https://www.reddit.com/r/opnsense/comments/1rz0cwm/urgent_support_retirement_for_mongodb_and/
https://www.reddit.com/r/opnsense/comments/1rz0cwm/urgent_support_retirement_for_mongodb_and/
So about 4 days ago I deployed my #OPNsense #Router🥳️
It would have been sooner
if OPNsense would update their old ass Docs😒🙄
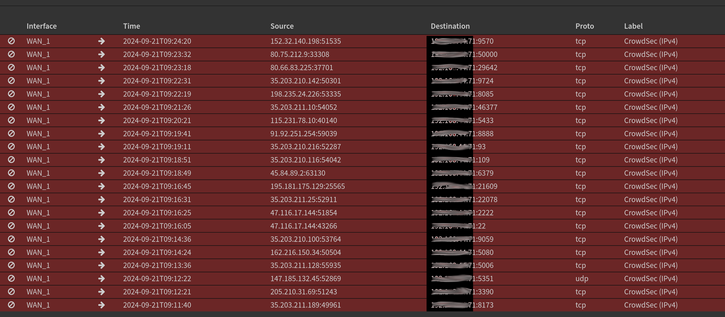
It's running like a dream, I got #Suricata on the WAN running loads of Rule-sets under my policies & I got #Zenarmor running on the LAN as Free User but I'm trying 15 day trial for Home User.
I feel OPNsense Dev's are moving too fast & over looking many little things that do matter.
Also the interface to Suricata is bad vs #Firewall Live View🙄
I read a lot of #CyberSecurity #News and when I read about #Malware I'm see an increasing trend in #Telegram and #Discord often being used for command and control (C2) operations, data exfiltration and more.
This is happening so much I feel if you don't use them block them!!!
Block there domain-names & make firewall rules.
If you use #Zenarmor there are profiles already made to block just them.
#CyberSecurityTips #CyberSecurityNews #Telegram #Discord #Malware
I really hate the assholery out there on the #interwebs. If it weren’t for #fail2ban, I’d be facing even more aggressive daily denials of service attacks. I get these periods of times where shit slows down to a crawl and I get these random attacks. I’m almost certain that they’re happening on the SSH and WireGuard ports. Yes, changing the SSH port to a non-standard port does help some and I think I am going to do that when I get home to mitigate this somewhat. But it will be only a matter of time before a port scanner discovers the new SSH port and alerts the bots to the new port. I’m sure that the bots are also trying to attack WireGuard. WireGuard is damn near impossible so the bots are simply just trying to be assholes for the sake of breaking #Mastodon.
It wouldn’t surprise me if the Twitter, X, or whatever flavor of the month fuckers were behind it. WireGuard keeps no logs so I have no idea. I’d have to do a #wireshark and see what IP addresses are trying to break WireGuard. Bottom line is I think I need some more advanced routing capabilities.
I may look into adding #ZenArmor to my defensive tools. ZenArmor offers deep packet inspection. This would allow a little bit smarter blocking of the bots based on their traffic signatures. This way I whatever gets through the geoblocking, could potentially get nailed by ZenArmor. Then what gets missed by ZenArmor will get cleaned up by fail2ban. I’ll have to see how difficult ZenArmor is to configure. If it’s going to be a bitch, I’ll replace #AlmaLinux on my VPS with #OPNsense, a true router/firewall.
So here is my new #OPNsense Router.
My old router is a #Linksys WRT3200ACM running #DDWRT & it's blue, so I called it #Tachikoma from #GhostInTheShell.
So went with the same theme here.
I am really happy with it😁.
I'm still getting for feel for OPNsense & where everything is
I've been playing with Suricata & I got Zenarmor installed.
For more info about my network setup & more Pic's
Click The Link: https://pcpartpicker.com/b/sK3ypg
#Intel #OPNsense #Firewall #Router #Suricata #Zenarmor #FreeBSD #InFoSec
WoW OPNsense is cool but crazy deep.
It's going to take a little time for me to learn OPNsense, so I will not be using it just yet.
I'm also finding out how little I know about FreeBSD.
I have played with #FreeBSD & #NetBSD here & there over many years but I never ran any BSD on my systems(Last time I was on a FreeBSD system was 2013).
Yes FreeBSD people this is where you LOL at the #Linux guy🐧
I plan to run #Suricata & #Zenarmor
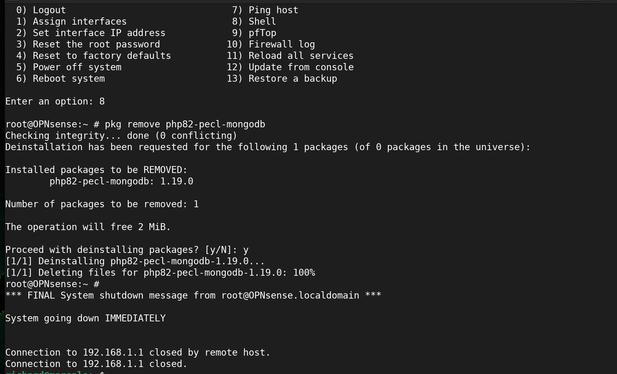
@tux Die Fehlermeldung ist nun verschwunden. Ich habe mich über die Konsole in die #OPNsense eingeloggt und als Root in der Shell den Befehl `pkg remove php82-pecl-mongodb` ausgeführt – mit Erfolg.
Ein Hinweis zur Ursache: Bei der damaligen Installation von ZENamor wurde das Paket `php82-pecl-mongodb` über `pkg` nachinstalliert.
Quelle Link: https://forum.opnsense.org/index.php?topic=45472.0