We added a feed of IPs/websites with ClickFix/ClearFake injected code in our Compromised Website reporting, tagged as 'clickfix'. Visitors of the website get tricked to install malware when injected JavaScript executes. If you receive an alert review for root cause of compromise!
657 instances shared for 2026-03-14. We expect to increase the volume of the feed in the future!
We would like to thank our Alliance partners and Validin for the collaboration making this possible!
Background on investigating ClickFix/ClearFake: https://www.atea.no/siste-nytt/it-sikkerhet/investigating-a-clearfake-clickfix-etherhide-campaign/
Compromised Website Report: https://www.shadowserver.org/what-we-do/network-reporting/compromised-website-report/
Dashboard World Map view of infected IPs:
https://dashboard.shadowserver.org/statistics/combined/map/?date_range=1&map_type=std&source=compromised_iot&source=compromised_website&source=compromised_website6&tag=clickfix&data_set=count&scale=log&auto_update=on
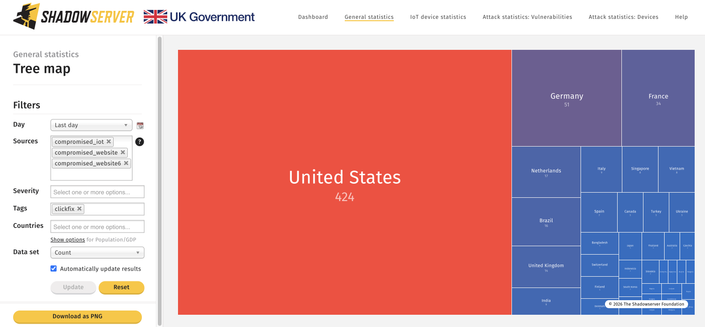
Dashboard Tree Map view of infected IPs:
https://dashboard.shadowserver.org/statistics/combined/tree/?date_range=1&source=compromised_iot&source=compromised_website&source=compromised_website6&tag=clickfix&data_set=count&scale=log&auto_update=on