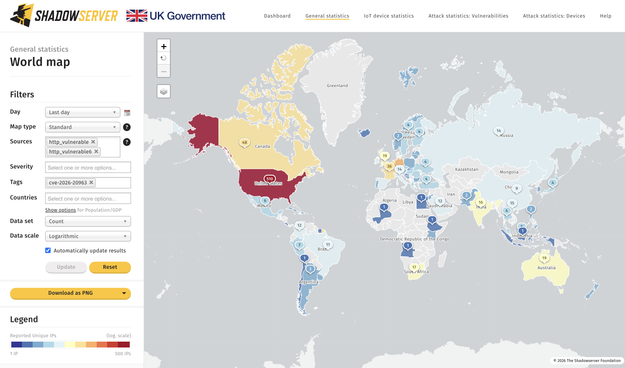
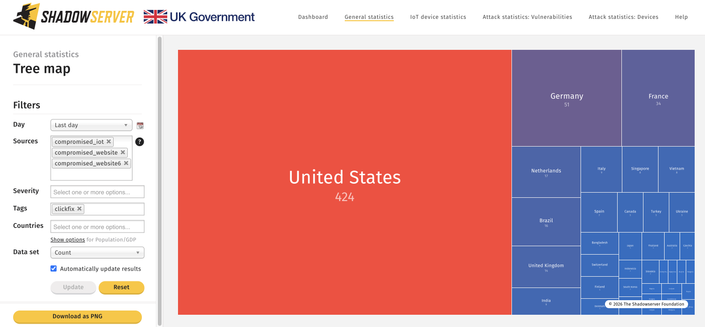
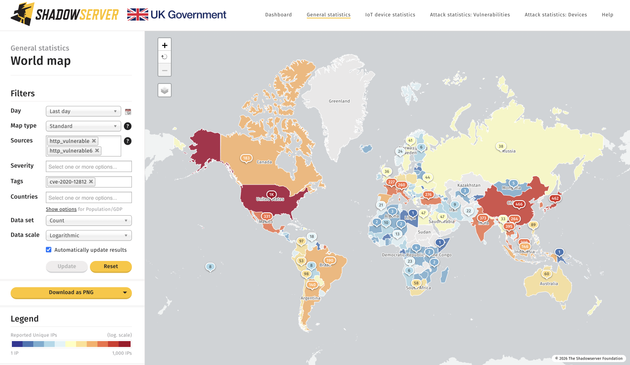
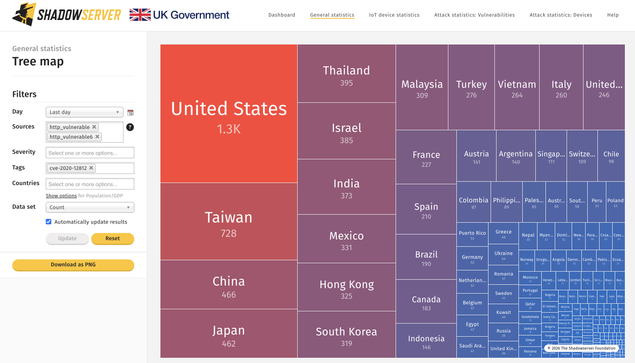
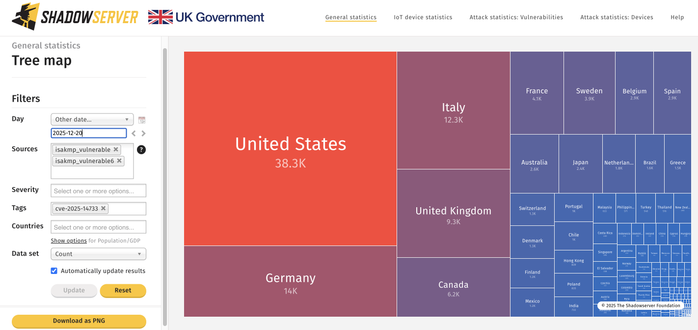
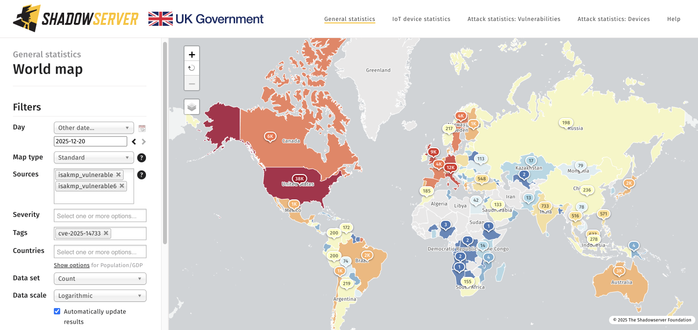
We added Microsoft SharePoint CVE-2026-20963 (post-auth deserialization RCE) to our scanning & daily feeds. 1109 IPs found running vulnerable instances worldwide (close to 1900 FQDNs) on 2026-03-19, with 510 IPs in the US.
Vulnerable IPs (tagged 'cve-2026-20963') shared daily in our Vulnerable HTTP reporting: https://www.shadowserver.org/what-we-do/network-reporting/vulnerable-http-report/
CVE-2026-20963 is known exploited in the wild and on US CISA KEV: https://www.cisa.gov/known-exploited-vulnerabilities-catalog?search_api_fulltext=CVE-2026-20963
Check for compromise.
Microsoft Advisory: https://msrc.microsoft.com/update-guide/vulnerability/CVE-2026-20963
CVE-2026-20963 Dashboard Tracker: https://dashboard.shadowserver.org/statistics/combined/time-series/?date_range=7&source=http_vulnerable&source=http_vulnerable6&tag=cve-2026-20963%2B&dataset=unique_ips&limit=100&group_by=geo&stacking=stacked&auto_update=on
Dashboard Tree Map view: https://dashboard.shadowserver.org/statistics/combined/tree/?date_range=1&source=http_vulnerable&source=http_vulnerable6&tag=cve-2026-20963%2B&data_set=count&scale=log&auto_update=on