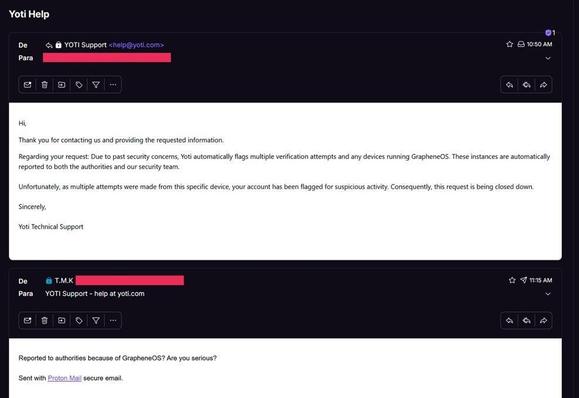
Czy F-Droid to wciąż synonim bezpiecznego Androida, czy już tylko ideologiczny relikt przeszłości? 🤖⚓
Choć w polskiej społeczności FOSS zielony robocik ma status kultowy, w zderzeniu z nowoczesną architekturą bezpieczeństwa (jak w GrapheneOS) zaczyna być najsłabszym ogniwem. Dlaczego `targetSdkVersion`, centralne podpisy i nawyki z desktopowego Linuksa stają się problemem?
Zapraszam do dyskusji i lektury mojego najnowszego wpisu o ewolucji zaufania w świecie mobile:
🔗 https://meridian.bearblog.dev/ewolucja-zaufania-dlaczego-czas-f-droida-mija/
#FDroid #GrapheneOS #Android #Privacy #FOSS #Cybersecurity #Obtainium #infosec #Security #DeGoogle #Prywatnosc #Bezpieczenstwo

 und rein in die echte Welt!
und rein in die echte Welt!