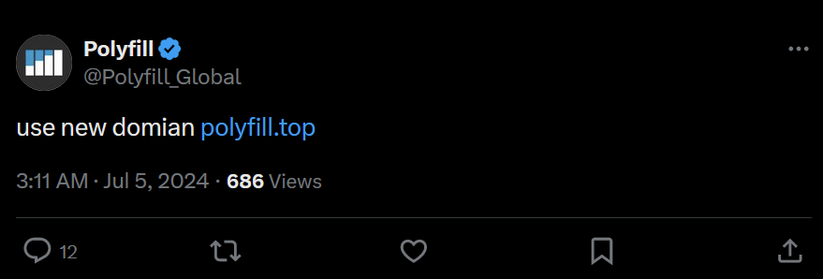
On July 5th, PolyfillIO switched to polyfill[.]top
This domain is currently unblocked by uBlock Origin and all major blocklists.
Tweet: https://x[.]com/Polyfill_Global/status/1809122842145141114
Thread with more information and also making fun of Windows users.
uBlock Origin has blocklisted polyfill[.]com
GitHub has placed a warning on the PolyfillIO repository (https://github.com/polyfillpolyfill/polyfill-service), and has denied access for non-logged in users. The other two repositories owned by that account are unblocked. Dismissing the warning appears to be permanent for an account.
PolyfillIO maintainer denies they are serving malicious JavaScript
Someone has maliciously defamed us. We have no supply chain risks because all content is statically cached. Any involvement of third parties could introduce potential risks to your website, but no one would do this as it would be jeopardize our own reputation.
https://github.com/polyfillpolyfill/polyfill-service/issues/2890#issuecomment-2191461961
@KarlE Warum das eine schlechte Idee ist, demonstriert gerade Polyfill.io.
If you're still using polyfill.io you probably want to replace/remove it IMMEDIATELY. The domain has been sold and the new owners are injecting #malware (1).
If you absolutely have to use externally hosted #JavaScript and #CSS, it's a good idea to secure it with #SubresourceIntegrity (2). It's supported by most old browsers you're probably polyfilling for.
(1) https://polykill.io/
(2) https://developer.mozilla.org/en-US/docs/Web/Security/Subresource_Integrity
Just added some more resources like old CNAME records, a link to archive org as well as a link to the GitHub thread discussing the payload.
Interesting part here: I haven't come across a second source for the payload yet. it always circles back to the GitHub issue from 5 days ago.
@GossiTheDog uBlock Origin has blocklisted PolyfillIO in it's badware list.
Add polyfill.io as badware due to supplychain attack by SISheogorath · Pull Request #24255 · uBlockOrigin/uAssets
URL(s) where the issue occurs polyfill.io / cdn.polyfill.io Describe the issue This patch adds polyfill.io to badware.txt due to an ongoing supplychain attack using the domain and its subdomains. R...