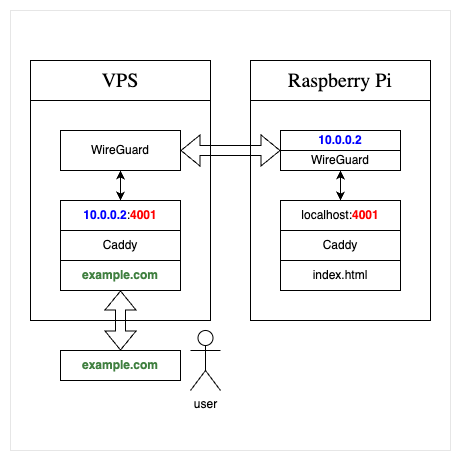
Im Grunde benötige ich kein Reverse #Proxy um Dienste entsprechend öffentlich zu machen ist für meinen Spaß unnötig. Es geht auch per #Wireguard. Damit wird auch die Sicherheit meiner sensiblen Daten erhöht.
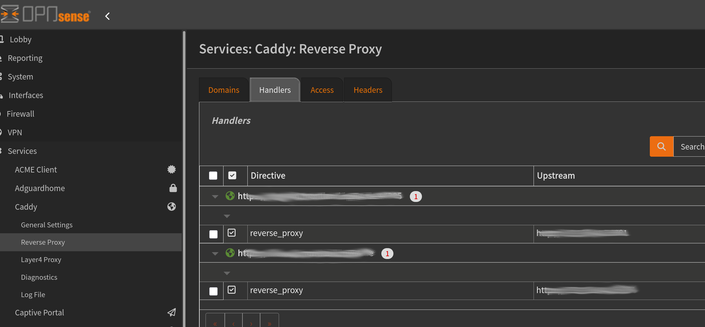
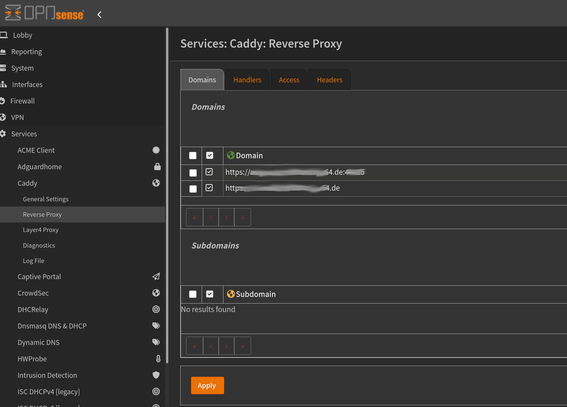
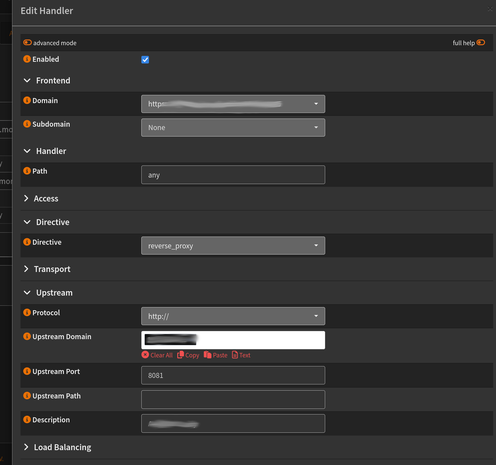
Trotzdem versuche ich dazu zulernen und diesmal ist #Caddy als #OPNsense #Plugin mein neues Tool. Als Proxy eine #DynDNS Adresse und lokal gebunden. Der externe Zugriff dann per Wireguard.