🦖Day 90 of the @velocidex #velociraptor #ArtifactsOfAutumn series
Artifact: Exchange.MacOS.UnifiedLogHunter
Link:
https://docs.velociraptor.app/exchange/artifacts/pages/macos.unifiedloghunter
----
With macOS 10.12 (Sierra) came a new way to log system events in a more centralized, unified fashion -- Unified Logs.
Read more here:
https://devstreaming-cdn.apple.com/videos/wwdc/2016/721wh2etddp4ghxhpcg/721/721_unified_logging_and_activity_tracing.pdf
These logs can be of great importance to investigators searching for artifacts of adversary activity.
----
@crowdstrike , @Mandiant, and others have done a great job covering the usefulness and technical details surrounding the Unified Logging system.
https://www.crowdstrike.com/blog/how-to-leverage-apple-unified-log-for-incident-response/
https://www.mandiant.com/resources/blog/reviewing-macos-unified-logs
----
This artifact is a wrapper around the 'log' command, allowing defenders to easily review events from the logs from the many subsystems of the Unified Logging infrastructure.
It provides the ability to search using a custom or pre-defined filter, and is great for live hunting.
----
If you are looking to collect only raw files and parse them later, or for a third party tool to process the data, check out the Exchange.MacOS.UnifiedLogParser artifact.
https://docs.velociraptor.app/exchange/artifacts/pages/macos.unifiedlogparser/
----
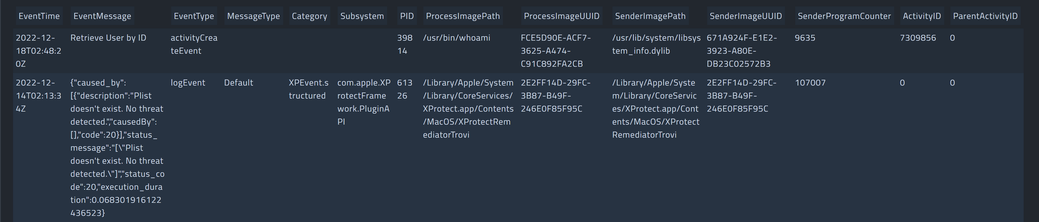
This information provided by this artifact includes:
- Event time/message/type
- Message type
- Category
- Subsystem
- PID
- Process image Path/UUID
- Sender image Path/UUID
- Sender program counter
- Activity ID
- Parent activity ID
----
That's it for now! Stay tuned to learn about more artifacts! 🦖
#DFIR
#Forensics
#Infosec
#macOS
#ThreatHunting
#UnifiedLogs