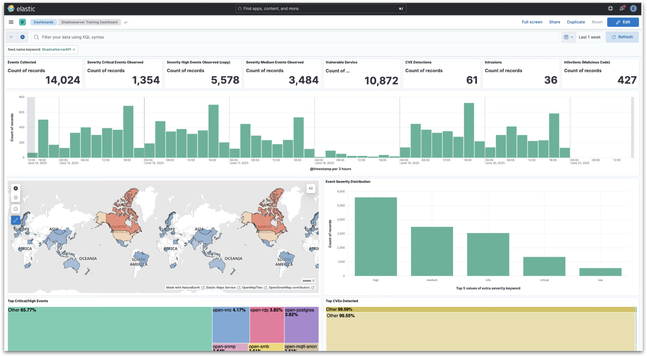
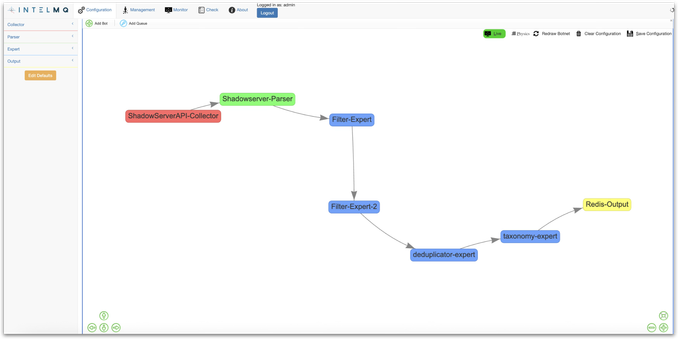
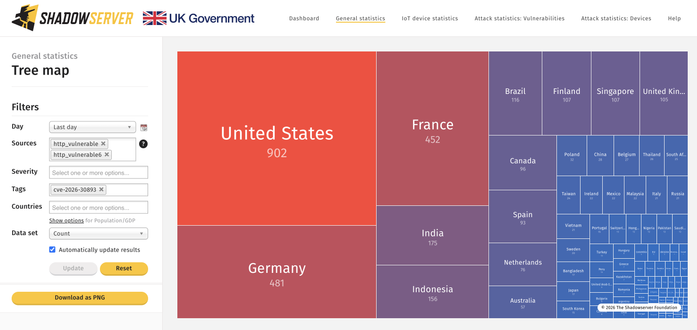
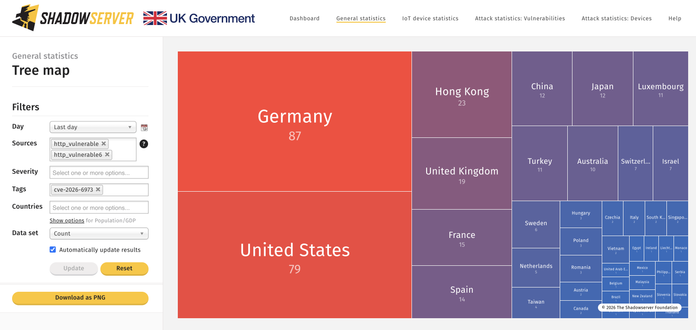
We published a "Shadowserver-in-a-box" platform based on IntelMQ + ELK that can ingest, process and visualize our threat/vulnerability/victim data feeds. Available as a VM or Docker image for free download. Use it for training or in production!
https://github.com/The-Shadowserver-Foundation/training
For usage, you need to request a test API key (or you can use your production API key if you have one already). Please send requests via https://www.shadowserver.org/contact/
Test API key provides access to test/dummy data.
“Shadowserver-in-a-box” development was supported by the cyber capacity building project under the ECOWAS-G7 partnership for cybersecurity, the “Joint Platform for Advancing Cyber Security” (JPAC) in West Africa.
The project was launched by the ECOWAS Commission in collaboration with Germany’s G7 presidency in 2022, commissioned by the German Federal Foreign Office & the European Union Commission in 2023 & implemented by Deutsche Gesellschaft für Internationale Zusammenarbeit (GIZ) GmbH.