Recently, I wrote a write-up for the vulnerable machine from #VulNyx called Controler. It’s a medium-level #Windows machine. #Enumeration begins with the Kerberos account, which I use to gain initial system access. Through further Active Directory enumeration, I #exploit replication rights, ultimately extracting the Domain Administrator’s password hash and gaining full administrative control.
Solving this machine took me some time, but I learned a lot. I touched on new tools like #BloodHound, delved a bit deeper into Active Directory, and, in general, kept my #pentesting skills in check.
If you are starting in #cybersecurity, I would definitely recommend checking some VMs from VulNyx.
https://medium.com/@thecybercraft/vulnyx-controler-writeup-b9ada8e12fdd
Sekken-enum: tool for subdomain enumeration
A GitHub repo offering a tool to perform high-speed subdomain enumeration using wordlists, API integration, and recursive bruteforce.
STM32 Short #8 - Understanding USB Enumeration (re-enumeration)
In this videi we will cover the topic of USB Enumeration and how to trigger a USB Host to re-enumerate a STM32 USB Device (or Gadget).
#STM32 #Tutorial #STM32CubeIDE #STM32CubeMX #USB #Enumeration #STM32World
STM32 Short #8 - Understanding USB Enumeration (re-enumeration)
🤔 Ever wonder how to escape from a container? Or how security tools know what permissions they have from inside that same container? It's nice to have a great script for #enumeration ... but what does it check for and why does it matter?
Who am I? - Let’s get oriented and figure out what we have in our container. (https://some-natalie.dev/container-escapes-whoami/)
Our shared kernel - #Containers are processes that share a kernel. What can we see about our host? (https://some-natalie.dev/container-escapes-shared-kernel/)
Are we capable? - What sort of capabilities do we have? (https://some-natalie.dev/container-escapes-capabilities/)
Seccomp is your friend - #Seccomp filters what a container can do. Let’s learn what’s been set for us. (https://some-natalie.dev/container-escapes-seccomp/)
Are we in a microVM? - With #microVM runtimes gaining popularity, how do you know if you’re in a container? (https://some-natalie.dev/blog/microvm-or-container/)
(or, I did a little editing and put my workshop from @appsec_village at #DEFCON33 up) 
Subdomain enumeration is an essential OSINT technique. Amass and Subfinder are well-known enumeration tools, but they have limitations. Explore this comprehensive database with over 200 sources.
https://osintteam.com/passive-subdomain-enumeration-uncovering-more-subdomains-than-subfinder-amass/
Finally finished implementing the functionality of the PS function for #Enumeration that I've been working on since I saw some flaws in the currently existing tools while studying for #CRTE
It's focused on trying to show interesting ACLs without overwhelming you with lots of useless information. There's probably something out there that does that already (Find-InteterestingDomainAcl is supposed to do the trick but it's still too verbose for me). However, I needed an excuse to dive deeper into ACLs 😜
After cleaning the current monolith of PS scripting and allowing @maikel to peer review it, I'll publish it ☺️
https://www.linux-magazine.com/Issues/2025/290/Enumerating-Resources
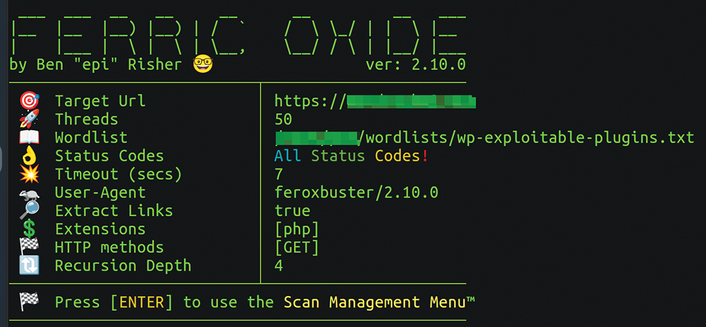
#security #tools #feroxbuster #ffuf #enumeration #cyberattack #automation #fuzzing
Title of the day: "generatingfunctionology"
https://www.youtube.com/watch?v=QwxaRPuJkyU
#tracking #capital surveillance #enumeration #ever cookie