The slides I presented last Saturday at Barbhack are available here: https://www.fortiguard.com/events/6189/barb-hack-2025-decompile-linux-malware-with-r2ai
I've already presented on r2ai. What's new here is (1) the analysis of a complex ransomware such as Linux/Trigona, and (2) learn to tweak context size, output token limits etc to get the best out of your LLM.
Enjoy!
NB. One of the demos is available here: https://asciinema.org/a/pBPEaJhp6cunWSKFpBUDTgPt4
Publications | FortiGuard Labs
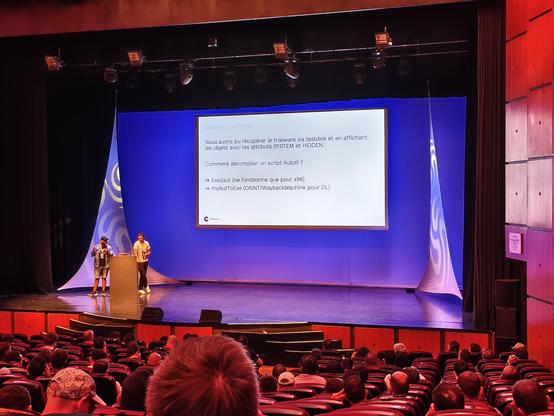
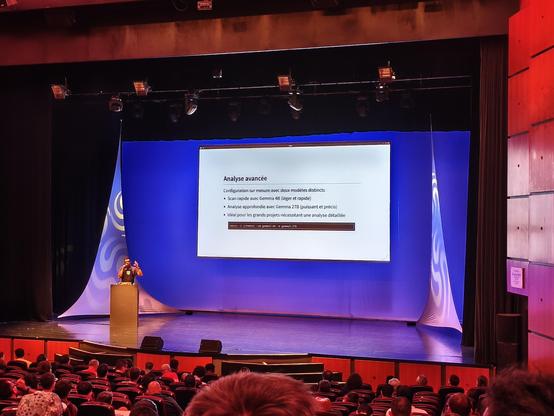
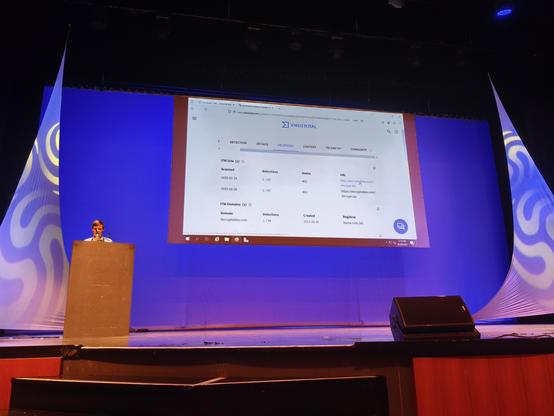
<p>This talk presents 2 different Linux malware:</p><ul><li><p>a shellcode, named Linux/Shellcode_ConnectBack.H!tr. The binary is small and compact, but traditional disassemblers like Ghidra fail to produce understandable decompiled code. With AI assistance in Radare 2, we manage to get far better code. There are few things to fix in the code though.</p></li><li><p>a ransomware, named Linux/Trigona. This binary is bigger and more complex. We analyze with AI, but there are several technical issues due to its size, because the AI context is too big. We show how to workaround the issue, by configuration of r2ai, adequate choice of model, different prompts and different approaches.</p></li></ul>