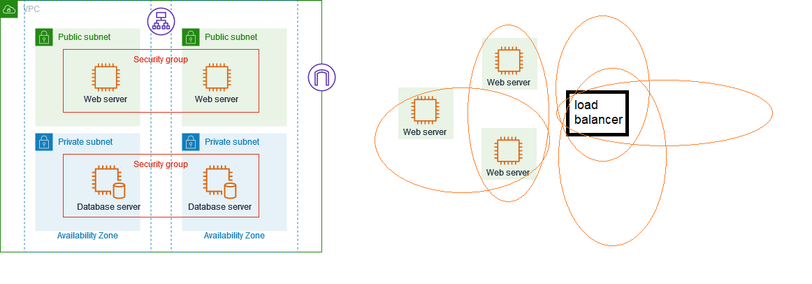
I'm perpetually confused by #aws security groups, which act both as access control rules *and* an identifier for a source of traffic.
For example, you can attach multiple security group to a load balancer, and my understanding is that the result is the union of the permissions.
But when you want to permit traffic from that load balancer to your instance, the load balancer's #SecurityGroup is the "source" for a rule in the instance security group.
But if the load balancer has three groups A, B, and C, are any of them usable as the source? My reading of https://docs.aws.amazon.com/vpc/latest/userguide/security-group-rules.html#security-group-referencing suggests "yes" -- any resource associated with the source security group can use that rule.
The pictures in the documentation look all nice and neat and hierarchal, when in real life it seems it is always a horrible mess, particularly when you let Kubernetes start creating things for you.
I think the thing that is more surprising to me is that the security group view does not give you any way of finding what is in it! You have to go to the "network interfaces" tab and filter by service group there, then look at the descriptions of each to see what it belongs to.
(So the real members of a security group are network interfaces? I'm pretty sure you can set up different ENIs attached to the same instance in different security groups, but that seems glossed over a lot in the UI.)
Frankly, I think this is an incredible muddle and I'm wondering if other cloud providers do better.


 DevelopersIO
DevelopersIO