🌍 OnlyHuman
OnlyHuman is a filter list for uBlock Origin that blocks low-effort AI content farms and SEO spam websites from appearing in your search results and feeds.
🎯 What does it block?
OnlyHuman specifically targets:
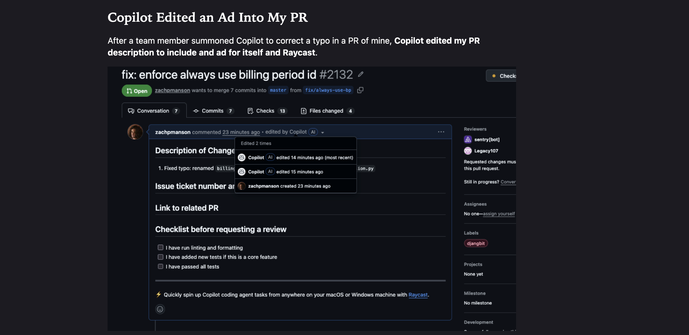
- AI-SEO content farms, websites designed to rank for search queries by mass-producing low-effort AI rewrites.
- Thin SEO sites, pages with thousands of words saying nothing, purely optimized for search algorithms.
- Spun content and rewrites, identical articles regurgitated across multiple domains.
- Search result spam, low-quality sites that flood Google, Bing, DuckDuckGo, Yandex with filler content.
If it's a website built purely to exploit search engines with AI-generated fluff, it gets blocked.
⚙️ How to install
Install uBlock Origin.
Go to "Filter lists" → "Import" and paste this URL:
https://raw.githubusercontent.com/FranklyRocks/OnlyHuman/refs/heads/main/list.txt
Apply changes.
Enjoy cleaner search results.
#ai #ublock #adware